以下は CODE BLUE 2020 で発表された「Dissecting China's Information Operations with Threat Intelligence」を試訳したものです。
発表者:Che Chang, Silvia Yeh
発表日:2020年10月29日
目的
CODE BLUE を聴講後、復習をかねて以下の手順で翻訳しました。
- Otter で YouTube の動画(英語版)を音声から文字へ変換
- YouTube の動画の字幕と比較して単語の誤変換を修正
- DeepL と Google Translate で英語から日本語へ翻訳
- YouTube の動画(日本語通訳版)の日本語と比較して翻訳を修正
- 英辞郎で単語や慣用表現を修正
- 翻訳を推敲
講演内容
はじめに
Hello, welcome to join on talk.
こんにちは、本講演へようこそご参加くださいました。
This presentational is about China's Information Operation.
本日のプレゼンテーションは中国の情報操作についてお話しします。

My name is Che Chang.
私は張哲誠(Che Chang)と申します。
And my name is Silvia.
Silvia と申します。
We are the cyber threat analysts from TeamT5 threat intelligence team.
私たちは TeamT5 社の脅威インテリジェンスチームにおいて、サイバー脅威アナリストを担当しています。
In the past 2 years, our threat intelligence about China's Information Operation has helped our partners in government agencies and our clients in various industries to better understand the issue.
この 2 年間、中国の情報操作に関する弊社の脅威インテリジェンス(脅威を低減するために利用できる情報)は、政府機関のパートナーや様々な業界のクライアントがこの問題をより理解するために役立ってきました。
So, without further ado, let's get started.
では、早速(難しい話は抜きにして)、本題に入りましょう。
(以降は事前に録画した内容へ移行)
Hi, Welcome to join TeamT5 presentation about China's Information Operation.
こんにちは、中国の情報操作に関する弊社のプレゼンテーションへようこそご参加くださいました。
Today's topic is "Dissecting China's InfoOps with Threat Intelligence".
本日のトピックは「脅威インテリジェンスによる中国の情報操作の分析」です。
I am Che Chang.
Che Chang(張哲誠)です。
I am the co-author of TeamT5 Information Operation White Paper.
TeamT5 社の「情報操作白書」の共同執筆者です。
I have been focusing on the information operation research and the underground market.
私はこれまで情報操作の研究や地下市場に関して取り組んできました。
In the past few years, I have been the invited speakers of many security conferences.
また、ここ数年は多くのセキュリティカンファレンスの招待講演者を務めてきました。
In the 2020 April, I was invited to be the speaker of a virtual training workshop held by the Taiwanese goverment, the vGCTF, to talk about the COVID-19 disinformation.
2020 年 4 月には、台湾の政府機関である vGCTF(Virtual Global Cooperation and Training Framework)が開催した机上演習ワークショップに講師として招かれ、新型コロナウイルスに関するデマ(意図的な虚偽情報)についてお話をさせていただきました。
I am Silvia Yeh.
Silvia Yeh(Silvia 葉)です。
I am also the co-author of TeamT5's InfoOp White Paper.
私も TeamT5 社の「情報操作白書」の共同執筆者です。
Apart from Information Operation, I also do analysis of cyber policies in Asia Pacific countries.
情報操作以外に、アジア太平洋諸国のサイバー政策の分析も行っています。
概要
Here is the outline today.
では、本日の概要です。

First, we will give a brief introduction about what is Information Operation and why it matters.
まず、情報操作とは何か、なぜ情報操作が重要なのか、について簡単にご説明します。
Then we will have an overview of Taiwan's 2020 general election.
続いて、2020 年の台湾総選挙の概要についてご紹介します。
And starting from Taiwan, we will summarize 3 key methods to see how China is launching its InfoOp on social media.
そして台湾の事例をもとに、中国がソーシャルメディア上でどのように情報操作を展開しているのか 3 つの重要な手法をまとめながら見ていきます。
And last, We will have a Q&A session.
最後に、質疑応答を行います。
So, if you have any question during our talk, please just type in.
講演中にご質問があれば、(EventHub のチャットに)入力してください。
情報操作とは何か
Ok. So, what is Information Operation?
さて、「情報操作」とは何でしょうか?
