概要
Cisco ASAvを使用してOCI IPSecにVPN接続する設定例です。
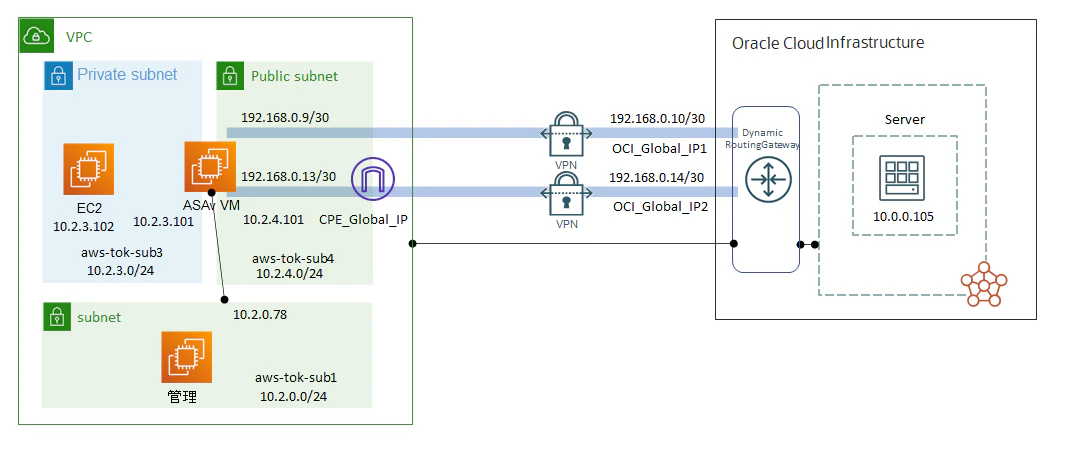
構成
設定例(Static)
- OCI
OCIメニューからネットワーキング>>顧客接続性>>サイト間VPNを選択します。
作成については以下のサイトをご参照ください。
サイト間VPNの設定
https://docs.oracle.com/ja-jp/iaas/Content/Network/Tasks/settingupIPsec.htm
CPE構成 Cisco ASA: ルートベース
https://docs.oracle.com/ja-jp/iaas/Content/Network/Reference/ciscoasaCPEroutebased.htm#Cisco_ASA_RouteBased
ここでは作成済みの設定となります。
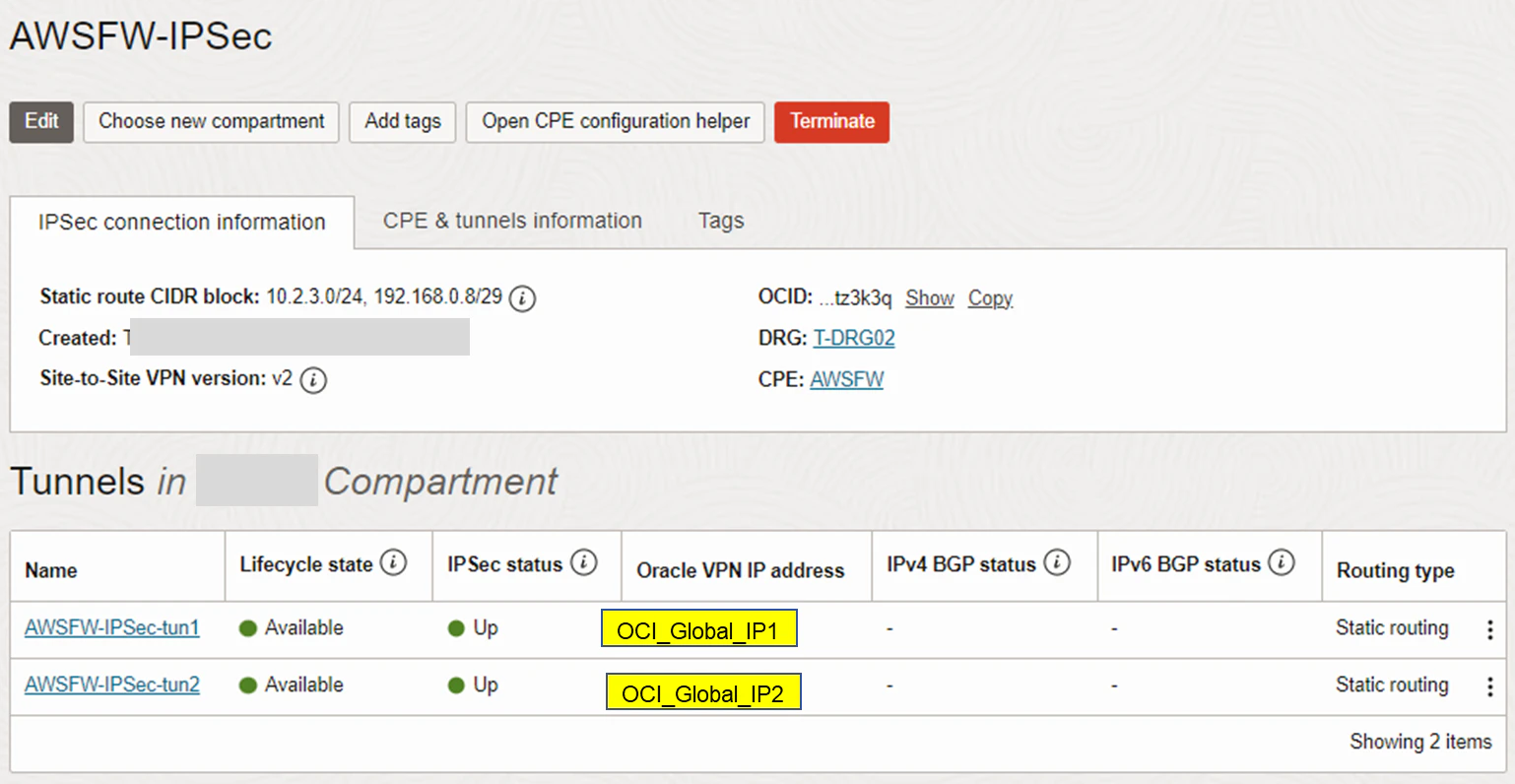
ネットワーキング>>顧客接続性>>サイト間VPN>>作成したVPN
CPE IKE IDはGlobal IPではなくASAvのOutside側のPrivateIPを設定します
(ASAv側でIKE IDを個別指定できないため)
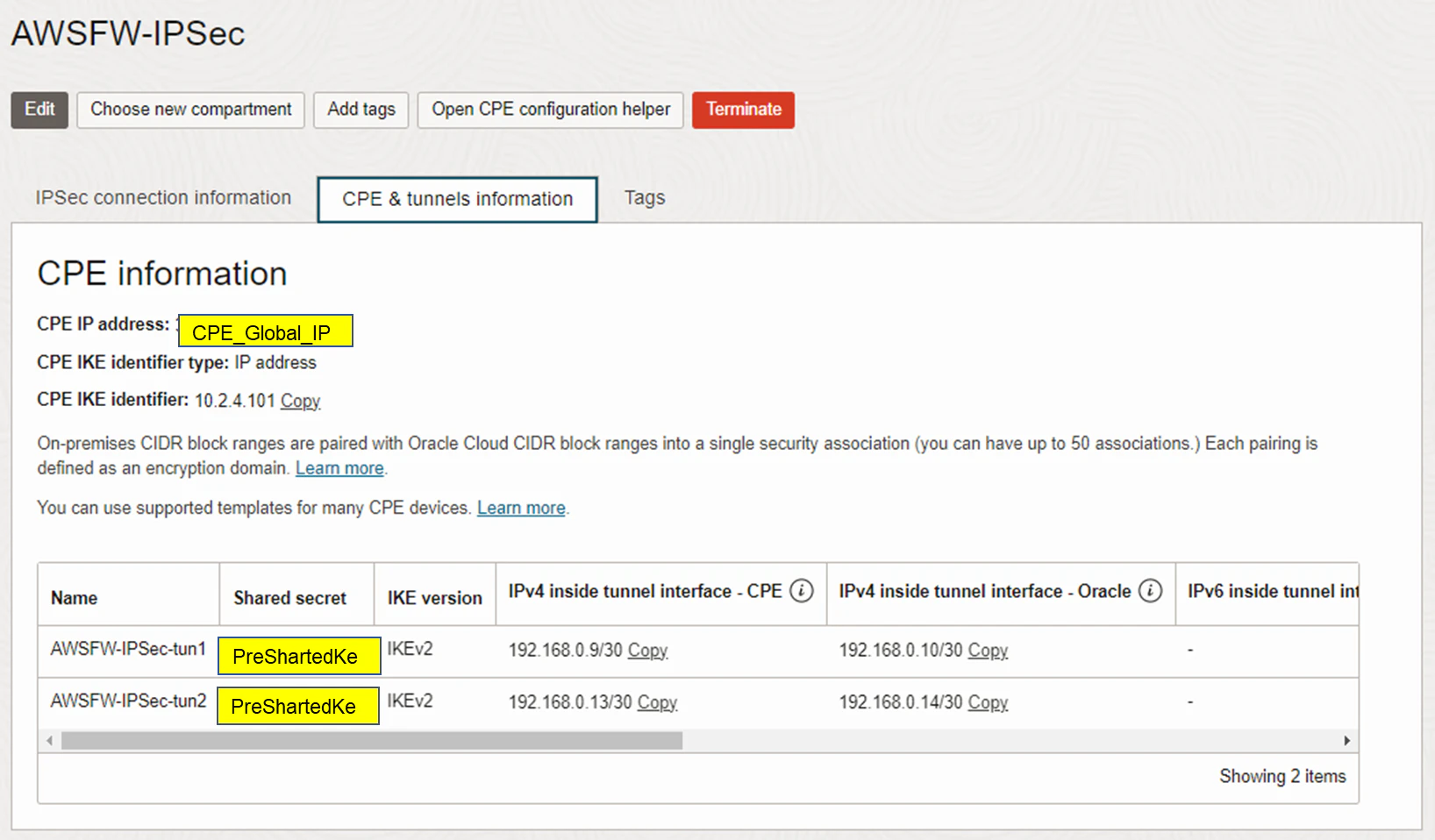
ネットワーキング>>顧客接続性>>サイト間VPN>>作成したVPN>>トンネル1

ネットワーキング>>顧客接続性>>サイト間VPN>>作成したVPN>>トンネル2

