前置き
今週の月曜日に、以下の内容をQittaに投稿して、皆さんと共有しました。
割りとたくさんの方々に上記の投稿を見ていただいて、非常に嬉しいと思います。今後も、自分なりにDeepDiveして、得られた情報を皆さんに共有しますので、少しでもお役に立てれば嬉しいと思います。
概要
前回の投稿では、下記の図に示す通りに、管理される側のConfig Rulesが管理する側のLambdaを呼び出して、管理される側のCloudTrailの設定を監査できることを検証してみました。
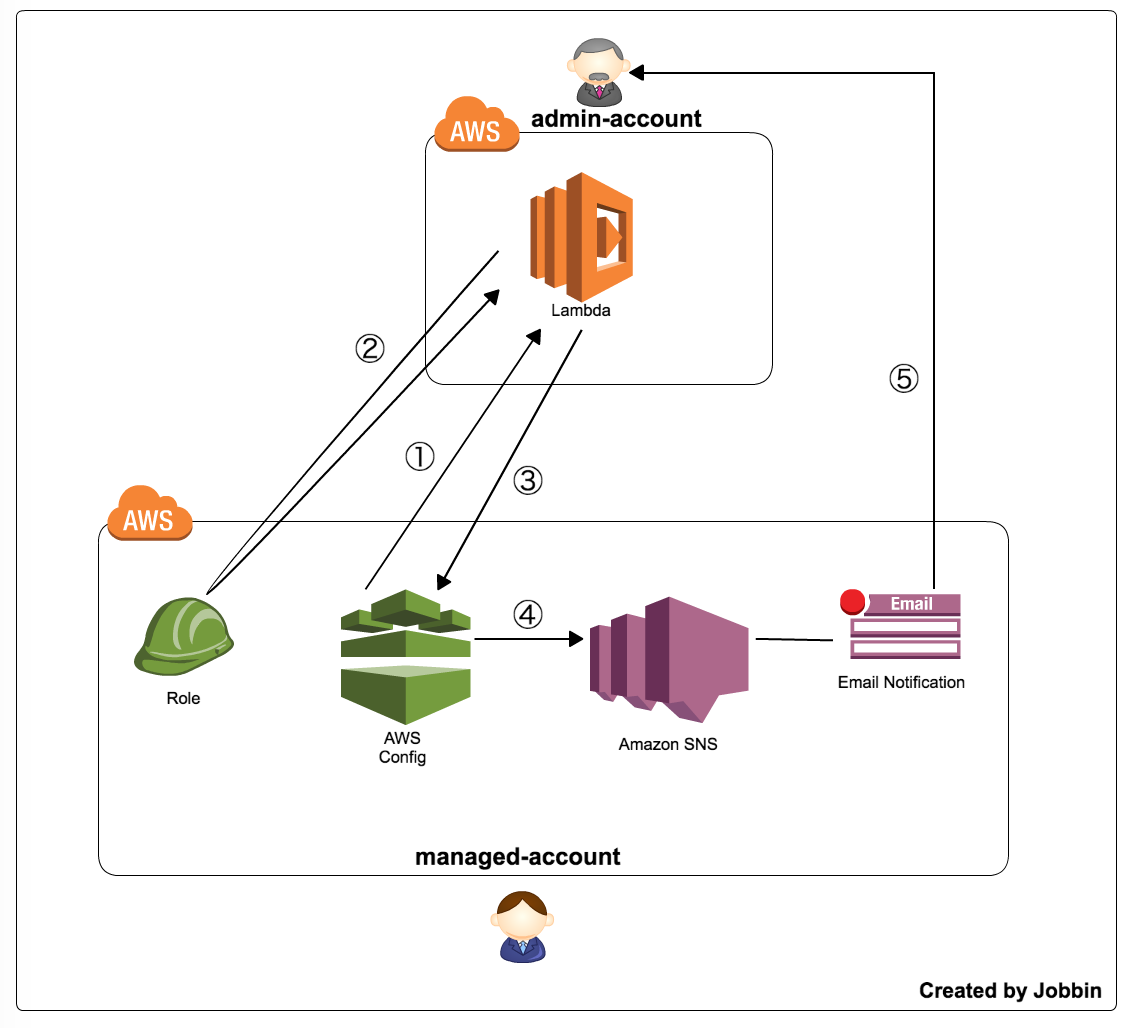
今回は、① ~ ⑤の間に、どんなデータを利用されているかを皆さんに共有しようと思います。
データ編
Config → Lambda ( ① )
Configから Lambdaに渡される情報 → event
{
"version": "1.0",
"invokingEvent": "{
\"configurationItemDiff\":{},
\"configurationItem\":{
\"configurationItemVersion\":\"1.2\",
\"relatedEvents\":[\"a46a2a05-b61d-4e01-903c-c396001b6150\"],
\"relationships\":[],
\"configuration\":{},
\"supplementaryConfiguration\":{},
\"tags\":{},
\"configurationItemCaptureTime\":\"2016-07-14T14:12:56.439Z\",
\"configurationStateId\":43,
\"awsAccountId\":\"**********\",
\"configurationItemStatus\":\"OK\",
\"resourceType\":\"AWS::CloudTrail::Trail\",
\"resourceId\":\"Cloud-Trail\",
\"resourceName\":null,
\"ARN\":\"arn:aws:cloudtrail:us-east-1:**********:trail/Cloud-Trail\",
\"awsRegion\":\"us-east-1\",
\"availabilityZone\":\"Regional\",
\"configurationStateMd5Hash\":\"86e1f7bf6caa764267a918a160086d79\",
\"resourceCreationTime\":null
},
\"notificationCreationTime\":\"2016-07-14T14:12:56.553Z\",
\"messageType\":\"ConfigurationItemChangeNotification\",
\"recordVersion\":\"1.2\"
}",
"ruleParameters": "{\"executionRole\":\"arn:aws:iam::**********:role/config-rules-admin\"}",
"resultToken": "**********",
"eventLeftScope": false,
"executionRoleArn": "arn:aws:iam::**********:role/config-role",
"configRuleArn": "arn:aws:config:us-east-1:**********:config-rule/config-rule-asdspc",
"configRuleName": "CloudTrail-LogValidation-Enabled",
"configRuleId": "config-rule-asdspc",
"accountId": "**********"
}
Lambda → Config ( ② )
LambdaがAssumeRole時の一時的なクレデンシャル情報
{
"expired": true,
"expireTime": null,
"masterCredentials": {
"expired": false,
"expireTime": null,
"accessKeyId": "ASI*****HVNBBA",