Information Operation, InfoOp, is also called influence operation or information warfare.
「情報操作(InfoOp)」は「影響力工作」や「情報戦」とも呼ばれます。
The term was first used in the US military, meaning to influence the decision making of the adversary.
この用語は米軍において敵の意思決定に影響を与えるという意味で使用されたのが始まりです。
And in the era of social media, the social media service is now the essential space for all people to exchange ideas and get the new information.
ソーシャルメディアの時代において、ソーシャルメディアサービスは今やあらゆる人たちが意見を交換し、新しい情報を得るために必要不可欠な空間となっています。
After the 2016 Russian interference against the US election, the world has realized the state-sponsored Information Operation could be used through the social media.
2016 年のロシアによる米大統領選挙への干渉を経て、世界は国家主導の情報操作がソーシャルメディアを通じて利用される可能性があることに気づきました。
This authoritarian regimes could use social medias to launch InfoOp to spread propaganda, disinformation and even hate speech.
かの権威主義的な政権(中国)はソーシャルメディアを悪用し、宣伝活動や虚偽情報、さらにはヘイトスピーチを拡散するために、情報操作を展開している可能性があります。
中国の情報操作
China's InfoOp could be categorized into 2 kinds of operations.
中国の情報操作は 2 種類の工作活動(オペレーション)に分類することができます。

First one is the overt operation, meaning the operations are openly conducted and without any concealment.
一つは明白な工作活動であり、工作活動は公然と遂行され、なんら隠蔽されることがないことを意味します。
We can easily identify the overt actors as the agent of the Chinese government like the propaganda and misinformation spread by the Chinese state media and China's diplomats.
中国の国営メディアや外交官によって拡散された宣伝活動や虚偽情報のように、公然のアクター(遂行者)は中国政府のエージェント(工作員)であることが容易に特定できます。
The other one is more tricky.
もう一つの方がより厄介です。
It is a covert operation, meaning the operation cannot be directly attributed to the Chinese government.
こちらは秘密の工作活動であり、中国政府に直接たどりつくことができない工作活動であることを意味します。
The actors of the covert operations will be more aggressive to spread disinformation, conspiracy theories, and even perform doxing campaigns.
秘密工作のアクターはより積極的に虚偽情報や陰謀論を拡散し、さらには組織的な Doxing(個人情報の暴露)活動さえ行っています。
For the past 2 years, in these major events like 2018 Taiwan's local elections, 2019 the Hong Kong pro-democracy protest, 2020 Taiwan's general election, and the COVID-19 pandemic, we all identify China's InfoOp campaigns.
この 2 年間、2018 年の台湾地方選挙、2019 年の香港民主化抗議デモ、2020 年の台湾総選挙と新型コロナウイルスの爆発的な流行といった大きな出来事のなかで、中国の組織的な情報操作活動が存在したことがわかってます。
Our researches have helped the governments, the journalism and the social media platforms and many research institutes in these major events to better understand China's InfoOp's Tactic, Techniques, and Procedures.
これらの大きな出来事のなかで、弊社の研究成果は政府、ジャーナリズム、ソーシャルメディアプラットフォーム、および多くの研究機関に対し、中国の情報操作の TTP(戦術、技術、手順)をより理解するために支援してきました。
And in the past few months, we are now teamed up with our democratic partners for the upcoming US 2020 election.
そしてこの数か月間は、来るべき 2020 年の米大統領選挙に向けて、民主党のパートナーとチームを組んでいます。
2020 年の台湾総選挙の概要
Here is the overview of Taiwan's 2020 general election.
では、2020 年の台湾総選挙の概要についてご紹介します。
From 2018 to 2020, Taiwan has witnessed the growing threat of disinformation to our citizens.
2018 年から 2020 年にかけて、台湾では市民に対する虚偽情報の脅威が増大するという状況に直面しました。
It was observed that many malicious actors utilized social media to disseminate a huge amount of fake news, false information, and even hate speech.
多くの悪質なアクターがソーシャルメディアを悪用し、大量のフェイクニュースや虚偽情報、さらにはヘイトスピーチを拡散していることが観測されました。
According to the Taiwanese government, the disinformation cases have reached the highest number in this 2020 election.