- ASAv
AWS MarketplaceからASAvを利用しました。
Software Versionは9.19(1)です。
作成については以下のサイトをご参照ください。
CPE構成 Cisco ASA: ルートベース
https://docs.oracle.com/ja-jp/iaas/Content/Network/Reference/ciscoasaCPEroutebased.htm#Cisco_ASA_RouteBased
ここでは作成済みの設定となります。
: Saved
:
: Serial Number: ******
: Hardware: ASAv, 4096 MB RAM, CPU Xeon 4100/6100/8100 series 3600 MHz, 1 CPU (2 cores)
:
ASA Version 9.19(1)
!
hostname ciscoasa
enable password ***** pbkdf2
service-module 0 keepalive-timeout 4
service-module 0 keepalive-counter 6
names
no mac-address auto
!
interface Management0/0
no management-only
nameif management
security-level 100
ip address dhcp setroute
!
interface TenGigabitEthernet0/0
description outside
nameif outside
security-level 0
ip address 10.2.4.101 255.255.255.0
!
interface TenGigabitEthernet0/1
description inside
nameif inside
security-level 100
ip address 10.2.3.101 255.255.255.0
!
interface Tunnel0
nameif ORACLE-VPN1
ip address 192.168.0.9 255.255.255.252
tunnel source interface outside
tunnel destination 【OCI_Global_IP1】
tunnel mode ipsec ipv4
tunnel protection ipsec profile oracle-vcn-vpn-policy
!
interface Tunnel1
nameif ORACLE-VPN2
ip address 192.168.0.13 255.255.255.252
tunnel source interface outside
tunnel destination 【OCI_Global_IP2】
tunnel mode ipsec ipv4
tunnel protection ipsec profile oracle-vcn-vpn-policy
!
