こんにちは、ひろかずです。
前回、Deep Security ~ AWS WAF連携ツールを評価しましたが、DSaaSに対する連携という制限が付いていました。
2016年2月20日にアップデートされ、インスタンスに構築したDeep Security Manager(以下、個別DSM)に対応したとのことなので、一筆書きます。
参考
Githubリポジトリ deep-security/aws-waf
前提
- Deep Security Managerの導入が完了していること。
- ライセンスを投入していること。
- 前回の内容を踏んでいること。
- 前回起動したインスタンスが、連携先Deep Security Managerのポート4119に到達できること。
工程
- Deep Securty ~ AWS WAF連携ツールの更新
- 動作確認
1. Deep Securty ~ AWS WAF連携ツールの更新
前回、a877db1にロールバックしていたので、最新版の0e4712eに更新します。
$ git pull origin master
remote: Counting objects: 20, done.
remote: Total 20 (delta 1), reused 1 (delta 1), pack-reused 19
Unpacking objects: 100% (20/20), done.
From https://github.com/deep-security/aws-waf
* branch master -> FETCH_HEAD
46e3e5b..0e4712e master -> origin/master
Updating a877db1..0e4712e
Fast-forward
:
更新されていますね。
$ ll
合計 20
-rw-rw-r-- 1 ec2-user ec2-user 1081 2月 10 10:08 LICENSE
-rw-rw-r-- 1 ec2-user ec2-user 7060 2月 27 23:48 README.md
drwxrwxr-x 5 ec2-user ec2-user 4096 2月 27 23:48 dsawswaf
-rw-rw-r-- 1 ec2-user ec2-user 33 2月 10 10:08 requirements.txt
念のためにアップデート確認
pipの警告は置いておいて、特にアップデートは不要だったようですね。
$ sudo pip install -r requirements.txt
You are using pip version 6.1.1, however version 8.0.3 is available.
You should consider upgrading via the 'pip install --upgrade pip' command.
Requirement already satisfied (use --upgrade to upgrade): netaddr>=0.7.18 in /usr/local/lib/python2.7/site-packages (from -r requirements.txt (line 1))
Requirement already satisfied (use --upgrade to upgrade): boto3>=1.2.1 in /usr/local/lib/python2.7/site-packages (from -r requirements.txt (line 2))
Requirement already satisfied (use --upgrade to upgrade): jmespath<1.0.0,>=0.7.1 in /usr/lib/python2.7/dist-packages (from boto3>=1.2.1->-r requirements.txt (line 2))
Requirement already satisfied (use --upgrade to upgrade): futures<4.0.0,>=2.2.0 in /usr/local/lib/python2.7/site-packages (from boto3>=1.2.1->-r requirements.txt (line 2))
Requirement already satisfied (use --upgrade to upgrade): botocore<1.4.0,>=1.3.0 in /usr/lib/python2.7/dist-packages (from boto3>=1.2.1->-r requirements.txt (line 2))
Requirement already satisfied (use --upgrade to upgrade): python-dateutil<3.0.0,>=2.1 in /usr/lib/python2.7/dist-packages (from botocore<1.4.0,>=1.3.0->boto3>=1.2.1->-r requirements.txt (line 2))