"sessionToken": "***************"
"envPrefix": "AWS"
},
"params": {
"RoleArn": "arn:aws:iam::********:role/config-rules-admin",
"RoleSessionName": "temporary-credentials"
}
}
Lambdaから Configに渡される評価結果 → putEvaluationsRequest
{
"Evaluations": [
{
"ComplianceResourceType": "AWS::CloudTrail::Trail",
"ComplianceResourceId": "Cloud-Trail",
"ComplianceType": "NON_COMPLIANT / COMPLIANT",
"OrderingTimestamp": "2016-07-14T14:12:56.439Z"
}
],
"ResultToken": "**********"
}
SNS ( ④と⑤ )
CloudTrailに対する監査レポート情報
- [AWS Config:Region] AWS::CloudTrail::Trail Name is NON_COMPLIANT with Config Rule Name
- [AWS Config:Region] AWS::CloudTrail::Trail Name is COMPLIANT with Config Rule Name
上記2種類の情報をまとめると、以下になります。
{
"awsAccountId": "",
"configRuleName": "",
"configRuleARN": "arn:aws:config:*********:config-rule/config-rule-asdspc",
"resourceType": "AWS::CloudTrail::Trail",
"resourceId": "Cloud-Trail",
"awsRegion": "us-east-1",
"newEvaluationResult": {
"evaluationResultIdentifier": {
"evaluationResultQualifier": {
"configRuleName": "CloudTrail-LogValidation-Enabled",
"resourceType": "AWS::CloudTrail::Trail",
"resourceId": "Cloud-Trail"
},
"orderingTimestamp": ""
},
"complianceType": "COMPLIANT / NON_COMPLIANT",
"resultRecordedTime": "2016-07-10T14:36:46.619Z",
"configRuleInvokedTime": "2016-07-10T14:36:44.212Z",
"annotation": null,
"resultToken": null
},
"oldEvaluationResult": {},
"notificationCreationTime": "2016-07-10T13:32:30.059Z",
"messageType": "ComplianceChangeNotification",
"recordVersion": "1.0"
}
- [AWS Config:Region] AWS::CloudTrail::Trail Name is Updated in Account Account-ID
{
"configurationItemDiff": {
"changedProperties": {
"Configuration.LogFileValidationEnabled": {
"previousValue": false,
"updatedValue": true,
"changeType": "UPDATE"
}
},
"changeType": "UPDATE"
},
"configurationItem": {
"configurationItemVersion": "1.2",
"relatedEvents": [
"0dfe96fa-3fdd-493d-a558-1247d3bc6495"
],
"relationships": [],
"configuration": {