ftp mode passive
no object-group-search access-control
access-group acl-out in interface outside
access-group acl-in in interface inside
access-list acl-in extended permit ip 10.2.3.0 255.255.255.0 10.0.0.0 255.255.255.128
access-list acl-in extended permit ip 10.2.3.0 255.255.255.0 192.168.0.8 255.255.255.248
access-list acl-in extended deny ip any4 any4
access-list acl-out extended permit ip 10.0.0.0 255.255.255.128 10.2.3.0 255.255.255.0
access-list acl-out extended permit ip 10.0.0.0 255.255.255.128 192.168.0.8 255.255.255.248
access-list acl-out extended deny ip any4 any4
no pager
logging enable
logging buffered debugging
mtu management 1500
mtu outside 1500
mtu inside 1500
no failover
no failover wait-disable
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
arp rate-limit 8192
!
route-map prependout permit 10
set as-path prepend 64512
!
route-map prependin permit 10
set as-path prepend 31898
!
route ORACLE-VPN1 10.0.0.0 255.255.255.128 192.168.0.10 1
route ORACLE-VPN2 10.0.0.0 255.255.255.128 192.168.0.14 100
route outside 【OCI_Global_IP2】 255.255.255.255 10.2.4.1 1
route outside 【OCI_Global_IP1】 255.255.255.255 10.2.4.1 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
timeout conn-holddown 0:00:15
timeout igp stale-route 0:01:10
user-identity default-domain LOCAL
aaa authentication ssh console LOCAL
aaa authentication login-history
no snmp-server location
no snmp-server contact
sysopt connection tcpmss 1300
crypto ipsec ikev2 ipsec-proposal oracle_v2_ipsec_proposal
protocol esp encryption aes-gcm-256
protocol esp integrity null
crypto ipsec profile oracle-vcn-vpn-policy
set ikev2 ipsec-proposal oracle_v2_ipsec_proposal
set pfs group5
set security-association lifetime seconds 3600
crypto ipsec security-association pmtu-aging infinite
crypto ca trustpoint _SmartCallHome_ServerCA
no validation-usage
crl configure
crypto ca trustpoint _SmartCallHome_ServerCA2
no validation-usage
crl configure
crypto ca trustpool policy
auto-import
crypto ca certificate chain _SmartCallHome_ServerCA
certificate ca *****
quit
crypto ca certificate chain _SmartCallHome_ServerCA2
certificate ca 0509
*****
quit
crypto ikev2 policy 10
encryption aes-256
integrity sha384
group 20
prf sha384
lifetime seconds 28800
crypto ikev2 enable outside
telnet timeout 5
ssh stack ciscossh
ssh stricthostkeycheck
ssh timeout 30
ssh key-exchange group dh-group14-sha256
ssh 0.0.0.0 0.0.0.0 management
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
group-policy oracle_v2_group_policy internal
group-policy oracle_v2_group_policy attributes
vpn-tunnel-protocol ikev2
dynamic-access-policy-record DfltAccessPolicy
username admin password ***** pbkdf2 privilege 15
username admin attributes
service-type admin
ssh authentication publickey ***** hashed
tunnel-group 【OCI_Global_IP1】 type ipsec-l2l
tunnel-group 【OCI_Global_IP1】 general-attributes
default-group-policy oracle_v2_group_policy
tunnel-group 【OCI_Global_IP1】 ipsec-attributes
ikev2 remote-authentication pre-shared-key 【PreSharedKey】
ikev2 local-authentication pre-shared-key 【PreSharedKey】
tunnel-group 【OCI_Global_IP2】 type ipsec-l2l
tunnel-group 【OCI_Global_IP2】 general-attributes
default-group-policy oracle_v2_group_policy
tunnel-group 【OCI_Global_IP2】 ipsec-attributes
ikev2 remote-authentication pre-shared-key 【PreSharedKey】
ikev2 local-authentication pre-shared-key 【PreSharedKey】
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns migrated_dns_map_1
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
policy-map global_policy
class inspection_default
inspect dns migrated_dns_map_1
inspect ftp
inspect h323 h225
inspect h323 ras
inspect ip-options
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect icmp
policy-map type inspect dns migrated_dns_map_2
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
!