Requirement already satisfied (use --upgrade to upgrade): docutils>=0.10 in /usr/lib/python2.7/dist-packages (from botocore<1.4.0,>=1.3.0->boto3>=1.2.1->-r requirements.txt (line 2))
Requirement already satisfied (use --upgrade to upgrade): six in /usr/lib/python2.7/dist-packages (from python-dateutil<3.0.0,>=2.1->botocore<1.4.0,>=1.3.0->boto3>=1.2.1->-r requirements.txt (line 2))
2. 動作確認
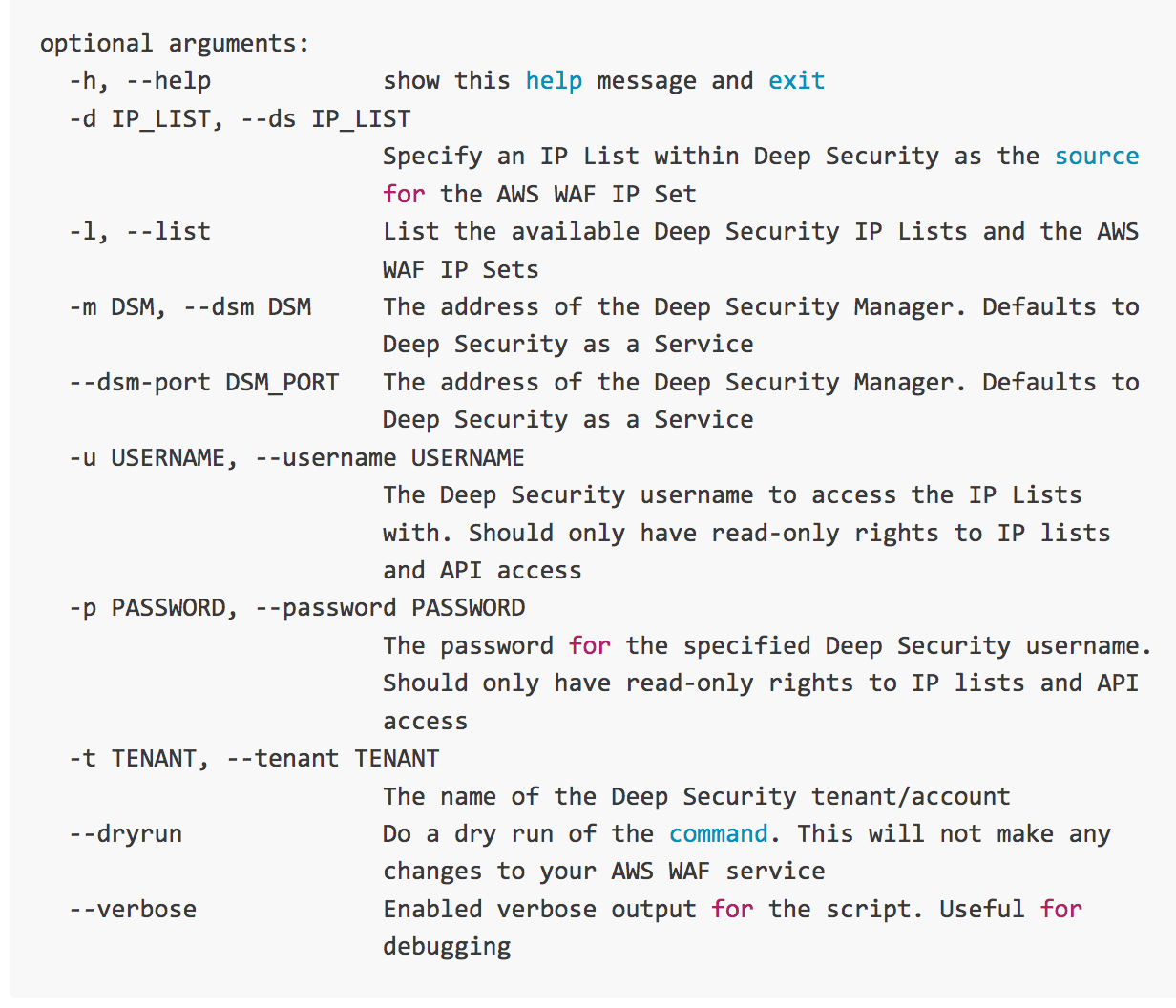
readme.mdを見ると、個別DSMへの連携には -m オプションで対向の個別DSMを指定して、 --dsm-port でポートを指定する必要がありそうですね。
では、実行してみます。
期待値は、前回同様に個別DSMに登録されているIPリストとAWS WAFのCondition(IP List)一覧の表示です。
$ python ip_list_to_set.py --list -m xxx.xxx.xxx.xxx --dsm-port 4119 -u webapi -p xxxxxxxx
Available Deep Security IP Lists
================================
--- No IP lists available
Available AWS WAF IP Sets
=========================
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx test3
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx myIP
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx test2
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx test
そんなもんはねぇ!と言われてしまいました。
ip_list_to_set.py を見ると、以下の引き数処理が追加されています。
parser.add_argument('--ignore-ssl-validation', action='store_true', dest='ignore_ssl_validation', required=False, help='Ignore SSL certification validation. Be careful when you use this as it disables a recommended security check. Required for Deep Security Managers using a self-signed SSL certificate')
そう言えば、個別DSMはデフォルトで自己署名証明書が使用されています。
個別DSMに対しては、このオプションが必要なようですね。
では、もう一度
$ python ip_list_to_set.py --list -m xxx.xxx.xxx.xxx --dsm-port 4119 -u webapi -p xxxxxxxx --ignore-ssl-validation
***********************************************************************
* IGNORING SSL CERTIFICATE VALIDATION
* ===================================
* You have requested to ignore SSL certificate validation. This is a less secure method
* of connecting to a Deep Security Manager (DSM). Please ensure that you have other
* mitigations and security controls in place (like restricting IP space that can access
* the DSM, implementing least privilege for the Deep Security user/role accessing the
* API, etc).