台湾政府によれば、虚偽情報の事例は今回の 2020 年の選挙において最も多かったとのことです。
The Taiwanese Central Election Commission (CEC) stated that they are 128 disimformation cases targeting this election.
台湾中央選挙管理委員会(CEC)は、今回の選挙を対象とした虚偽情報の事例が 128 件あることを明らかにしました。
In addition to the evolution in quantity and tactics, we believe that the dissemination of disinformation did not stop after this election.
量や戦術の進化に加え、今回の総選挙後も虚偽情報の拡散は止まらなかったと弊社では考えています。
虚偽情報はどこからやってきたのか
So, where did the disinformation come from?
では、このような虚偽情報はどこからやってきたのでしょうか?

When we looked at all disinformation cases on the major SNS in Taiwan, such as Facebook, Twitter, YouTube and LINE, we discovered that many of them were started from the Chinese SNS like Weibo and WeChat.
Facebook、Twitter、YouTube、LINE など台湾の主要な SNS において、あらゆる虚偽情報の事例を調査したところ、その多くが微博(Weibo)や微信(WeChat)など中国の SNS に端を発していることが判明しました。
Maybe this is because Taiwan has a historical and cultural relationship with China, which makes the netizens in the 2 regions become highly entangled.
おそらく台湾は中国と歴史的・文化的な関係があるため、両地域のネット市民が複雑に影響を及ぼし合っているからかもしれません。
This is a possible scenario.
このようなことは可能性としてあり得るでしょう。
However, in some cases, we also identify that the contents are directly copied from the official website of Chinese military or they will amplify propaganda made by the Chinese government.
しかし、場合によっては、人民解放軍の公式ウェブサイトから直接コピーされた内容であったり、中国政府によって組織された宣伝活動を増幅させようとしたこと(形跡が存在すること)もわかっています。
Taiwan's polarized political environment and troubled relations with the Chinese government make Taiwan a primary target for China's InfoOps.
台湾の二極化した政治環境と中国政府との関係の悪化によって、台湾は中国の情報操作の重要な対象の一つとなっているのです。
中国はどのように情報操作を展開しているのか
In the following section, we will leave Silvia to talk about the TTPs of China's InfoOp.
次に、中国の情報操作の TTP(戦術、技術、手順)について、Silvia よりご紹介します。
Hello everyone, this is Silvia.
みなさんこんにちは。Silvia です。
Next, I will take you to look into the TTPs of China's InfoOp.
次は、中国の情報操作の TTP について見ていきたいと思います。
TTP is a very frequent term in cybersecurity, it means "Tactics, Techniques and Procedure".
TTP は、サイバーセキュリティの分野でかなり頻繁に使用される用語であり、戦術(Tactics)、技術(Techniques)、手順(Procedure)を意味します。
Due to the time limit, today I will talk about 3 methods used in China's InfoOps, which are the propaganda machine, political content farm and spam botnet, and mobilization of patriotic netizens.
時間の都合上、本日は中国の情報操作で使用される 3 つの手法、宣伝活動機関、政治的コンテンツファームとスパムボットネット、愛国的ネット市民の動員についてのみご紹介します。
宣伝活動機関
To start with, the Chinese propaganda machine has built significant presence over social media platforms in recent years.
まず、近年、中国の宣伝活動機関はソーシャルメディアプラットフォーム上で大きな存在感を示してきました。
The Chinese propaganda machine consists of state media, embassies and diplomats.
中国の宣伝活動機関は国営メディア、大使館、外交官で構成されています。
Studies show that they have spent a lot in advertisement to boost their engagement on social media platforms.
研究によれば、彼らはソーシャルメディアプラットフォームへの関与を高めるため、宣伝広告に多くの労力を費やしてきたことがわかっています。
To name a few, in this June, the United States Justice Department published a report that disclosed state media China Daily has spent about 11 million US dollar on ads in the US newspapers, including the New York Times, Wall Street Journal, Foreign Policy and etc.
一例を挙げると、今年 6 月、米司法省は報告書を発表することで、国営メディアの中国日報が New York Times、Wall Street Journal、Foreign Policy など、米紙の宣伝広告に約 1,100 万ドルを支出していたことを明らかにしました。
And over 260,000 US dollar was spent for advertising over Twitter.