service-policy global_policy global
prompt hostname context
no call-home reporting anonymous
call-home
profile License
destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService
destination transport-method http
profile CiscoTAC-1
no active
destination address http https://tools.cisco.com/its/service/oddce/services/DDCEService
destination address email callhome@cisco.com
destination transport-method http
subscribe-to-alert-group diagnostic
subscribe-to-alert-group environment
subscribe-to-alert-group inventory periodic monthly
subscribe-to-alert-group configuration periodic monthly
subscribe-to-alert-group telemetry periodic daily
Cryptochecksum:a5b7b15cc615bd5840d517808f9701a1
: end
IPSec状況
ciscoasa(config)# show crypto ikev2 sa
IKEv2 SAs:
Session-id:20, Status:UP-ACTIVE, IKE count:1, CHILD count:1
Tunnel-id Local Remote fvrf/ivrf Status Role
2037529709 10.2.4.101/4500 【OCI_Global_IP2】/4500 Global/Global READY INITIATOR
Encr: AES-CBC, keysize: 256, Hash: SHA384, DH Grp:20, Auth sign: PSK, Auth verify: PSK
Life/Active Time: 28800/494 sec
Child sa: local selector 0.0.0.0/0 - 255.255.255.255/65535
remote selector 0.0.0.0/0 - 255.255.255.255/65535
ESP spi in/out: 0x4b555613/0x4a10a23e
IKEv2 SAs:
Session-id:19, Status:UP-ACTIVE, IKE count:1, CHILD count:1
Tunnel-id Local Remote fvrf/ivrf Status Role
2308983409 10.2.4.101/4500 【OCI_Global_IP1】/4500 Global/Global READY INITIATOR
Encr: AES-CBC, keysize: 256, Hash: SHA384, DH Grp:20, Auth sign: PSK, Auth verify: PSK
Life/Active Time: 28800/616 sec
Child sa: local selector 0.0.0.0/0 - 255.255.255.255/65535
remote selector 0.0.0.0/0 - 255.255.255.255/65535
ESP spi in/out: 0xb3bcf42e/0x6733a74e
ciscoasa(config)# show crypto ips sa
interface: ORACLE-VPN1
Crypto map tag: __vti-crypto-map-Tunnel0-0-0, seq num: 65280, local addr: 10.2.4.101
Protected vrf (ivrf): Global
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
current_peer: 168.138.223.77
#pkts encaps: 636, #pkts encrypt: 636, #pkts digest: 636
#pkts decaps: 551, #pkts decrypt: 551, #pkts verify: 551
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 636, #pkts comp failed: 0, #pkts decomp failed: 0
#pre-frag successes: 0, #pre-frag failures: 0, #fragments created: 0
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
#TFC rcvd: 0, #TFC sent: 0
#Valid ICMP Errors rcvd: 0, #Invalid ICMP Errors rcvd: 0
#send errors: 0, #recv errors: 0
local crypto endpt.: 10.2.4.101/4500, remote crypto endpt.: 【OCI_Global_IP1】/4500
path mtu 1500, ipsec overhead 63(44), media mtu 1500
PMTU time remaining (sec): 0, DF policy: copy-df
ICMP error validation: disabled, TFC packets: disabled
current outbound spi: 6733A74E
current inbound spi : B3BCF42E
inbound esp sas:
spi: 0xB3BCF42E (3015504942)
SA State: active
transform: esp-aes-gcm-256 esp-null-hmac no compression
in use settings ={L2L, Tunnel, NAT-T-Encaps, PFS Group 5, IKEv2, VTI, }
slot: 0, conn_id: 167, crypto-map: __vti-crypto-map-Tunnel0-0-0
sa timing: remaining key lifetime (kB/sec): (4239304/2984)
