概要
- GitHub ActionsでAWS ACEESKEYをGitHub側(GitHubSecrets)に保存したくない
- OpenID Connect経由の各種Cloud Providerの認証がとれる
- 認証をパスする事が目的なのでポリシーなど細かい要素は後回しにしてシンプルにトライ
- とりあえず習うより慣れろで
前提
- OpenID Connect Provider認証の仕組みについて理解している
- IAMのAssumeRoleの仕組みについて理解している
- GitHubSecretsの利便性とリスクについて理解している
詳細
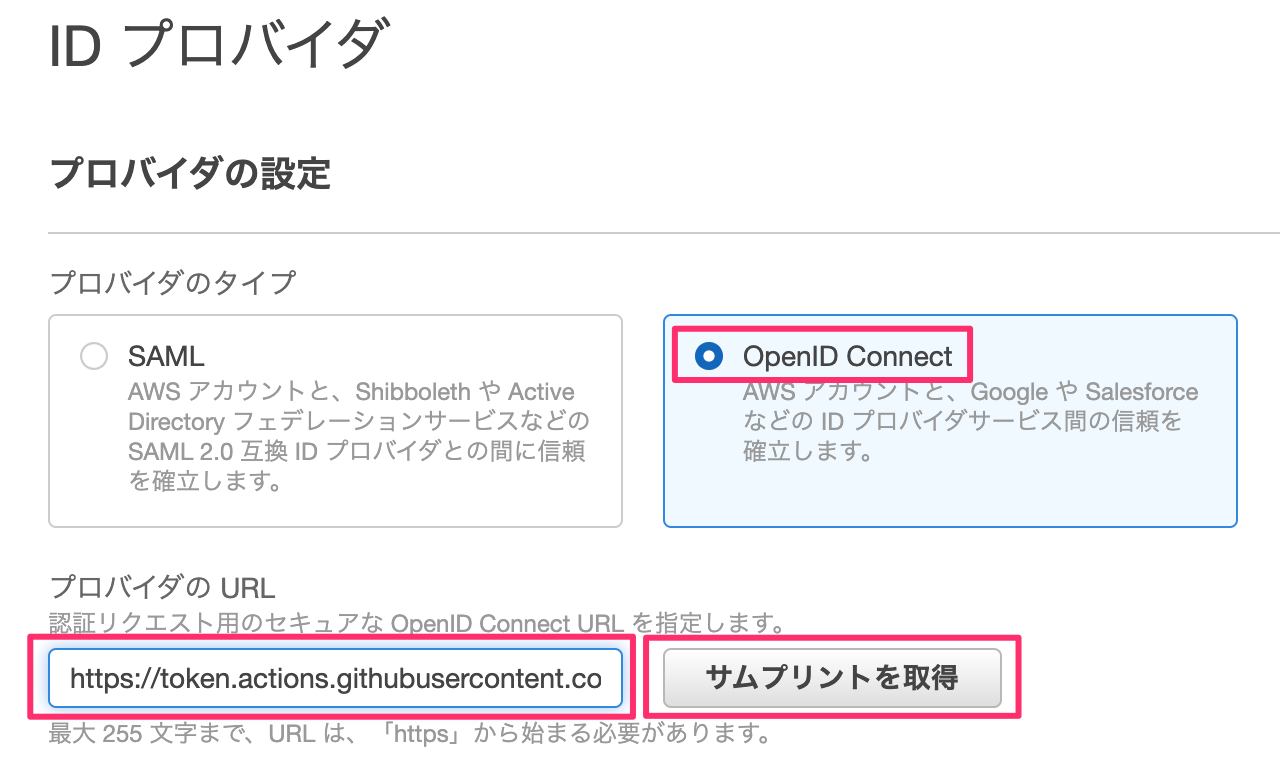
OpenIDプロバイダを作成
-
プロバイダのタイプ: OpenID Connect
-
プロバイダの URL: https://token.actions.githubusercontent.com
-
対象者: sts.amazonaws.com
-
AWSのIAMからIDプロバイダを作成する






ロールの割当
- "ロールの割当"→"新しいロールを作成"


テスト用ロールの作成
- ウェブアイデンティティで作成
- Audienceは"sts.amazonaws.com "