また、Twitter での宣伝広告にも 26 万ドル以上が使用されていました。
So, China's heavy spending on advertisement has boosted their influence in both traditional media environment and social media platforms.
つまり、中国の宣伝広告への多額の支出により、伝統的なメディア環境とソーシャルメディアプラットフォームの両方で彼らの影響力が高まってきているわけです。
So, this result is a very significant number.
この結果は相当に有意な数字です。
Let's look at the world's famous media outlet's followers on Facebook.
世界的に有名なソーシャルメディアである Facebook のフォロワー数をご覧ください。

Currently, China runs five out of six media outlets with the highest number of Facebook followings, which is the CGTN (China Global Television Network), China Daily, People's Daily, Xinhua News and Global Times.
現在、中国は Facebook のフォロワー数が最も多い 6 つのメディアのうち 5 つ(中国環球電視網(CGTN)、中国日報、人民日報、新華社通信、環球時報)を運営しています。
Even the BBC News is behind them.
BBC News でさえ、それらのメディアに遅れをとっています。
The number one on the list, CGTN, which is the English version of CCTV, has over 100 million followers.
リストの 1 位は、中国中央電視台(CCTV)の英語版である中国環球電視網(CGTN)であり、フォロワー数は 1 億人を超えています。
CGTN also ranked the 4th among the most-followed pages of Facebook.
また、中国環球電視網(CGTN)は Facebook において最もフォローされているページにおいて、4 位を占めています。
The stat is really shocking.
この統計は実に衝撃的です。
Because back in 2014, none of the Chinese state media had more than 3 million fans.
なぜなら、2014 年まで遡れば、中国の国営メディアで 300 万人以上のフォロワーを有するメディアは皆無だったからです。
We know that by having a large number of likes, the media can actually look very credible and genuine at first sight.
大量の「いいね!」がつくことで、現にひと目でそのメディアが非常に信頼性が高く、本物らしく見えるのは周知のとおりです。
So, they can cause the audience tend to believe their content, because they have such amount of likes and followers.
閲覧者に彼らのコンテンツを信頼するよう仕向けることができるのは、彼らがこのような大量の「いいね!」やフォロワーを有しているからなのです。
The reason why we have a great concern on Chinese propaganda machine on SNS, is because they have a bad reputation of spreading misinformation and conspiracy theories.
SNS 上で中国の宣伝活動機関に大きな懸念を抱く理由は、彼らが虚偽情報や陰謀論を拡散しているという悪評があるからです。
Since the outbreak of the COVID-19 pandemic, they have put a lot of efforts to establish the image of China as a global savior, instead of a troublemaker.
新型コロナウイルスの爆発的な流行以来、彼らは中国を厄介者としてではなく、世界の救世主としてのイメージを確立するために多くの労力を費やしてきました。

So, you can see the screenshot on the left is Hua Chunying tweeted a video by People's Daily, which showed Italians singing Chinese anthem in Rome.
スライドの左側のスクリーンショットは、ローマでイタリア人が中国の国歌を歌う人民日報の動画を中国外交官の華春瑩氏がツイートしたものです。
That video was labeled as misinformation by fact check center, because the Chinese anthem was actually later edited into the video in the post-production.
その動画がファクトチェックセンターで虚偽情報に分類されたのは、実際は撮影後の編集作業で中国の国歌の部分が後から差し替えられていたためです。
So, on the right hand side, is the Chinese Embassy in Italy.
スライドの右側はイタリアの中国大使館です。
It posted a lot of tweets praising China's donation of mask and supplies to Italy.
中国がイタリアに対してマスクと物資を寄贈したことを称賛するツイートが多数投稿されています。
Yet it was later revealed that those supplies were actually purchased by the Italian government instead of a generous donation.
しかしながら、これらの物資は多額の寄付によるものではなく、実際にはイタリア政府が購入した物資であることが後に明らかになりました。
Not to mention Zhao Lijian, a Chinese diplomat who has been promoting the conspiracy theory of "US army brought the coronavirus to Wuhan".
「米軍が武漢に新型コロナウイルスを持ち込んだ」という陰謀論を後押ししてきた中国外交官の趙立堅氏に至っては言うまでもないでしょう。
政治的コンテンツファームとスパムボットネット
Next, political content farm and spam botnet has become the amplifier of propaganda machine.