IV size: 8 bytes
replay detection support: Y
Anti replay bitmap:
0xFFFFFFFF 0xFFFFFFFF
outbound esp sas:
spi: 0x6733A74E (1731438414)
SA State: active
transform: esp-aes-gcm-256 esp-null-hmac no compression
in use settings ={L2L, Tunnel, NAT-T-Encaps, PFS Group 5, IKEv2, VTI, }
slot: 0, conn_id: 167, crypto-map: __vti-crypto-map-Tunnel0-0-0
sa timing: remaining key lifetime (kB/sec): (4285384/2984)
IV size: 8 bytes
replay detection support: Y
Anti replay bitmap:
0x00000000 0x00000001
interface: ORACLE-VPN2
Crypto map tag: __vti-crypto-map-Tunnel1-0-1, seq num: 65280, local addr: 10.2.4.101
Protected vrf (ivrf): Global
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
current_peer: 168.138.219.128
#pkts encaps: 30, #pkts encrypt: 30, #pkts digest: 30
#pkts decaps: 24, #pkts decrypt: 24, #pkts verify: 24
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 30, #pkts comp failed: 0, #pkts decomp failed: 0
#pre-frag successes: 0, #pre-frag failures: 0, #fragments created: 0
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
#TFC rcvd: 0, #TFC sent: 0
#Valid ICMP Errors rcvd: 0, #Invalid ICMP Errors rcvd: 0
#send errors: 0, #recv errors: 0
local crypto endpt.: 10.2.4.101/4500, remote crypto endpt.: 【OCI_Global_IP2】/4500
path mtu 1500, ipsec overhead 63(44), media mtu 1500
PMTU time remaining (sec): 0, DF policy: copy-df
ICMP error validation: disabled, TFC packets: disabled
current outbound spi: 4A10A23E
current inbound spi : 4B555613
inbound esp sas:
spi: 0x4B555613 (1263883795)
SA State: active
transform: esp-aes-gcm-256 esp-null-hmac no compression
in use settings ={L2L, Tunnel, NAT-T-Encaps, PFS Group 5, IKEv2, VTI, }
slot: 0, conn_id: 170, crypto-map: __vti-crypto-map-Tunnel1-0-1
sa timing: remaining key lifetime (kB/sec): (4331518/3106)
IV size: 8 bytes
replay detection support: Y
Anti replay bitmap:
0x00000000 0x01FFFFFF
outbound esp sas:
spi: 0x4A10A23E (1242604094)
SA State: active
transform: esp-aes-gcm-256 esp-null-hmac no compression
in use settings ={L2L, Tunnel, NAT-T-Encaps, PFS Group 5, IKEv2, VTI, }
slot: 0, conn_id: 170, crypto-map: __vti-crypto-map-Tunnel1-0-1
sa timing: remaining key lifetime (kB/sec): (4101117/3106)
IV size: 8 bytes
replay detection support: Y
Anti replay bitmap:
0x00000000 0x00000001
- Pingテスト
AWSサーバーからOCIサーバーへのping結果
Server.
[ec2-user@ip-10-2-3-102 ~]$ ping 10.0.0.105
PING 10.0.0.105 (10.0.0.105) 56(84) bytes of data.
64 bytes from 10.0.0.105: icmp_seq=1 ttl=61 time=4.72 ms
64 bytes from 10.0.0.105: icmp_seq=2 ttl=61 time=4.26 ms
64 bytes from 10.0.0.105: icmp_seq=3 ttl=61 time=4.50 ms
64 bytes from 10.0.0.105: icmp_seq=4 ttl=61 time=4.50 ms
64 bytes from 10.0.0.105: icmp_seq=5 ttl=61 time=4.52 ms
^C
--- 10.0.0.105 ping statistics ---
5 packets transmitted, 5 received, 0% packet loss, time 4006ms
rtt min/avg/max/mdev = 4.260/4.503/4.725/0.170 ms
[ec2-user@ip-10-2-3-102 ~]$
OCIサーバーからAWSサーバーへのping結果
Server.
[opc@t-vm10-0-0-105 ~]$ ping 10.2.3.102
PING 10.2.3.102 (10.2.3.102) 56(84) bytes of data.