GitHub側準備
- テスト用リポジトリを用意する
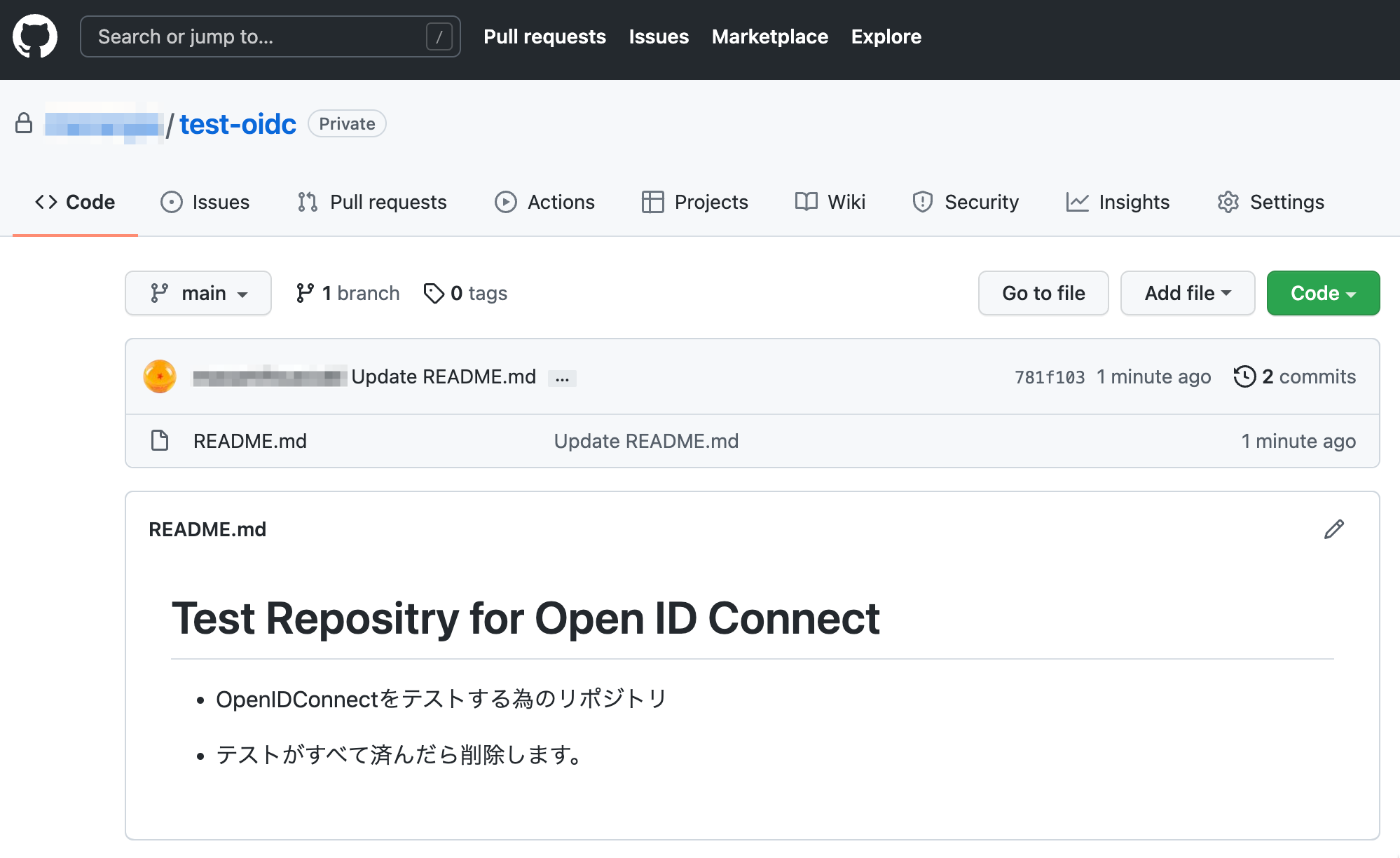
- workflowのフォルダとファイルを作成
$ git clone https://github.com/menergia/test-oidc
$ mkdir -p test-oidc/.github/workflows
$ echo "### oidc test workflow ###" > test-oidc/.github/workflows/test-oidc-ci.yml
$ cd test-oidc
$ git add .
$ git commit -m "add blank workflow"
$ git push origin main
GitHubActions用workflowファイルを作成
- アカウントIDをメモ・控えておく
- test-oidc-ci.ymlを編集
- GitHub公式ドキュメントのworkflowサンプルを参考
- permissions: id-token: write
test-oidc-ci.yml
### oidc test workflow ###
name: OIDC test
on:
push:
jobs:
build:
runs-on: ubuntu-latest
permissions:
id-token: write
contents: read
steps:
- name: Set up environment
run: |
export AWS_ROLE_ARN=arn:aws:iam::39********81:role/Role-GithubActions-OpenIDConnect-Test
export AWS_WEB_IDENTITY_TOKEN_FILE=/tmp/aws-credential
export AWS_DEFAULT_REGION=ap-northeast-1
echo AWS_WEB_IDENTITY_TOKEN_FILE=$AWS_WEB_IDENTITY_TOKEN_FILE >> $GITHUB_ENV
echo AWS_ROLE_ARN=$AWS_ROLE_ARN >> $GITHUB_ENV
echo AWS_DEFAULT_REGION=$AWS_DEFAULT_REGION >> $GITHUB_ENV
curl -H "Authorization: bearer $ACTIONS_ID_TOKEN_REQUEST_TOKEN" "$ACTIONS_ID_TOKEN_REQUEST_URL&audience=sts.amazonaws.com" | jq -r '.value' > $AWS_WEB_IDENTITY_TOKEN_FILE
- run: aws sts get-caller-identity
- commit/push後actionsタブを確認
- CI上でOpenIDConnectが成功している

残課題
- このあとは必要なポリシー・ロールを正しく設定してトライして見る