次は、政治的コンテンツファームとスパムボットネットが宣伝活動機関の増幅器となっている点です。
In this year, the most popular Western social media platforms including Facebook, Twitter and Google, announced that they have removed hundreds of thousands of fake accounts linked to China.
今年に入り、Facebook、Twitter、Google といった欧米の人気ソーシャルメディアプラットフォームは中国の関与が疑われる数十万件の偽アカウントを削除したと発表しました。
According to Twitter, these pro-China accounts were involved in manipulative and coordinated activities.
Twitter によれば、これら親中派のアカウントは操られていたり組織的な活動に関与していたとのことです。
They spread geopolitical narrative favorable to the Chinese Communist Party and pushed deceptive narrative about political dynamic in Hong Kong.
彼らは中国共産党に有利な地政学的な作り話を拡散し、香港の政治力学に関する虚偽の作り話を後押ししていました。
Even though the platforms are already so dedicated to remove the propaganda network, we still observed a considerable amount of accounts continue to boost the narrative of the Chinese government across the SNS.
すでにソーシャルメディアプラットフォームは本気で宣伝活動ネットワークを削除しているにもかかわらず、SNS 上ではまだ相当量のアカウントが中国政府の虚構を後押しし続けていることが観測されています。
So, here I will show you an example of how the spam botnet and content farm amplified the content of Chinese state media.
ここで、スパムボットネットとコンテンツファームが中国の国営メディアのコンテンツを増幅させている例をご紹介しましょう。
One of the main themes in the Chinese propaganda is attacking the Trump administration.
中国の宣伝活動の主要なテーマの一つは、トランプ政権への攻撃です。
So, on August 15th, Xinhua News posted an article titled "Politicization of COVID-19 Gets U.S. Trapped in Deep Trouble".
8 月 15 日に新華社通信は「“政治化”操弄令美国深陷疫情困境」と題した記事を掲載しました。

You can see the highlighted sentences in the article was later become the material for spam botnet and content farm.
記事中で強調された文章は、後にスパムボットネットやコンテンツファームの素材になったことがわかります。

On August 16th, the article was first copied and shared by a notorious Chinese content farm called KKnews (Meiri toutiao, 每日頭條).
8 月 16 日にまずこの記事がコピーされ、「每日頭條」(KKnews)という悪名高い中国のコンテンツファームで共有されました。
And then, the text from the article was spread across Facebook and Twitter via spamming accounts.
そして、この記事の文章がスパムアカウントを経由して Facebook や Twitter に拡散されました。
We found that this account shows strong signs of automatic behavior, because they simultaneously posted numerous identical contents on a daily basis.
このアカウントが自動化された振る舞いという点で強い兆候を示していることに気づいたのは、毎日のように非常に多くの同一コンテンツを一斉に投稿していたからです。
And their content are mostly copied from Chinese state media and Chinese SNS, such as Weibo.
その内容はほとんどが中国の国営メディアや微博(Weibo)のような中国の SNS からコピーされたものでした。
Also, we observed that some of the accounts in the botnets used mugshots as profile pictures.
また、ボットネット内のアカウントの中には、プロフィール画像として顔写真を使用しているものも観測されています。
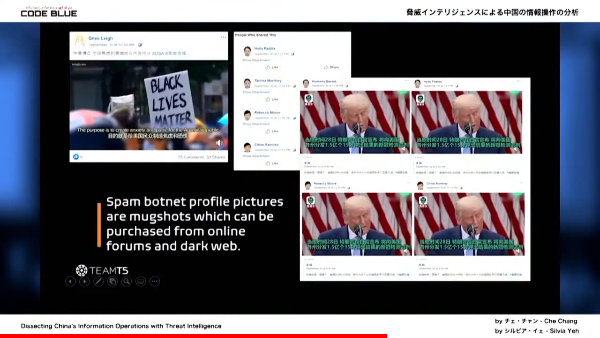
These mugshots are often available on online forums and dark web.
これらの顔写真はオンラインフォーラムやダークウェブでもよく見かけます。
So from the screenshot, you can see the spam botnet simultaneously share videos that criticize the crop the Trump administration, emphasizing the incompetence of the US government to handle the pandemic.