64 bytes from 10.2.3.102: icmp_seq=1 ttl=253 time=4.96 ms
64 bytes from 10.2.3.102: icmp_seq=2 ttl=253 time=4.09 ms
64 bytes from 10.2.3.102: icmp_seq=3 ttl=253 time=4.29 ms
64 bytes from 10.2.3.102: icmp_seq=4 ttl=253 time=4.00 ms
^C
--- 10.2.3.102 ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 3003ms
rtt min/avg/max/mdev = 4.002/4.334/4.960/0.381 ms
設定例(BGP)
Static route設定を以下のように変更します
【OCI】
- ネットワーキング>>顧客接続性>>サイト間VPN>>作成したVPN>>トンネル1を編集しルーティングをBGPに変更
- ネットワーキング>>顧客接続性>>サイト間VPN>>作成したVPN>>トンネル2を編集しルーティングをBGPに変更
- ネットワーキング>>顧客接続性>>サイト間VPN>>作成したVPNを編集しオンプレミス・ネットワークへのルートに設定したStatic Routeを削除
【vSRX】
- OCI VCN向けのStatic routeを削除
route ORACLE-VPN1 10.0.0.0 255.255.255.128 192.168.0.10 1
route ORACLE-VPN2 10.0.0.0 255.255.255.128 192.168.0.14 100
- BGPを追加
トンネル1を優先するためにトンネル2のBGPに対してAS Path prependでルートを付加する設定を追加しています
route-map prependout permit 10
set as-path prepend 64512
!
route-map prependin permit 10
set as-path prepend 31898
!
router bgp 64512
bgp log-neighbor-changes
address-family ipv4 unicast
neighbor 192.168.0.10 remote-as 31898
neighbor 192.168.0.10 activate
neighbor 192.168.0.14 remote-as 31898
neighbor 192.168.0.14 activate
neighbor 192.168.0.14 route-map prependin in
neighbor 192.168.0.14 route-map prependout out
network 10.2.3.0 mask 255.255.255.0
no auto-summary
no synchronization
exit-address-family
!
BGP確認
ciscoasa# sh route
BGPのみ
B 10.0.0.0 255.255.255.128 [20/0] via 192.168.0.10, 00:20:04
B 10.0.0.128 255.255.255.224 [20/0] via 192.168.0.10, 00:20:04
ciscoasa# sh bgp
BGP table version is 10, local router ID is 192.168.0.13
Status codes: s suppressed, d damped, h history, * valid, > best, i - internal,
r RIB-failure, S Stale, m multipath
Origin codes: i - IGP, e - EGP, ? - incomplete
Network Next Hop Metric LocPrf Weight Path
* 10.0.0.0/25 192.168.0.14 0 31898 31898 i
*> 192.168.0.10 0 31898 i
* 10.0.0.128/27 192.168.0.14 0 31898 31898 i
*> 192.168.0.10 0 31898 i
*> 10.2.3.0/24 0.0.0.0 0 32768 i
ciscoasa#
- Pingテスト
AWSサーバーからOCIサーバーへのping結果
Server.
[ec2-user@ip-10-2-3-102 ~]$ ping 10.0.0.105
PING 10.0.0.105 (10.0.0.105) 56(84) bytes of data.
64 bytes from 10.0.0.105: icmp_seq=1 ttl=61 time=5.56 ms
64 bytes from 10.0.0.105: icmp_seq=2 ttl=61 time=5.61 ms
64 bytes from 10.0.0.105: icmp_seq=3 ttl=61 time=5.50 ms
64 bytes from 10.0.0.105: icmp_seq=4 ttl=61 time=5.57 ms
^C
--- 10.0.0.105 ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 3004ms
rtt min/avg/max/mdev = 5.509/5.564/5.613/0.064 ms
OCIサーバーからAWSサーバーへのping結果
Server.
[opc@t-vm10-0-0-105 ~]$ ping 10.2.3.102
PING 10.2.3.102 (10.2.3.102) 56(84) bytes of data.
64 bytes from 10.2.3.102: icmp_seq=1 ttl=253 time=5.09 ms
64 bytes from 10.2.3.102: icmp_seq=2 ttl=253 time=5.05 ms
64 bytes from 10.2.3.102: icmp_seq=3 ttl=253 time=5.37 ms
64 bytes from 10.2.3.102: icmp_seq=4 ttl=253 time=5.14 ms
^C
--- 10.2.3.102 ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 3004ms
rtt min/avg/max/mdev = 5.053/5.163/5.368/0.122 ms
[opc@t-vm10-0-0-105 ~]$