"name": "Cloud-Trail",
"s3BucketName": "******",
"s3KeyPrefix": null,
"snsTopicName": null,
"includeGlobalServiceEvents": true,
"isMultiRegionTrail": true,
"homeRegion": "us-east-1",
"trailARN": "arn:aws:cloudtrail:us-east-1:*********:trail/Cloud-Trail",
"logFileValidationEnabled": true,
"cloudWatchLogsLogGroupArn": null,
"cloudWatchLogsRoleArn": null,
"kmsKeyId": null
},
"supplementaryConfiguration": {},
"tags": {},
"configurationItemCaptureTime": "2016-07-10T10:36:46.701Z",
"configurationStateId": 20,
"awsAccountId": "*********",
"configurationItemStatus": "OK",
"resourceType": "AWS::CloudTrail::Trail",
"resourceId": "Cloud-Trail",
"resourceName": null,
"ARN": "arn:aws:cloudtrail:us-east-1:*********:trail/Cloud-Trail",
"awsRegion": "us-east-1",
"availabilityZone": "Regional",
"configurationStateMd5Hash": "fe86053064517dc0c824e900db241935",
"resourceCreationTime": null
},
"notificationCreationTime": "2016-07-10T10:36:46.799Z",
"messageType": "ConfigurationItemChangeNotification",
"recordVersion": "1.2"
}
Config Configuration(バックアップ用)まわり
- [AWS Config:Region] Configuration Snapshot Delivery Started for Account Account-ID
{
"configSnapshotId": "",
"notificationCreationTime": "",
"messageType": "ConfigurationSnapshotDeliveryStarted",
"recordVersion": ""
}
- [AWS Config:Region] Configuration Snapshot Delivery Completed for Account Account-ID
{
"configSnapshotId": "",
"s3ObjectKey": "",
"s3Bucket": "",
"notificationCreationTime": "",
"messageType": "ConfigurationSnapshotDeliveryCompleted",
"recordVersion": ""
}
- [AWS Config:Region] Configuration History Delivery Completed for Account Account-ID
{
"s3ObjectKey": "",
"s3Bucket": "",
"notificationCreationTime": "",
"messageType": "ConfigurationHistoryDeliveryCompleted",
"recordVersion": ""
}
まとめ
① ~ ⑤の間に使われているデータを簡単に整理して、データの種類・構造などを皆さんに共有しました。これらのデータを確認することによって、下記の投稿に書かれている検証の仕組みと流れを理解するにお役に立てれば嬉しいです。
[ AWSセキュリティ担当者必見] Config Rules 、Lambda、SNSによる中央集権型の管理統制について