スクリーンショットからは、スパムボットネットがトランプ政権を批判する動画を一斉に共有し、新型コロナウイルスの爆発的な流行に対処する米国政府が無能であると強調していることがわかります。
You can see the spam botnet that use mugshots as profile picture, and more importantly, their user name were made to look like US citizens, such as Harmony Becket, Holly Padilla, Rebecca Moore, Chloe Ramirez, etc.
プロフィール画像に顔写真を使用しているスパムボットネットがおわかりいただけるかと思いますが、さらに重要なのは、ハーモニー・ベケット(Harmony Becket)、ホリー・パディラ(Holly Padilla)、レベッカ・ムーア(Rebecca Moore)、クロエ・ラミレス(Chloe Ramirez)など、米国市民と思わせるようなユーザー名がつけられていることです。
So, we also spotted some cross-platform activities.
また、クロスプラットフォームでの活動もいくつか観測されました。
Here is the screenshot of botnet spamming a video that accuses Trump of dictatorship on YouTube, Facebook, and Twitter.
こちらは YouTube、Facebook、Twitter 上でトランプ氏の独裁を非難する動画を大量に送信するボットネットのスクリーンショットです。
You can see that the video content, and the caption are 100% identical.
動画の内容とキャプションが完全に一致していることがわかるかと思います。

And again, our investigation found that the source of content was from China Xiaokang.com, which is a national news site controlled by a party media outlet.
さらに弊社の調査で、コンテンツの情報源が共産党系メディアの支局が管轄する国営ニュースサイトの「中国小康網」からであることが明らかとなりました。
This shows that not only do this spam botnets spread text and images, but they also disseminate video content.
このことは当該のスパムボットネットが文章や画像を拡散するだけでなく、動画コンテンツも拡散していることを示しています。
And this is harder for the authorities and researchers to detect the disinformation campaign.
このような手法が、政府機関や研究者が虚偽情報に係る組織活動を見抜くことを難しくしています。
愛国的ネット市民の動員
The next one is the mobilization of patriotic netizens.
次に、愛国的ネット市民の動員です。
Patriotic netizens, also known as the little pink, are notorious for launching trolling campaigns against foreign online users, where they feel China is being attacked by biased reporting.
「小粉紅(Little Pink)」とも呼ばれる愛国的ネット市民は偏向した報道によって中国が攻撃されていると感じ、外国のネットユーザーに対して組織的な荒らし行為を展開することで悪名を馳せています。
The Chinese authorities have recognized the power of the patriotic netizens.
中国の政府機関(当局)は愛国的ネット市民の力を認めています。
Sometimes the regime will deliberately mobilize them to attack dissidents.
時には政権が意図的に彼らを動員して反体制派を攻撃することもあります。

So last year, they have mobilized the patriotic netizens to launch a doxing campaign against the Hong Kong protesters.
昨年は愛国的ネット市民を動員し、香港の抗議者に対する組織的な Doxing(個人情報の暴露)活動を展開していました。
For your information, doxing is the action to search for and publish private information about a particular individual on the internet, typically with malicious intent.
ちなみに「Doxing(人肉搜索,晒し)」とは特定の個人に関する個人情報をインターネット上で検索して公開する行為であり、通常は悪意をもって行われます。
So, the context is in late August, there was an anonymous website that disclosed personal details of the Hong Kong protesters.
その背景として、8 月下旬に、香港の抗議者の個人情報を公開している匿名サイトがありました。
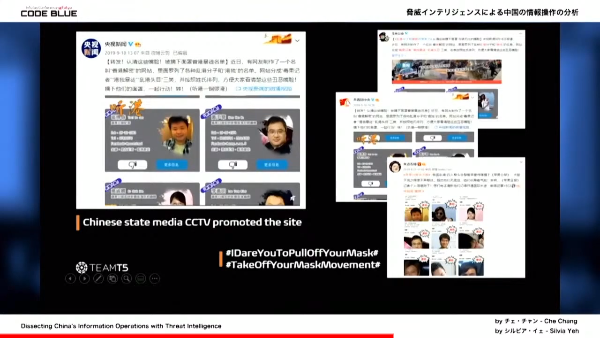
So, on the right hand side is the screenshot of the website.