*
* During script execution, you'll see a number of "InsecureRequestWarning" messages.
* These are to be expected when operating without validation.
***********************************************************************
/home/ec2-user/aws-waf/dsawswaf/requests/packages/urllib3/connectionpool.py:789: InsecureRequestWarning: Unverified HTTPS request is being made. Adding certificate verification is strongly advised. See: https://urllib3.readthedocs.org/en/latest/security.html
InsecureRequestWarning)
Available Deep Security IP Lists
================================
1 Ignore Reconnaissance
2 Network Broadcast
3 Ingress Filters
4 Domain Controller(s)
5 Off Domain IPs
6 Corporate Network IPs
7 VPN Tunnel IPs
21 awswaf
Available AWS WAF IP Sets
=========================
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx test3
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx myIP
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx test2
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx test
/home/ec2-user/aws-waf/dsawswaf/requests/packages/urllib3/connectionpool.py:789: InsecureRequestWarning: Unverified HTTPS request is being made. Adding certificate verification is strongly advised. See: https://urllib3.readthedocs.org/en/latest/security.html
InsecureRequestWarning)
なんかすごく警告文がずらずら出ますが、情報は取れましたね。
では、21 awswaf をAWS WAFのConditionに追加しましょう。
まずは、dryrun。
大丈夫そうですね。(自己署名証明書に起因する警告は省略しました)
$ python ip_list_to_set.py -d 21 -m xxx.xxx.xxx.xxx --dsm-port 4119 -u webapi -p xxxxxxxx --ignore-ssl-validation --dryrun
:
***********************************************************************
* DRY RUN ENABLED. NO CHANGES WILL BE MADE
***********************************************************************
Will request the creation of [awswaf]
:
では、実行。
できたみたいですね。
$ python ip_list_to_set.py -d 21 -m xxx.xxx.xxx.xxx --dsm-port 4119 -u webapi -p xxxxxxxx --ignore-ssl-validation
:
Converted 4 IP List entries to 4 IP Set entries
Updated IP Set [awswaf] with ID [xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx]
:
できました。
python ip_list_to_set.py --list -m xxx.xxx.xxx.xxx --dsm-port 4119 -u webapi -p xxxxxxxx --ignore-ssl-validation
:
Available Deep Security IP Lists
================================
1 Ignore Reconnaissance
2 Network Broadcast
3 Ingress Filters
4 Domain Controller(s)
5 Off Domain IPs
6 Corporate Network IPs
7 VPN Tunnel IPs
21 awswaf
Available AWS WAF IP Sets
=========================
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx test3
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx myIP
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx test2
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx test
xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx awswaf ★★★
:
おまけ
Deep Security 側のIPリストに空行が入っていると処理ができないようです。
IPリストは、コメントや空行が入ってないものを使用しましょう。
今日はここまでです。
お疲れ様でした。