スライドの右側にあるのが、そのウェブサイトのスクリーンショットです。
The website describes the protesters as troublemakers and foreign agents aiming to destroy Hong Kong's stability.
このウェブサイトでは、抗議者のことを香港の安定を破壊することを目的とした厄介者または外国の工作員であると説明しています。
Later, in mid-September, the Chinese state media, led by CCTV, posted a video on Weibo to promote the website.
その後、9 月中旬には中国中央電視台(CCTV)を中心とした中国国営メディアが微博(Weibo)に動画を投稿し、このウェブサイトの宣伝を行いました。
And then, the posts by CCTV was widely shared and promoted by official accounts of the Chinese authorities.
そして、中国中央電視台の投稿は中国の政府機関の公式アカウントによって広く共有され、宣伝されました。
Eventually, they successfully inflamed the patriotic Chinese netizens.
最終的に彼らは首尾よく中国の愛国的ネット市民を扇動したわけです。
Many netizens have joined the narrative and demanded those protesters to reveal their true identity.
多くのネット市民がこの虚構に加担し、抗議者たちに正体を明らかにするよう要求しました。
They launched several hashtag campaigns on Weibo, such as "I dare you to pull off your mask" and "Take off your mask movement".
彼らは微博(Weibo)上で「#有本事摘口罩」(マスクをとる勇気もないのか)や「#全民摘口罩运动」といったハッシュタグキャンペーンを何度も展開しました。
This has posed a great threat to the protesters, because if they are identified, they could face unlawful punishment from the Chinese government.
この活動が抗議者にとって大きな脅威となったのは、身元が特定された場合、中国政府から不当な処罰を受ける可能性があったからです。
TeamT5 calls this unique and organizational mechanism as "digital propaganda formula" which is made up of 4 key components.
弊社では、この独自かつ組織的なメカニズムを「デジタルプロパガンダ(宣伝活動)方式」と呼んでおり、それは 4 つの重要な要素で構成されています。

Namely, state media, governmental affairs new media, communist youth league, and trolling army.
4 つの要素とは、国営メディア、政府系の新興メディア、共産党青年団、ネット世論操作部隊を指します。
We believe the regime has used this formula to influence and mobilize the country's netizens when they want to shape the online discourse in favor of China.
中国政府は中国に有利になるようネット世論を形成したい時、この方式を利用して国内のネット市民に働きかけ、動員しているものと考えられます。
One notable example is the cross-strait online disputes in 2016.
特筆すべき例として、2016 年に起きた中台(中国・台湾)間のネット論争が挙げられます。
That was the time when pro-democracy Tsai Ing-wen (Cai Yingwen, 蔡英文) was elected, and the Chinese patriotic netizens were mobilized to challenge Taiwan's election result.
それはちょうど親民主派の蔡英文が(大統領に)当選した時のことであり、台湾の選挙結果に異議を唱えようと中国の愛国的ネット市民が動員されました。
You may think the above mentioned cases are serious enough.
上記のケースだけでも十分に深刻だと思われるかもしれません。
However, the situation can get worse when hackers enter the InfoOp threat landscape.
しかしながら、ハッカーたちが情報操作における危険な状況に介入した場合、事態はさらに悪化する可能性があります。
And we call it an APT + InfoOp attack model.
これを弊社では「APT + InfoOp(情報操作)」の攻撃モデルと呼んでいます。

Advanced Persistent Threat, APT actors, are typically state-sponsored hacker groups.
一般的に、APT(持続的標的型攻撃)アクターは国家が支援するハッカーグループです。
They usually conduct prolonged and targeted cyber attacks to steal highly sensitive data.
通常、彼らは機密性の高い情報を盗み出すために、長期間にわたる標的型サイバー攻撃を行います。
However, in mid-July 2020, we identify an InfoOp that can be linked to a notorious Chinese APT group.
その一方で、2020 年 7 月中旬には、悪名高い中国の APT グループの関与が疑われる情報操作が存在したことがわかっています。
We dub the InfoOp as "Operation Juiker", because the threat actors had disseminated disinformation about "Juiker", which is a messaging app developed by Taiwan's research institute.
弊社がこの情報操作を「Operation Juiker」(Juiker 作戦)と命名したのは、台湾の研究機関が開発したメッセージングアプリ「Juiker」(揪科,ジューカー)に関して、脅威アクターが虚偽情報を拡散したからです。
The app is also widely used by government units.
このアプリは行政機関でも広く利用されています。
So, the actor claimed the Juiker app and the research institute were hacked, and many confidential data about military unit were exposed.
脅威アクターはこの「Juiker」というアプリや(アプリを開発した)研究機関がハッキングされ、軍事機関に関する機密情報が大量に漏えいしたと主張しました。
Operation Juiker took place on PTT, which is a popular, Reddit-like forum in Taiwan.
「Operation Juiker」は台湾で人気のある PTT(批踢踢)という Reddit のようなフォーラムにおいて行われました。
PTT has a special feature.
PTT には特別な機能があります。
The forum will display the IP address of the author of a post.
PTT のフォーラムでは投稿者の IP アドレスが表示されます。
We found that the actors had controled about 20 Taiwanese IPs and 50 PTT accounts to spread the disinformation.
弊社は脅威アクターが台湾の約 20 の IP アドレスと 50 の PTT アカウントを操作して虚偽情報を拡散していたことを突き止めました。
Many of the account's owners had later claimed that they have never posted articles about Juiker.
後に、このアカウントの所有者の大半がこれまで「Juiker」に関する記事を投稿したことはないと主張しました。
What's noteworthy is that we conducted an investigation to cross reference the IP address in this operation with our database and we found one of the IPs overlaps the C2 servers of a Chinese state-sponsored APT group which we have tracked for years.
注目すべきは、「Operation Juiker」で使用された IP アドレスと弊社のデータベースとを突き合わせて調査したところ、IP アドレスのうちの 1 つが何年も追跡してきた中国が支援する APT グループの C&C サーバーと一致することを突き止めたことです。
So the model, we think the model is more sophisticated, because a typical hack-and-leak operation is just a well-timed dump of stolen data.
弊社はその攻撃モデルはより洗練されていると考えています。なぜなら、(従来の)典型的な「hack-and-leak operation」(ハッキングによる情報漏洩)はタイミングよく大量のデータを窃取するだけですが…
Yet, APT + InfoOp could involve targeted social media campaigns disseminating disinformation based on highly confidential data.
これに対し、「APT + InfoOp」の攻撃モデルは、標的とされた組織的なソーシャルメディア活動を巻き込みながら、機密性の高い情報を模倣した虚偽情報を拡散することができるからです。
Such situation is super tricky for government units and fact-check centers and it could pose a great risk of national security.
このような状況は、政府機関やファクトチェックセンターにとって非常に厄介であり、国家の安全保障にも大きなリスクをもたらす可能性があります。
So, we think it is more crucial than ever to adopt threat intelligence solutions to combat the issue.
そのため、この問題に対処するために脅威インテリジェンスによる課題解決を採用することは、これまで以上に重要であると考えています。
Our research has shown that these actor will keep evolving and changing their tactics over times.
弊社の調査によれば、これらの脅威アクターは年代(世代)を超えて進化し続け、戦術を変化させていくことがわかっています。
With knowledge in cybersecurity and the ecosystem of SNS, we believe our threat intelligence can provide instant insight into actor methodology and exposes potential risks.
サイバーセキュリティと SNS における生態系に精通することで、私たちの脅威インテリジェンスが脅威アクターの手口を速やかに把握し、潜在的なリスクを顕在化させることができると信じています。
おわりに
This year, we have published a series of white papers on Information Operation.
今年、弊社は情報操作に関する一連の白書を発行してきました。

If you are interested in our research on InfoOp, you can go to our official website to request for a copy.
情報操作の調査結果にご興味のある方は、弊社の公式ウェブサイトへアクセスして資料請求をご依頼ください。
So, that's all for today.
本日はここまでとなります。
Thanks for listening.
ご清聴ありがとうございました。
Thanks for your attention.
ご関心をお寄せいただき、ありがとうございます。
We hope this talk can help provide some ideas to combat the issue.
本講演が当該の問題に対抗するアイデアを提供するための一助となることを願っています。
Here comes a short Q&A session.
それでは質疑応答に移ります。